SCAP & STIG Workshop - Student Workbook
A presentation at Defense in Depth 2014 in in Herndon, VA 20170, USA by Shawn Wells

SCAP & STIG Workshop 30 July 2014 http://defenseindepth2014.org Page 1 of 42
Table of Contents 1 INTRODUCTION………………………………………………………………………………………………………………………………. 4 2 SCAP SECURITY GUIDE PROJECT………………………………………………………………………………………………. 5 2.1 Background………………………………………………………………………………………………………………………………. 5 2.2 Project Charter………………………………………………………………………………………………………………………… 5 2.3 Installation……………………………………………………………………………………………………………………………….. 6 3 UNDERSTANDING THE COMPONENTS………………………………………………………………………………………. 7 3.1 Alphabet Soup Explained……………………………………………………………………………………………………….. 7 3.2 Content Location……………………………………………………………………………………………………………………. 7 3.3 OpenSCAP……………………………………………………………………………………………………………………………….. 7 3.4 XCCDF………………………………………………………………………………………………………………………………………. 8 3.4.1 Sample XCCDF Code……………………………………………………………………………………………………….. 9 3.4.2 Profles……………………………………………………………………………………………………………………………. 10 3.5 OVAL……………………………………………………………………………………………………………………………………….. 12 4 OPERATION……………………………………………………………………………………………………………………………………. 13 4.1 XCCDF Validation…………………………………………………………………………………………………………………… 13 4.2 Generate HTML Guide………………………………………………………………………………………………………….. 14 4.3 Performing a Scan…………………………………………………………………………………………………………………. 15 4.4 Interpreting Results……………………………………………………………………………………………………………… 16 4.4.1 HTML……………………………………………………………………………………………………………………………….. 16 4.4.2 XML…………………………………………………………………………………………………………………………………. 18 4.5 Remediation…………………………………………………………………………………………………………………………. 20 4.5.1Remediation? How Do?………………………………………………………………………………………………… 20 4.6 Scanning Automation…………………………………………………………………………………………………………… 22 4.7 Alternative Tools…………………………………………………………………………………………………………………… 23 4.7.1 SPAWAR SCAP Compliance Checker (SPAWAR SCC)…………………………………………….23 4.7.2 Red Hat Network Satellite………………………………………………………………………………………….. 23 5 CONTENT CUSTOMIZATION………………………………………………………………………………………………………. 24 5.1 So, You Wanna Be a Developer?………………………………………………………………………………………… 24 5.2 Cloning the Source………………………………………………………………………………………………………………. 25 5.3 Understanding the Code Tree……………………………………………………………………………………………. 26 5.4 Creating your frst XCCDF rule………………………………………………………………………………………….. 29 5.5 OVAL Authoring…………………………………………………………………………………………………………………… 35 5.6 Profles…………………………………………………………………………………………………………………………………… 38 5.7 Patch Creation & Submission…………………………………………………………………………………………….. 40 6 REFERENCES………………………………………………………………………………………………………………………………… 42 Page 2 of 42
Illustration Index Illustration 1: HTML Results Output: Target Information……………………………………………………………19 Illustration 2: HTML Results Output: Rule Results Summary…………………………………………………….19 Illustration 3: HTML Results Output: Rule Results Table…………………………………………………………..20 Illustration 4: HTML Results Output: Rule Detail…………………………………………………………………………20 Illustration 5: Sample SCAP Integration for RHN Satellite 5.5………………………………………………….27 Illustration 6: Sample must_install_ssg XCCDF Rule…………………………………………………………………..37 Illustration 7: Customized Table of Contents………………………………………………………………………………. 38 Illustration 8: XCCDF with XHTML <pre> Tags…………………………………………………………………………….39 Illustration 9: Updated XCCDF HTML Output……………………………………………………………………………… 40 Illustration 10: package_scap-security-guide_installed.xml……………………………………………………..42 Illustration 11: stig-rhel6-server.xml…………………………………………………………………………………………….. 45 Illustration 12: package_scap-security-guide_installed XCCDF Profle Rule………………………….46 Illustration 13: package_scap-security-guide_installed Patch Submission…………………………….48 Index of Tables Table 1: XCCDF Rule Elements………………………………………………………………………………………………………… 12 Table 2: Scan Results XML Output………………………………………………………………………………………………… 23 Table 3: SSG Code Tree: RHEL6/…………………………………………………………………………………………………… 33 Table 4: XCCDF Profle Tags………………………………………………………………………………………………………….. 45 Page 3 of 42

1 INTRODUCTION This workshop is intended to assist you in developing familiarity with, and skill in, the installation and customization of SCAP content for Red Hat Enterprise Linux, utilizing the DISA STIG baseline. Upon completion of this workshop, you should be able to return to your shop, obtain the SCAP components from Red Hat and DISA FSO, and be able to perform highly automated STIG scanning and reporting. Each attendee will be given a virtual machine to use for this workshop. The hostnames follow the syntax of: studentX.lab.ssgproject.org The initial login will be studentX, with a password of “redhat2014.” Use sudo to escalate to root as needed. This workshop has been designed to be delivered over a two hour period, with each chapter building upon the prior. Should you have any questions, please raise your hand and the instructors will be happy to assist. Page 4 of 42
2 SCAP SECURITY GUIDE PROJECT The scap-security-guide project (SSG) delivers security guidance, baselines, and associated validation mechanisms using the Security Content Automation Protocol (SCAP). We currently provide content for Red Hat Enterprise Linux 6 (RHEL6) and JBoss Enterprise Application Server 5 (JBoss EAP5), as well as Fedora. Additionally, work has recently started toward developing content for RHEL7. The SSG project aspires to bridge the gap between generalized policy and specifc implementation guidance, in SCAP formats to support automation whenever possible. The project homepage is https://fedorahosted.org/scap-security-guide/ 2.1 Background Security guidance documents, such as the NSA RHEL5 SNAC Guide, have historically been authored in archaic static formats such as PDF fles. This left much to be desired, particularly around automation, and individual shops were forced to create their own scripted hardening processes. These processes were authored in their own silos, by unique contractor teams, generally not shared across programs, and caused gross waste of tax payer dollars. Additionally, from a vendor perspective, supporting hardened environments was commercially unfeasible. As each shop held it’s own processes, how could the vendor know what was changed and how to support it? The system was broke. In May 2011, the Information Assurance Directorate of the National Security Agency (NSA IAD) invited Red Hat to begin collaboration on high quality security guidance for Red Hat Enterprise Linux 6. It was decided the content would be authored in SCAP formats to support automation, and thus the SCAP Security Guide project was born. Development of security guidance continued through May 2012, at which point Red Hat and NSA IAD contacted DISA Field Security Operations (DISA FSO) to begin development of the Red Hat Enterprise Linux 6 STIG. For the frst time, content development of a STIG would be open sourced. The movement towards transparent collaboration – between government agencies, industrial base partners, and content consumers – further refects acceptance by the NSA and DISA FSO of the benefts of open source development models. On February 12 th, 2013, DISA FSO released the frst public draft RHEL6 STIG - derived from the upstream SCAP Security Guide project. This community powered innovation model has allowed the rapid creation of security baselines at dramatically reduced costs, shortened timeframes, and has produced higherquality content that has now become offcial U.S. Government security baselines. Page 5 of 42
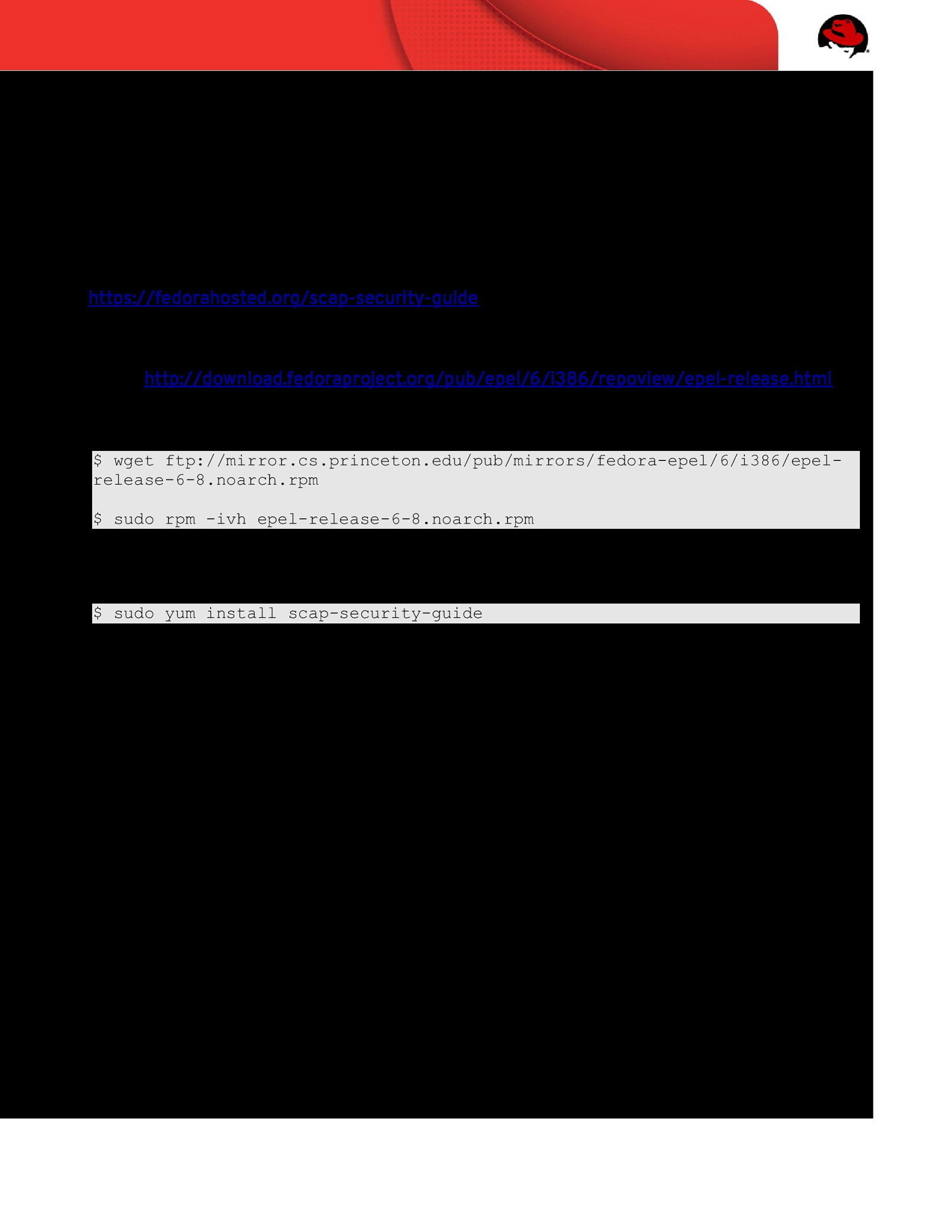
2.2 Project Charter The SSG community has a single goal: Develop usable security baselines across all Red Hat technology areas. Patches welcome! 2.3 Installation This workshop assumes you have access to a RHEL6 machine. Please note that the latest download instructions will always be found at the SSG homepage, located here: https://fedorahosted.org/scap-security-guide 1. To enable the EPEL repository, you must download latest epel-release RPM. The latest RPM URL can be found at http://download.fedoraproject.org/pub/epel/6/i386/repoview/epel-release.html. At the time of writing, the latest RPM can be downloaded via the following command: $ wget ftp://mirror.cs.princeton.edu/pub/mirrors/fedora-epel/6/i386/epelrelease-6-8.noarch.rpm $ sudo rpm -ivh epel-release-6-8.noarch.rpm 2. Next, install SSG via yum: $ sudo yum install scap-security-guide Please note this may pull down other dependencies, such as the OpenSCAP tooling, if they are not part of your current baseline. Page 6 of 42
3 UNDERSTANDING THE COMPONENTS 3.1 Alphabet Soup Explained SCAP content is made of many components with a variety of acronyms attached to them. • XCCDF: eXtensible Confguration Checklist Description • OVAL: Open Vulnerability Assessment Language • CPE: Common Platform Enumerator • CCE: Common Confguration Enumerator 3.2 Content Location On RHEL6, SCAP content is stored under /usr/share/xml/scap/ with each content provider responsible for creating their own subdirectories. The SSG project deploys content into /usr/share/xml/scap/ssg/ with the following sub directory: • content/ Houses SCAP content utilizing the following naming conventions: • CPE Dictionaries ssg-{profile}-cpe-dictionary.xml • CPE OVAL Content ssg-{profile}-cpe-oval.xml • OVAL Content ssg-{profile}-oval.xml • XCCDF Content ssg-{profile}-xccdf.xml • /usr/share/doc/scap-security-guide-/ HTML versions of SSG profles, easily consumable by humans. • /usr/share/doc/scap-security-guide-/table-{profile}-*.html HTML tables refecting which institutionalized policy a particular SSG rule conforms to. 3.3 OpenSCAP The SCAP protocol suite contains multiple complex data exchange formats that are used to transmit important vulnerability, confguration, and other security data. Historically, there have been few tools that provide a way to query this data in the needed format. This lack of Page 7 of 42
tooling makes the barrier to entry very high and discourages adoption of these protocols by the community. It’s the goal of the OpenSCAP project to create a framework of libraries and tools to improve the accessibility of SCAP and enhance the usability of the information it presents. SCAP is a protocol, akin to HTML, and consumers must use a protocol interpreter. OpenSCAP provides that functionality for the RHEL platform. The OpenSCAP homepage can be found at http://www.open-scap.org/page/Main_Page. 3.4 XCCDF As documented by NIST on their XCCDF specifcation page at http://scap.nist.gov/specifcations/xccdf/: XCCDF is a specification language for writing security checklists, benchmarks, and related kinds of documents. An XCCDF document represents a structured collection of security configuration rules for some set of target systems. The specification is designed to support information interchange, document generation, organizational and situational tailoring, automated compliance testing, and compliance scoring. The specification also defines a data model and format for storing results of benchmark compliance testing. The intent of XCCDF is to provide a uniform foundation for expression of security checklists, benchmarks, and other configuration guidance, and thereby foster more widespread application of good security practices. XCCDF documents are expressed in XML, and may be validated with an XML Schema-validating parser. Development of the XCCDF specification is being led by NSA, with contributions from other agencies and organizations. The current public draft of the specification document and related files can be downloaded below. A mailing list for XCCDF developers is available, please subscribe to participate in discussions. A publicly available archive of the XCCDF mailing list is also available. Within the project, XCCDF content is retained in /usr/share/xml/scap/ssg/content/. Page 8 of 42

3.4.1 Sample XCCDF Code To understand XCCDF, let’s review the disable_telnet_service rule within ssgrhel6-xccdf.xml. $ vim /usr/share/xml/scap/ssg/content/ssg-rhel6-xccdf.xml Once loaded, locate the disable_telnet_service rule: /<Rule id=”disable_telnet_service … <Rule id=”disable_telnet_service” selected=”false” severity=”high”> <title xmlns:xhtml=”http://www.w3.org/1999/xhtml” xml:lang=”en-US”> Disable telnet Service </title> <description xmlns:xhtml=”http://www.w3.org/1999/xhtml” xml:lang=”en-US”> The xhtml:codetelnet</xhtml:code> service can be disabled with the following command: xhtml:pre# chkconfig telnet off</xhtml:pre> </description> <reference href=”http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.80053r4.pdf”>AC-17(8)</reference> <reference href=”http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.80053r4.pdf”>CM-7</reference> <reference href=”http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.80053r4.pdf”>IA-5(1)(c)</reference> <reference href=”http://iase.disa.mil/cci/index.html”>68</reference> <reference href=”http://iase.disa.mil/cci/index.html”>1436</reference> <reference href=”http://iase.disa.mil/cci/index.html”>197</reference> <reference href=”http://iase.disa.mil/cci/index.html”>877</reference> <reference href=”http://iase.disa.mil/cci/index.html”>888</reference> <reference xmlns:dc=”http://purl.org/dc/elements/1.1/” href=”test_attestation”> dc:contributorDS</dc:contributor> dc:date20121026</dc:date> </reference> <rationale xmlns:xhtml=”http://www.w3.org/1999/xhtml” xml:lang=”en-US”> The telnet protocol uses unencrypted network communication, which means that data from the login session, including passwords and all other information transmitted during the session, can be stolen by eavesdroppers on the network. The telnet protocol is also subject to man-in-the-middle attacks. </rationale> <ident system=”http://cce.mitre.org”>CCE-26836-7</ident> <check system=”http://oval.mitre.org/XMLSchema/oval-definitions-5”> <check-content-ref name=”oval:ssg:def:335” href=”ssg-rhel6-oval.xml”/> </check> <check system=”ocil-transitional”> <check-export export-name=”the service is running” value-id=”conditional_clause”/> <check-content xmlns:xhtml=”http://www.w3.org/1999/xhtml”> To check that the xhtml:codetelnet</xhtml:code> service is disabled in system boot configuration, run the following command: xhtml:pre# chkconfig xhtml:codetelnet</xhtml:code> —list</xhtml:pre> Output should indicate the xhtml:codetelnet</xhtml:code> service has either not been installed, or has been disabled, as shown in the example below: xhtml:pre# chkconfig xhtml:codetelnet</xhtml:code> —list xhtml:codetelnet</xhtml:code> off</xhtml:pre> </check-content> </check> </Rule> … The code can be broken into the following parts: Page 9 of 42
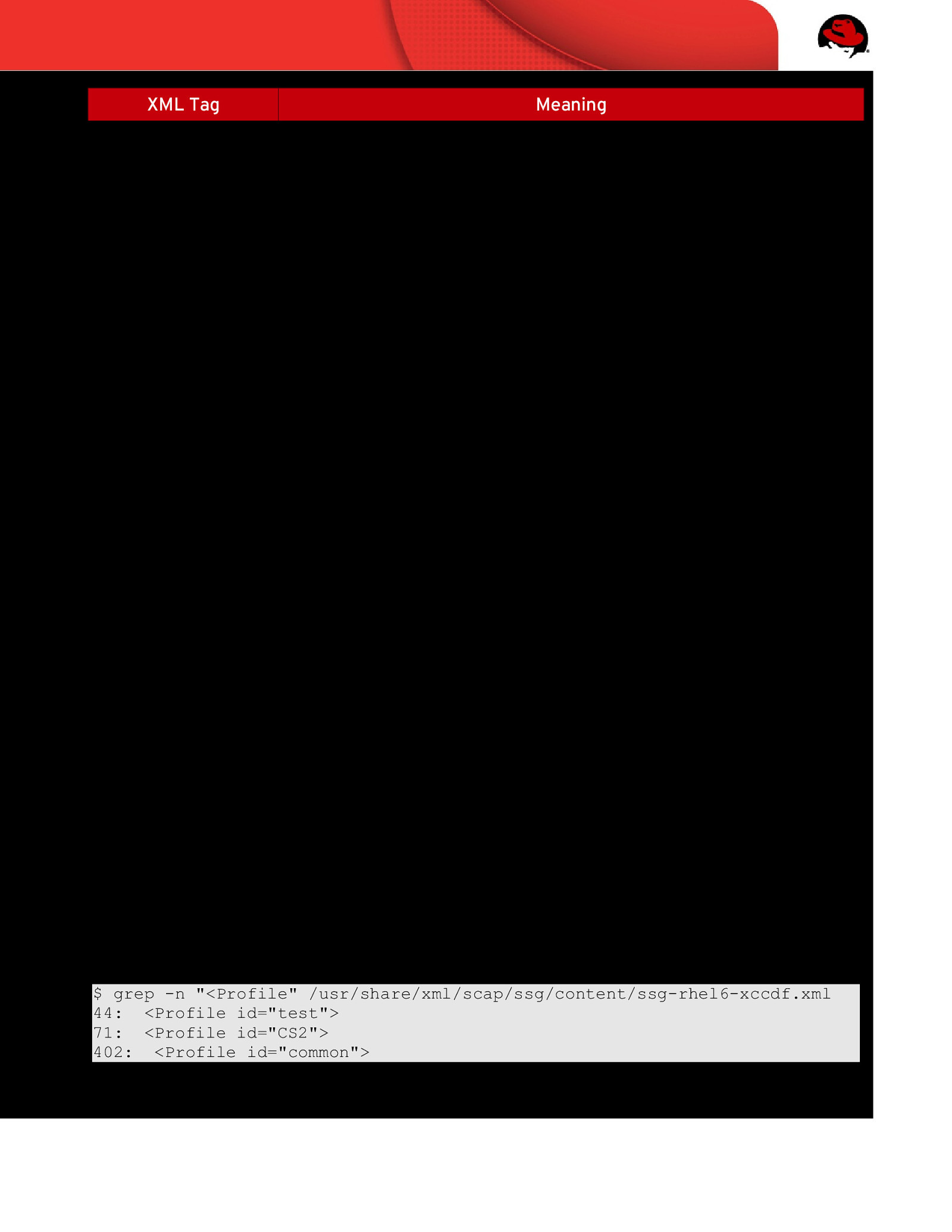
XML Tag <Rule> Meaning Indicates: • Rule Name … id=”disable_telnet_service” …. • Severity … severity=”high” … • If the rule is enforced / selected …. selected=”true” …
<title> The XCCDF Rule title <description> Largely free form, contains implementation instructions and any policy references <rationale> Identifes the logic behind applying this <rule> to the system. Answers “why is this important?” <ident system…> Identifes CCE mapping <check system…> Identifes which version of OVAL the check was written for <check-contentref…> There are two elements for this tag: • href=….. Path to associated OVAL fle • name=….. Identifes the corresponding OVAL rule name, such as oval:ssg:def:281. If one were to search for this rule within the href= identifed fle, they would be brought to the corresponding OVAL code. Table 1: XCCDF Rule Elements 3.4.2 Profiles XCCDF rules are logically organized into profles. To query which profles are contained within the SCAP Security Guide project, run the following command: $ grep -n “<Profile” /usr/share/xml/scap/ssg/content/ssg-rhel6-xccdf.xml 44: <Profile id=”test”> 71: <Profile id=”CS2”> 402: <Profile id=”common”> Page 10 of 42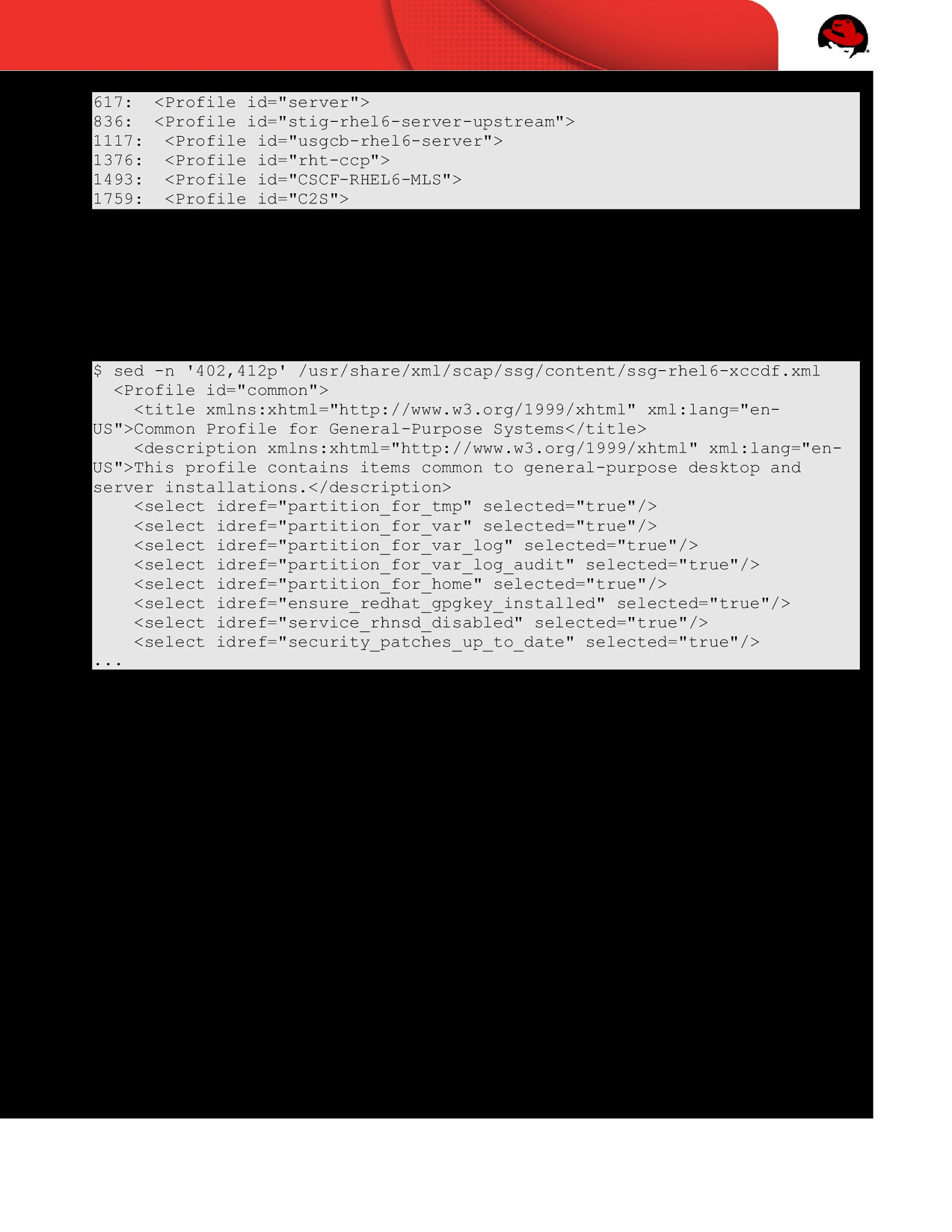
617: <Profile id=”server”> 836: <Profile id=”stig-rhel6-server-upstream”> 1117: <Profile id=”usgcb-rhel6-server”> 1376: <Profile id=”rht-ccp”> 1493: <Profile id=”CSCF-RHEL6-MLS”> 1759: <Profile id=”C2S”> If you were to view line 402 and those proceeding, you will see a sampling of which rules make up the common profle: $ sed -n ‘402,412p’ /usr/share/xml/scap/ssg/content/ssg-rhel6-xccdf.xml <Profile id=”common”> <title xmlns:xhtml=”http://www.w3.org/1999/xhtml” xml:lang=”enUS”>Common Profile for General-Purpose Systems</title> <description xmlns:xhtml=”http://www.w3.org/1999/xhtml” xml:lang=”enUS”>This profile contains items common to general-purpose desktop and server installations.</description> <select idref=”partition_for_tmp” selected=”true”/> <select idref=”partition_for_var” selected=”true”/> <select idref=”partition_for_var_log” selected=”true”/> <select idref=”partition_for_var_log_audit” selected=”true”/> <select idref=”partition_for_home” selected=”true”/> <select idref=”ensure_redhat_gpgkey_installed” selected=”true”/> <select idref=”service_rhnsd_disabled” selected=”true”/> <select idref=”security_patches_up_to_date” selected=”true”/> … Page 11 of 42
3.5 OVAL OVAL is an information security community effort to standardize how to assess and report upon the machine state of computer systems. OVAL includes a language to encode system details, and an assortment of content repositories held throughout the community. The OVAL component of SCAP can be a bit obtuse, and is arguably the most complex specifcation of the SCAP family. Instead of fully detailing here, we’ll acknowledge it’s existence, and return to the topic when we begin authoring custom content. The OVAL homepage is http://oval.mitre.org/ Page 12 of 42
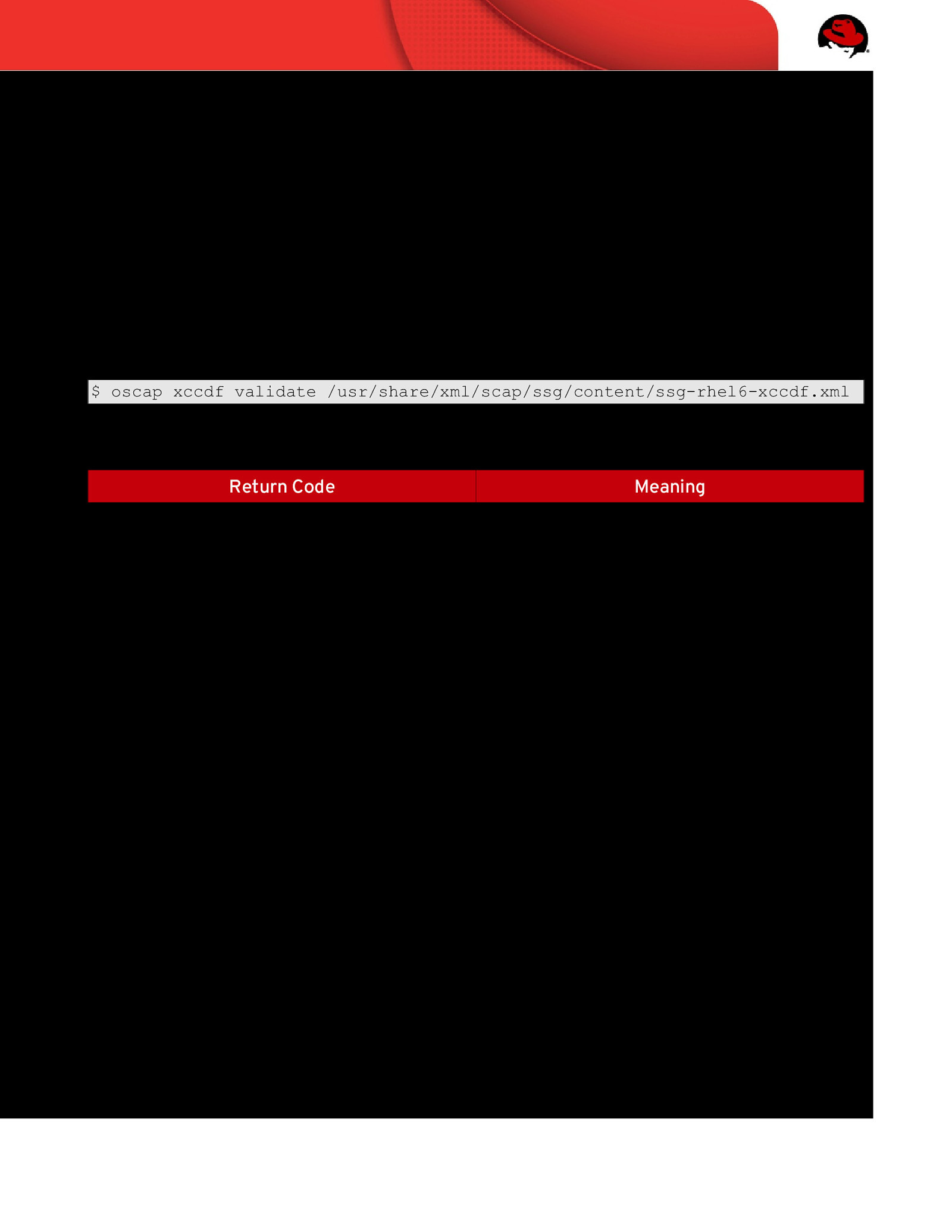
4 OPERATION 4.1 XCCDF Validation Similar to validating HTML content through W3C, it’s always a good idea to validate your XCCDF content before utilizing it to perform a scan on your system. Theoretically, by the time XCCDF content makes its way to end-users, this has already been done…. however, why not make sure? OpenSCAP contains the ability to validate a given XCCDF fle for valid XML schema. Every found error is printed to the standard error. To quickly validate the XCCDF content, run the following command: $ oscap xccdf validate /usr/share/xml/scap/ssg/content/ssg-rhel6-xccdf.xml The output will show a return code, the reference table for which is: Return Code Meaning 0 Validation Successful 1 Validation Not Performed Due to Error 2 XCCDF Document is Invalid Page 13 of 42
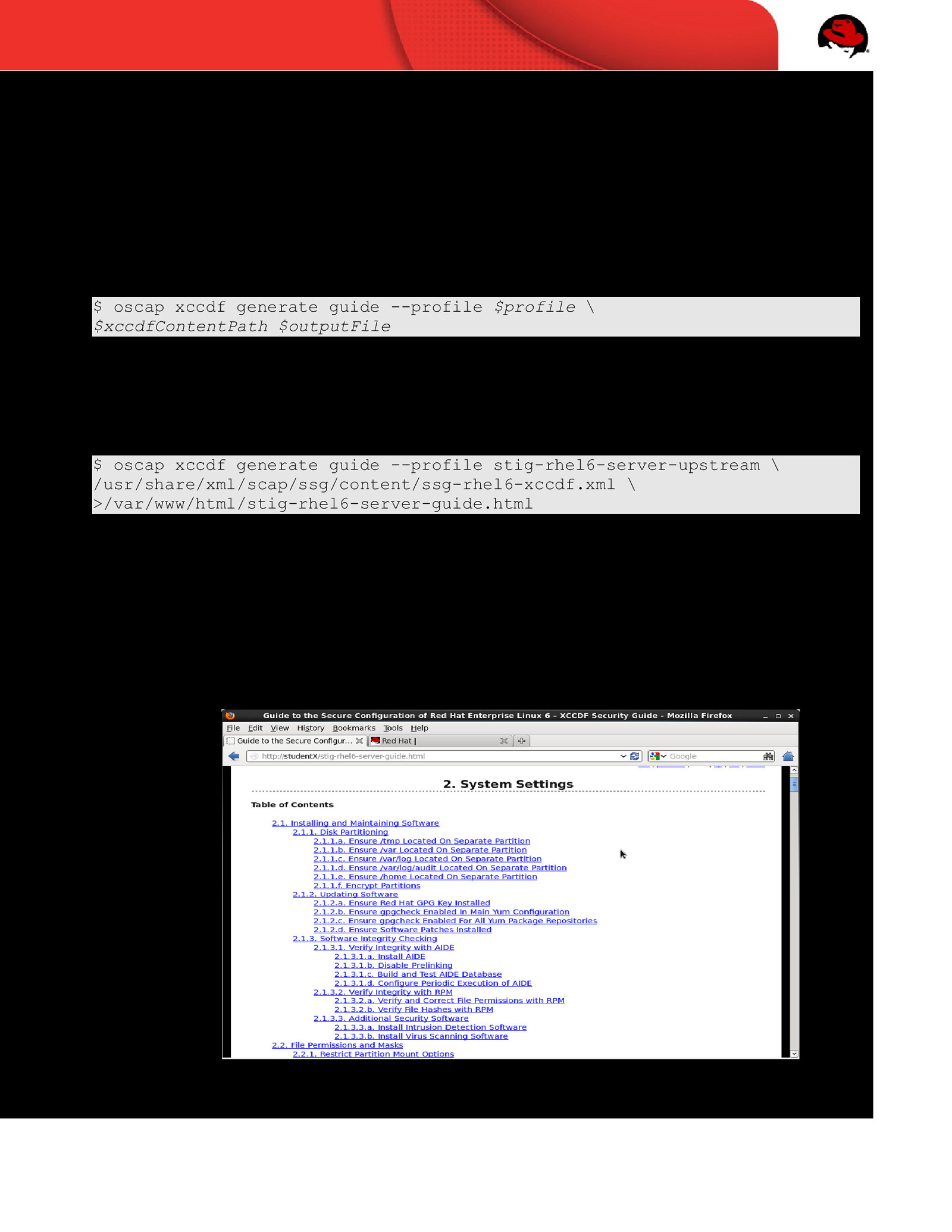
4.2 Generate HTML Guide In Chapter 3, you learned about logical groupings of individual XCCDF rules known as an XCCDF Profle. While users certainly can make their way through the XML fles, an arguably more effcient way to review XCCDF content is to generate an HTML checklist. The OpenSCAP utility can transform your XCCDF into an HTML checklist through the “generate guide” option: $ oscap xccdf generate guide —profile $profile \ $xccdfContentPath $outputFile For this workshop, generate an XCCDF Checklist for the stig-rhel6-server-upstream profle, placing the output in Apache’s HTML directory: $ oscap xccdf generate guide —profile stig-rhel6-server-upstream \ /usr/share/xml/scap/ssg/content/ssg-rhel6-xccdf.xml \ >/var/www/html/stig-rhel6-server-guide.html Point your web browser to http://studentX.lab.ssgproject.org/stig-rhel6-serverguide.html In the Table of Contents, click the “Rule Selection” link. The resulting HTML page will list all rules, indicating if they are “selected” or “not selected” for the stig-rhel6-serverupstream profle. Clicking on a rule title will expose full information on the rule. Page 14 of 42

4.3 Performing a Scan At this point you have a validated XCCDF fle, and through the previous section, an understanding of which rules our system will be scanned against. Using the OpenSCAP utility provided through the operating system, our next step is to run a scan. There are several available options within the OpenSCAP utility. Sources of relevant documentation the following man pages: •
man oscap
•
man scap-security-guide
Both documents detail sample commands, while the OpenSCAP manpage outlines all available arguments. For this workshop, we will use: •
—profile
•
—results
•
—report
•
—cpe
Mandatory; identifes which profle to scan against
Optional; indicates location to place XML formatted results
Optional, indicates location to place HTML formatted results
Mandatory, identifes location of CPE dictionary
Putting everything together, our command looks like this: $ sudo oscap xccdf eval —profile stig-rhel6-server-upstream \ —results /var/www/html/hostname-results.xml \ —report /var/www/html/hostname-report.html \ —cpe /usr/share/xml/scap/ssg/content/ssg-rhel6-cpe-dictionary.xml \ /usr/share/xml/scap/ssg/content/ssg-rhel6-xccdf.xml
Page 15 of 42
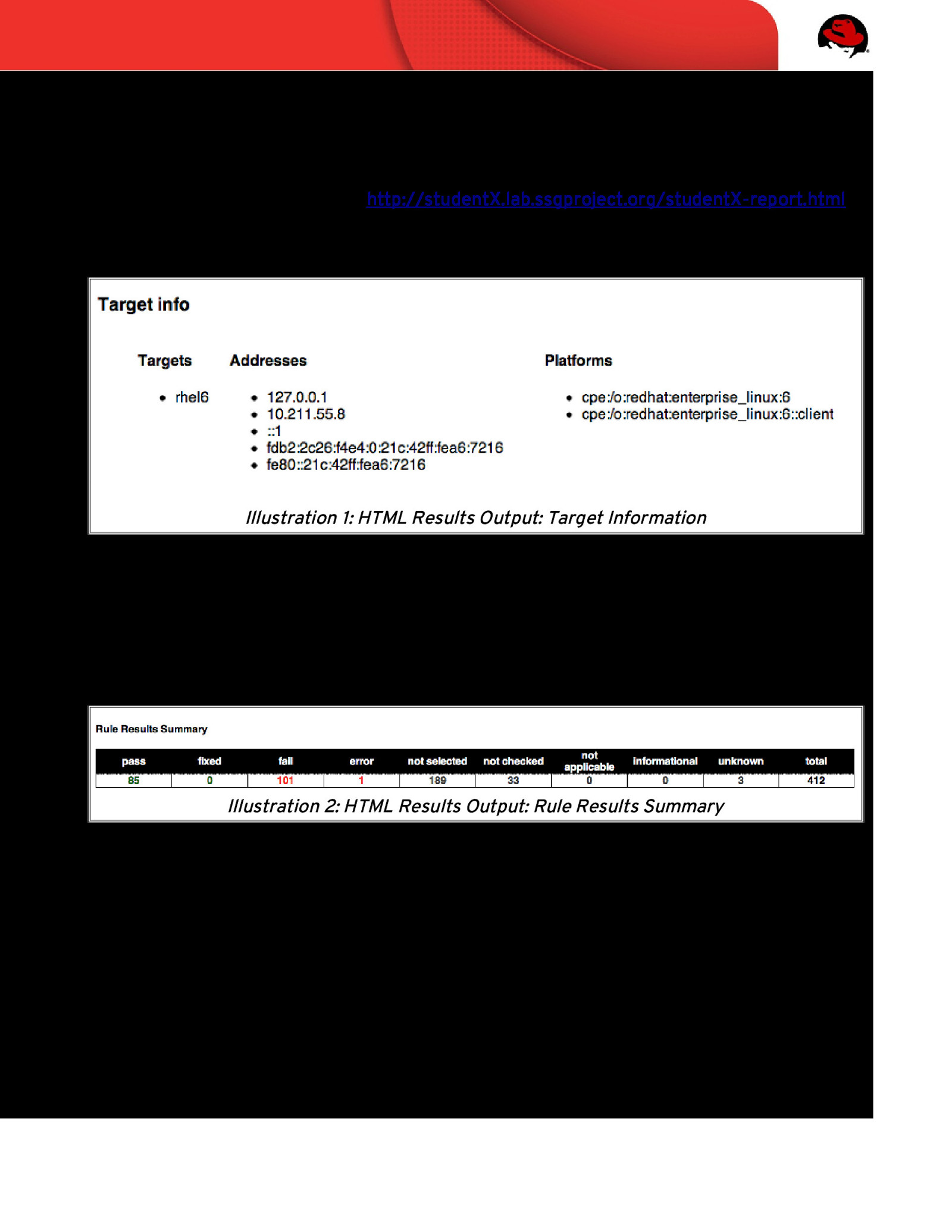
4.4 Interpreting Results 4.4.1 HTML 1. Using a web browser, load http://studentX.lab.ssgproject.org/studentX-report.html • Target Information Illustration 1: HTML Results Output: Target Information This information will include hostname, network information, and relevant platform data. The CPE is of particular importance, as it calls out the host platform (RHEL, Fedora, etc). • Rule Results Summary Illustration 2: HTML Results Output: Rule Results Summary This section provides an overview of scanning results. Page 16 of 42
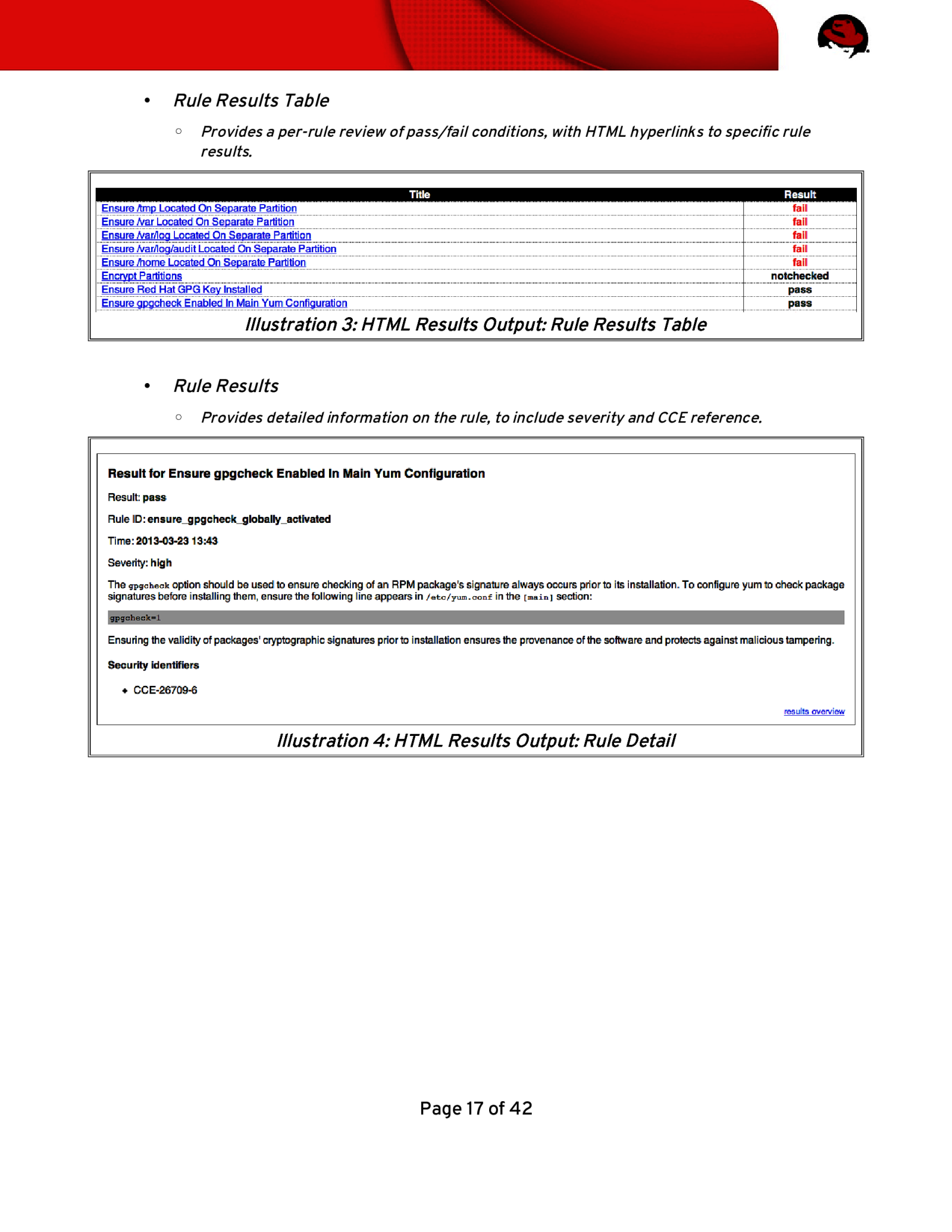
• Rule Results Table ◦ Provides a per-rule review of pass/fail conditions, with HTML hyperlinks to specifc rule results. Illustration 3: HTML Results Output: Rule Results Table • Rule Results ◦ Provides detailed information on the rule, to include severity and CCE reference. Illustration 4: HTML Results Output: Rule Detail Page 17 of 42

4.4.2 XML The OpenSCAP utility can output results in XML. Load studentX-results.xml: $ vim /var/www/html/studentX-results.xml The results are contained within <rule-result> tags. Issue a search query in vi: /<rule-result You will be brought to XML stanzas similar to: <rule-result idref=”package_aide_installed” time=”2014-07-28T17:04:53” severity=”medium” weight=”1.000000”> <result>pass</result> <ident system=”http://cce.mitre.org”>CCE-27024-9</ident> <fix xmlns:xhtml=”http://www.w3.org/1999/xhtml” system=”urn:xccdf:fix:script:sh”> if ! rpm -qa | grep -q aide; then yum -y install aide fi </fix> <check system=”http://oval.mitre.org/XMLSchema/oval-definitions-5”> <check-content-ref name=”oval:ssg:def:1331” href=”ssg-rhel6oval.xml”/> </check> </rule-result> Page 18 of 42

The XML above can be parsed as follows: XML Tag Meaning <rule-result idref….> Identifes which XCCDF rule the results refect <result> Pass/Fail/NotApplicable <ident system….> Identifes corresponding CCE <fix> Identifes remediation actions, in bash, to perform <check system….> Identifes which version of OVAL the check content was written against <check-content-ref Corresponding OVAL check name (name=….) and source OVAL …..> fle (href=….) Table 2: Scan Results XML Output Page 19 of 42
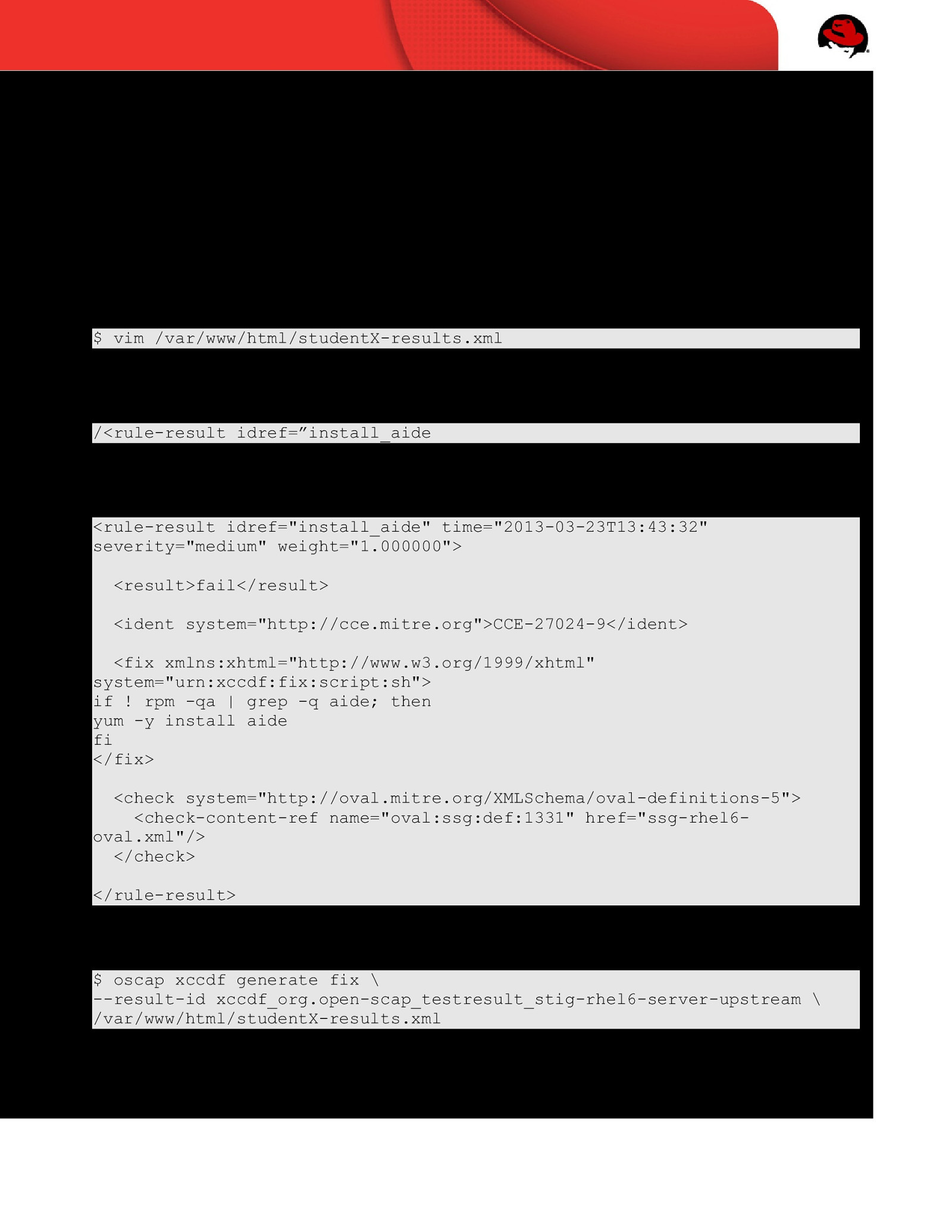
4.5 Remediation SCAP Security Guide contains robust remediation capabilities for RHEL 6. These exist in the form of bash scripts. In this section, we will explore the SSG’s remediation scripts and how they are applied to aide in system hardening. 4.5.1 Remediation? How Do? Earlier in this workshop we ran a scan, and created an XML output fle at /var/www/html/studentX-results.xml. Let’s quickly review that fle again: $ vim /var/www/html/studentX-results.xml Once loaded, search for the install_aide result: /<rule-result idref=”install_aide You will be brought to XML stanzas similar to: <rule-result idref=”install_aide” time=”2013-03-23T13:43:32” severity=”medium” weight=”1.000000”> <result>fail</result> <ident system=”http://cce.mitre.org”>CCE-27024-9</ident> <fix xmlns:xhtml=”http://www.w3.org/1999/xhtml” system=”urn:xccdf:fix:script:sh”> if ! rpm -qa | grep -q aide; then yum -y install aide fi </fix> <check system=”http://oval.mitre.org/XMLSchema/oval-definitions-5”> <check-content-ref name=”oval:ssg:def:1331” href=”ssg-rhel6oval.xml”/> </check> </rule-result> OpenSCAP has the ability to transform the <fix> section into an executable script for any rules which failed. To generate this fx script, run the following from the command-line: $ oscap xccdf generate fix \ —result-id xccdf_org.open-scap_testresult_stig-rhel6-server-upstream \ /var/www/html/studentX-results.xml Page 20 of 42
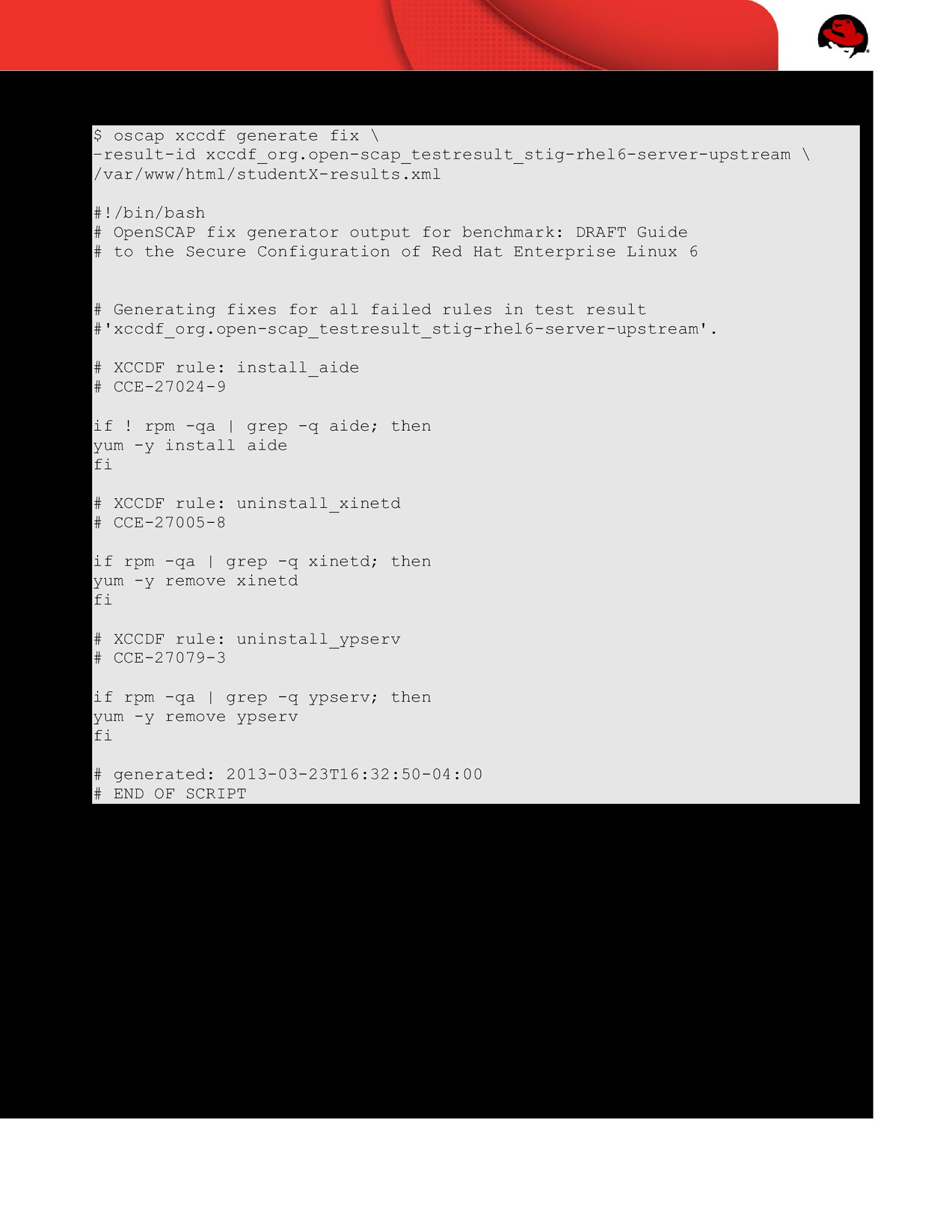
You will receive output similar to the following: $ oscap xccdf generate fix \ –result-id xccdf_org.open-scap_testresult_stig-rhel6-server-upstream \ /var/www/html/studentX-results.xml #!/bin/bash # OpenSCAP fix generator output for benchmark: DRAFT Guide # to the Secure Configuration of Red Hat Enterprise Linux 6 # Generating fixes for all failed rules in test result #’xccdf_org.open-scap_testresult_stig-rhel6-server-upstream’. # XCCDF rule: install_aide # CCE-27024-9 if ! rpm -qa | grep -q aide; then yum -y install aide fi # XCCDF rule: uninstall_xinetd # CCE-27005-8 if rpm -qa | grep -q xinetd; then yum -y remove xinetd fi # XCCDF rule: uninstall_ypserv # CCE-27079-3 if rpm -qa | grep -q ypserv; then yum -y remove ypserv fi # generated: 2013-03-23T16:32:50-04:00 # END OF SCRIPT This output could be redirected to a bash script, or build into your RHEL6 provisioning process (e.g. the %post section of a kickstart). Page 21 of 42

4.6 Scanning Automation Scanning can be automated/scheduled via cron. To schedule a daily scan of your system, place the following script into /etc/cron.daily/ssg-scan
oscap xccdf eval —profile stig-rhel6-server-upstream \ —results /var/www/html/date +%F-%R-hostname-results.xml \ —report /var/www/html/date +%F-%R-hostname-report.xml \ —cpe /usr/share/xml/scap/ssg/content/ssg-rhel6-cpe-dictionary.xml \ /usr/share/xml/scap/ssg/content/ssg-rhel6-xccdf.xml
Note: The XML results and HTML reports contain security information of your system. When creating reports on a production system, particularly those within the DoD and Intelligence Community, ensure your output is placed into a restricted location on the system. The /root directory is often ideal.
Page 22 of 42
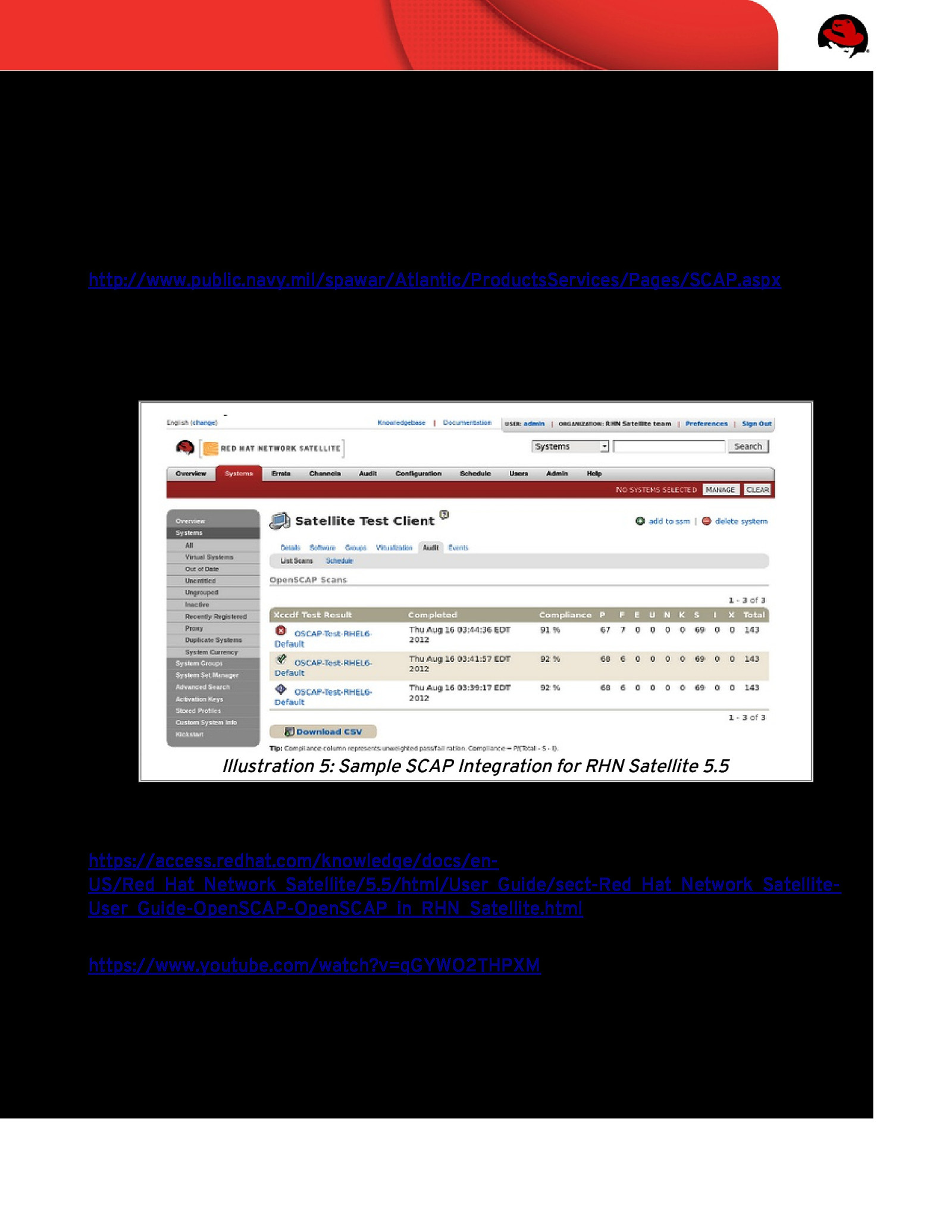
4.7 Alternative Tools 4.7.1 SPAWAR SCAP Compliance Checker (SPAWAR SCC) The SCAP Compliance Checker (SCC) is a Security Content Automation Protocol (SCAP) scanner developed by Space and Naval Warfare (SPAWAR) Systems Center Atlantic. The SCC homepage is located at: http://www.public.navy.mil/spawar/Atlantic/ProductsServices/Pages/SCAP.aspx 4.7.2 Red Hat Network Satellite Starting with RHN Satellite >= 5.5, users can now centralize their SCAP scanning through their Satellite administrative console (GUI) or via the Satellite API. Illustration 5: Sample SCAP Integration for RHN Satellite 5.5 This capability is documented at: https://access.redhat.com/knowledge/docs/enUS/Red_Hat_Network_Satellite/5.5/html/User_Guide/sect-Red_Hat_Network_SatelliteUser_Guide-OpenSCAP-OpenSCAP_in_RHN_Satellite.html A video presentation of this integration is available on YouTube: https://www.youtube.com/watch?v=qGYWO2THPXM – Security Compliance by OpenSCAP – Integration with Satellite Page 23 of 42
5 CONTENT CUSTOMIZATION 5.1 So, You Wanna Be a Developer? Welcome! Making changes to the project requires posting a patch to the mailing list so that it can be vetted. Once there, another commit-level project member must issue acknowledgement (“ACK”) to accept it, and then it can be pushed. Assuming another project member has not issued a NACK in protest frst, that is! The following instructions assume familiarity with git and git-send-email, but project members are happy to provide tips if you encounter any roadblocks. To properly join the project, you must frst establish a few required accounts: 1. Join the mailing list, it’s how developers and users communicate: https://fedorahosted.org/mailman/listinfo/scap-security-guide 2. Create your FedoraHosted account. It formally registers you as a developer, and allows you to upload your public SSH key (required for commits): https://admin.fedoraproject.org/accounts/ 3. Once your FedoraHosted account is created, request membership to the SCAP Security Guide project: https://admin.fedoraproject.org/accounts/group/view/gitscap-security-guide 4. Lastly, review a few coding standards: ◦ How to Create a New Guidance Item in XCCDF ◦ How to Create a New Compliance Check in OVAL Page 24 of 42
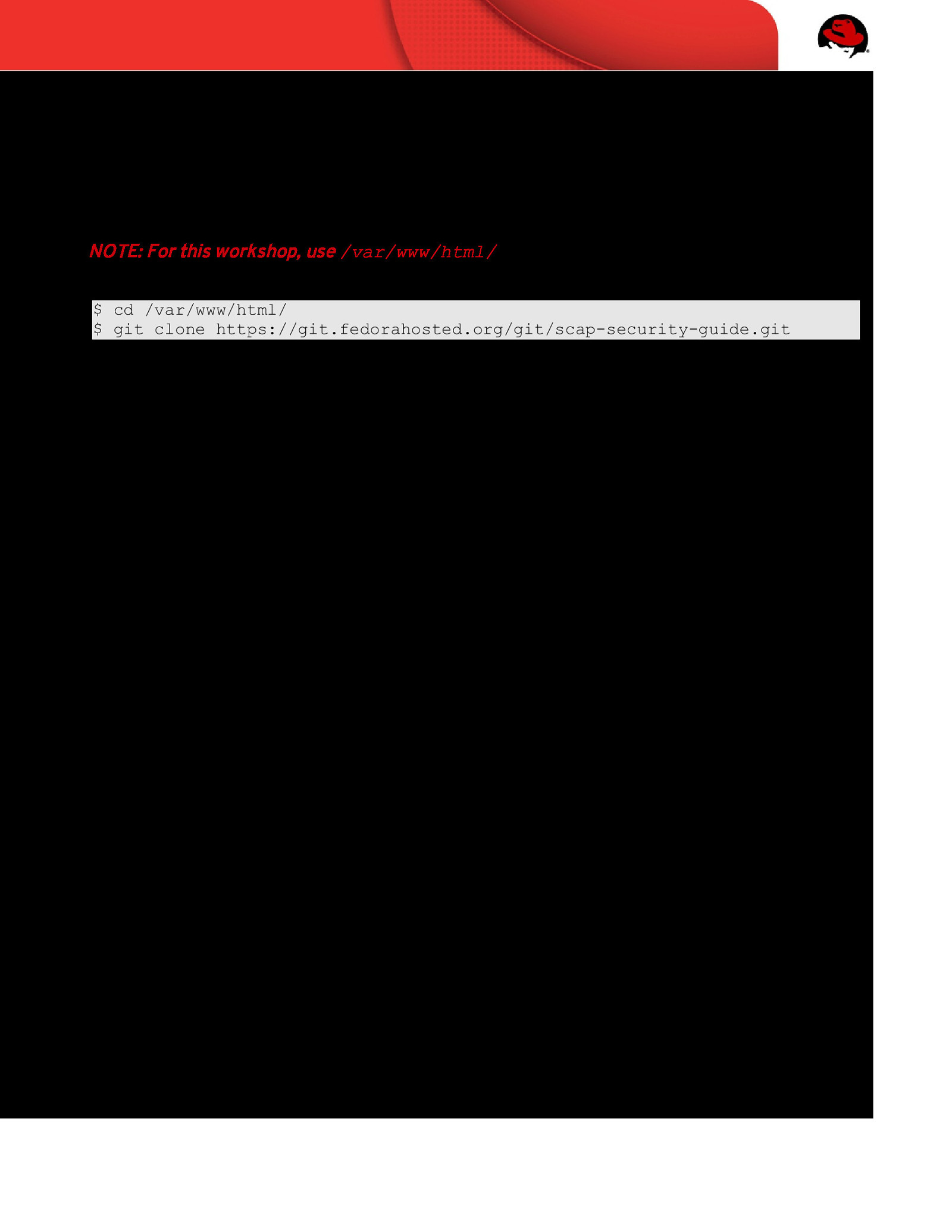
5.2 Cloning the Source If you’ve been given commit-level access, you will interface with the git repository over SSH. Change directory to where you’d like the source code to be placed (e.g. cd ~/MyProjects/) and run the following command: NOTE: For this workshop, use /var/www/html/ $ cd /var/www/html/ $ git clone https://git.fedorahosted.org/git/scap-security-guide.git Page 25 of 42
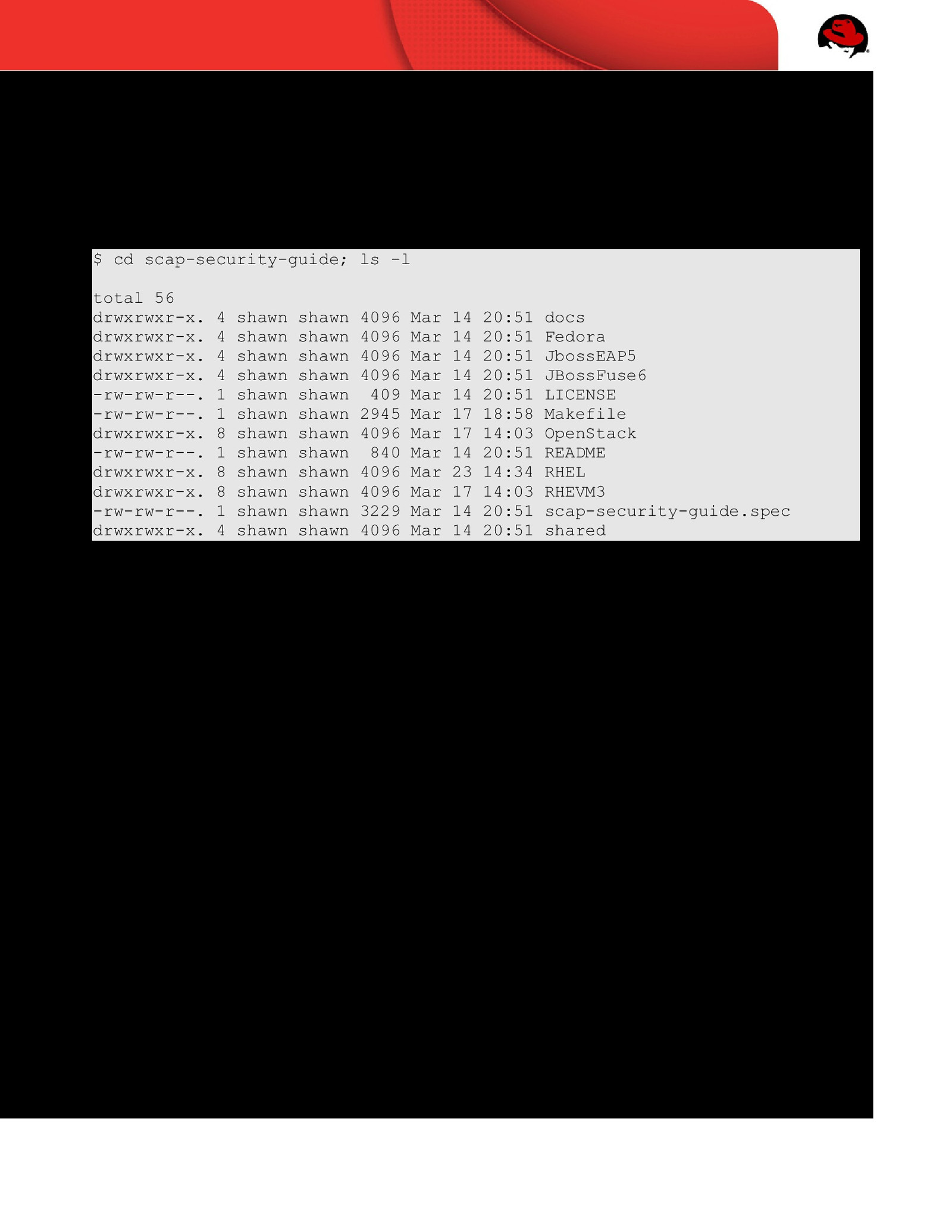
5.3 Understanding the Code Tree You’ve now cloned the projects source code. A new directory, scap-security-guide, was created where you ran the clone command. Change directory into it and perform a directory listing: $ cd scap-security-guide; ls -l total 56 drwxrwxr-x. drwxrwxr-x. drwxrwxr-x. drwxrwxr-x. -rw-rw-r—. -rw-rw-r—. drwxrwxr-x. -rw-rw-r—. drwxrwxr-x. drwxrwxr-x. -rw-rw-r—. drwxrwxr-x. 4 4 4 4 1 1 8 1 8 8 1 4 shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn shawn 4096 4096 4096 4096 409 2945 4096 840 4096 4096 3229 4096 Mar Mar Mar Mar Mar Mar Mar Mar Mar Mar Mar Mar 14 14 14 14 14 17 17 14 23 17 14 14 20:51 20:51 20:51 20:51 20:51 18:58 14:03 20:51 14:34 14:03 20:51 20:51 Page 26 of 42 docs Fedora JbossEAP5 JBossFuse6 LICENSE Makefile OpenStack README RHEL RHEVM3 scap-security-guide.spec shared

Top level directories have been created to contain the per-technology SCAP content. Change directory into RHEL/6/ and perform a directory listing: $ cd RHEL/6; ls -l total 40 drwxrwxr-x. 2 shawn drwxrwxr-x. 9 shawn -rw-rw-r—. 1 shawn drwxrwxr-x. 2 shawn -rw-rw-r—. 1 shawn drwxrwxr-x. 2 shawn drwxrwxr-x. 2 shawn drwxrwxr-x. 2 shawn shawn 4096 Mar 23 17:35 dist shawn 4096 Mar 21 18:57 input shawn 10277 Mar 14 20:51 Makefile shawn 4096 Mar 23 17:35 output shawn 1616 Mar 14 20:51 README shawn 4096 Mar 17 18:57 references shawn 4096 Mar 17 14:03 transforms shawn 4096 Mar 14 20:51 utils The directory usages are: Directory Usage dist/ The build process generates fnalized content here, which then are included into SSG RPMs. input/ Source fles that generate SCAP content, such as XCCDF and OVAL. Since a single large XML fle is an impractical format for multiple authors to collaborate on editing SCAP content, efforts are made to keep logically related guidance and checking content in individual fles. output/ Used as a storage area for items generated by the fles in the inputs directory. It should be empty in the repository, and built on users’ individual systems (and rely on its .gitignore fle to keep such fles out). The output directory contains transitional output (which may only exist in order to be further transformed) as well as fnal output. references/ Contain documents which are specifed as references from within the SCAP content, or documents that are “seeds,” viz. documents whose prose will be translated into SCAP formats, as well as other examples of SCAP content. transforms/ Resources that enable the fles inside the input directory (or output directory) to be combined and reformatted into valid SCAP formats or human-readable formats. Table 3: SSG Code Tree: RHEL6/ Page 27 of 42
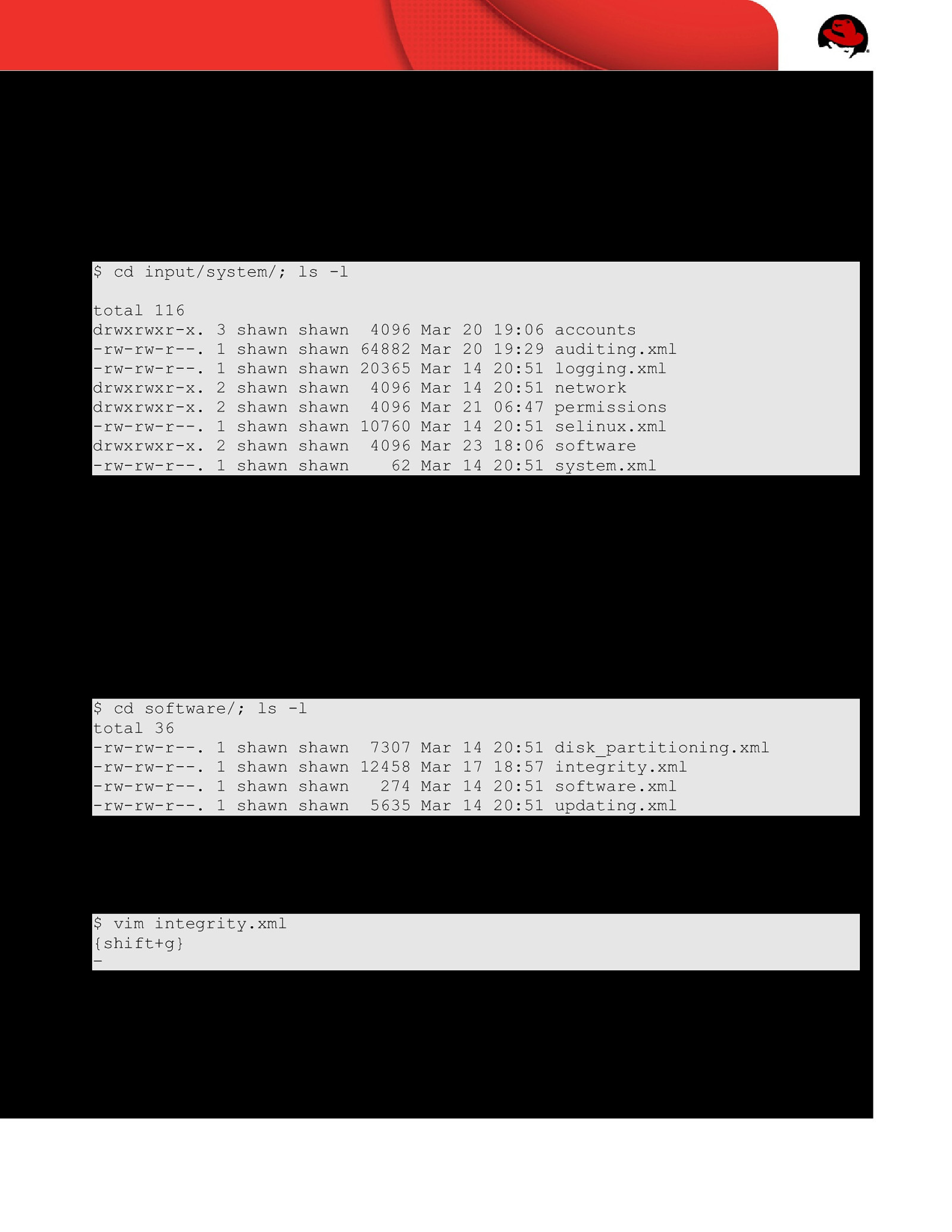
5.4 Creating your frst XCCDF rule For this workshop we will create a rule which mandates installation of the SCAP Security Guide RPM, and we’ll identify failure (the lack of installation) as a CAT I / SEV 1 fnding. The directory structure, and multiple XML fles, can be a bit overwhelming at frst. Change directory to input/system/ and perform a directory listing: $ cd input/system/; ls -l total 116 drwxrwxr-x. -rw-rw-r—. -rw-rw-r—. drwxrwxr-x. drwxrwxr-x. -rw-rw-r—. drwxrwxr-x. -rw-rw-r—. 3 1 1 2 2 1 2 1 shawn shawn shawn shawn shawn shawn shawn shawn shawn 4096 Mar 20 19:06 accounts shawn 64882 Mar 20 19:29 auditing.xml shawn 20365 Mar 14 20:51 logging.xml shawn 4096 Mar 14 20:51 network shawn 4096 Mar 21 06:47 permissions shawn 10760 Mar 14 20:51 selinux.xml shawn 4096 Mar 23 18:06 software shawn 62 Mar 14 20:51 system.xml To aid with multi-author content creation, the SSG project creates compartmented XCCDF fles. These individual fles are merged together during our Make/compilation process (more on that later!). In the directory listing above you’ll notice auditing.xml, logging.xml, and a few directories. Since we’re creating a rule that deals with software, change directory into software/ and perform a directory listing: $ cd software/; ls -l total 36 -rw-rw-r—. 1 shawn shawn 7307 Mar 14 -rw-rw-r—. 1 shawn shawn 12458 Mar 17 -rw-rw-r—. 1 shawn shawn 274 Mar 14 -rw-rw-r—. 1 shawn shawn 5635 Mar 14 20:51 18:57 20:51 20:51 disk_partitioning.xml integrity.xml software.xml updating.xml As the SSG project relates to security, lets create the new rule within the integrity.xml section. Load that fle in your favorite text editor, then place yourself one line above EOF: $ vim integrity.xml {shift+g} - Page 28 of 42
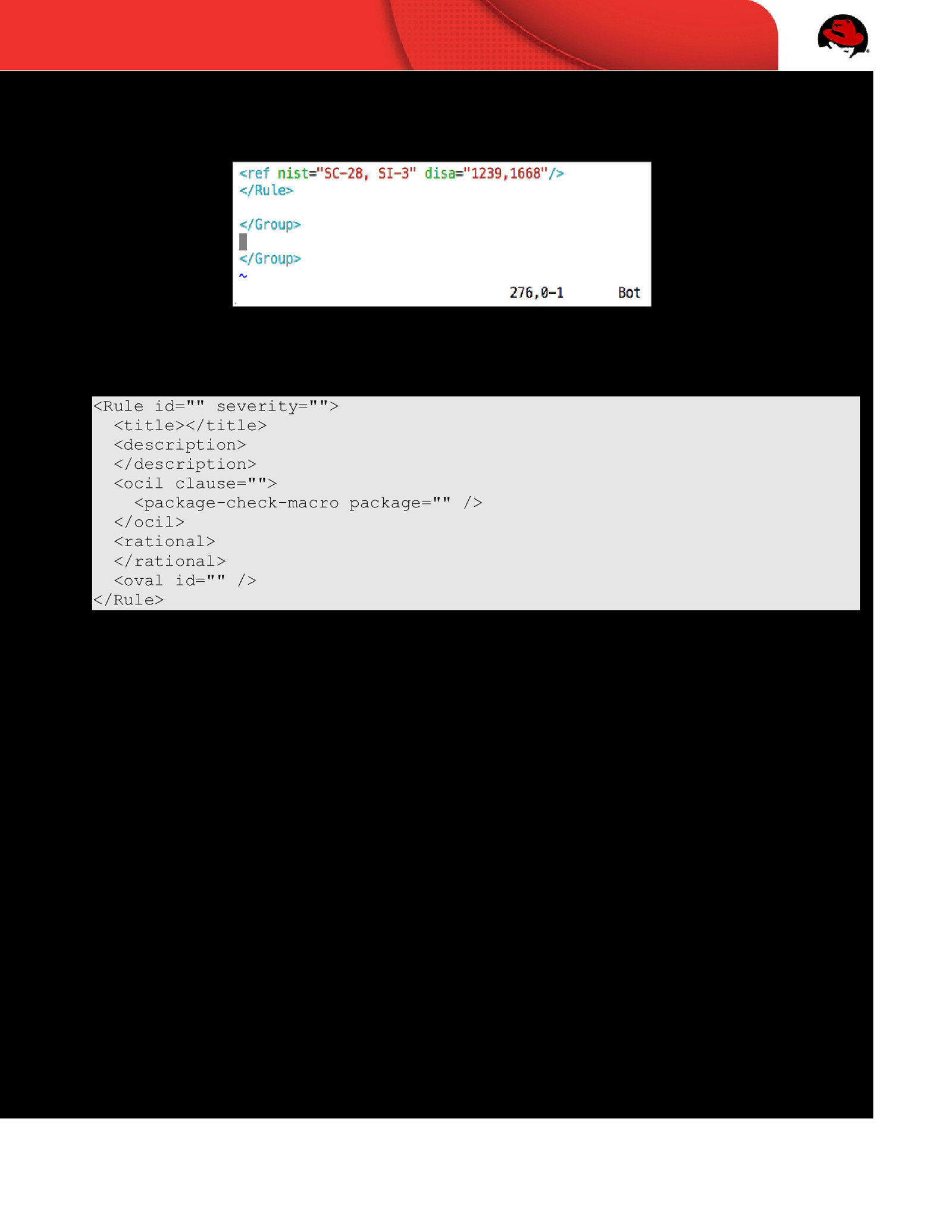
Your screen should be similar to the following: The template for SSG XCCDF rules is below. Insert the following template into integrity.xml: <Rule id=”” severity=”“> <title></title> <description> </description> <ocil clause=”“> <package-check-macro package=”” /> </ocil> <rational> </rational> <oval id=”” /> </Rule> Using the template above, create a rule which: 1. Has an XCCDF rule_id of “package_scap-security-guide_installed” with a severity of “high” 2. Has a human readable title of ‘Install SCAP Security Guide” 3. Outlines a method to install SSG. For example, “yum install scap-securityguide” 4. States that “if SCAP Security Guide is not installed, this is a fnding” 5. Includes the proper package name, scap-security-guide, in the package check macro 6. Includes rationale on why the SSG project is awesome, and should be installed 7. Corresponds to a (currently non-existent) OVAL rule named “package_scap-security-guide_installed” Page 29 of 42
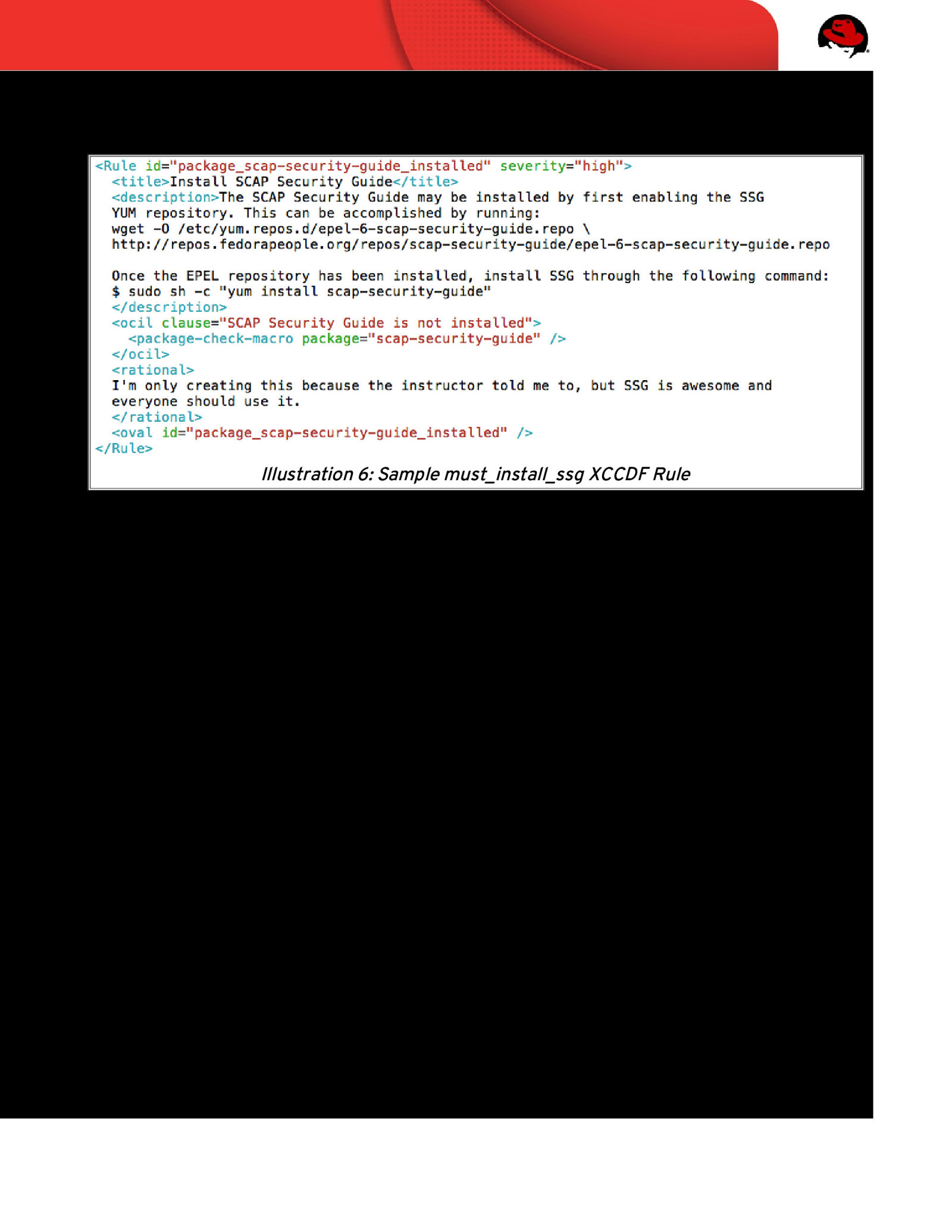
Your completed template will look similar to: Illustration 6: Sample must_install_ssg XCCDF Rule Done! Hopefully that wasn’t too painful. If you’re curious on where the “package-checkmacro” comes from, check out RHEL/6/transforms/shorthand2xccdf.xslt and search for lines that begin with “<xsl:template match=”” The shorthand2xccdf.xslt fle contains many short-hand macros that are available these insert template text into fnal XCCDF output. Unfortunately, in a two hour workshop, we don’t have enough time to properly cover all embedded XSLT transformations within the SSG. Feel free to direct questions to the public mailing list! Page 30 of 42
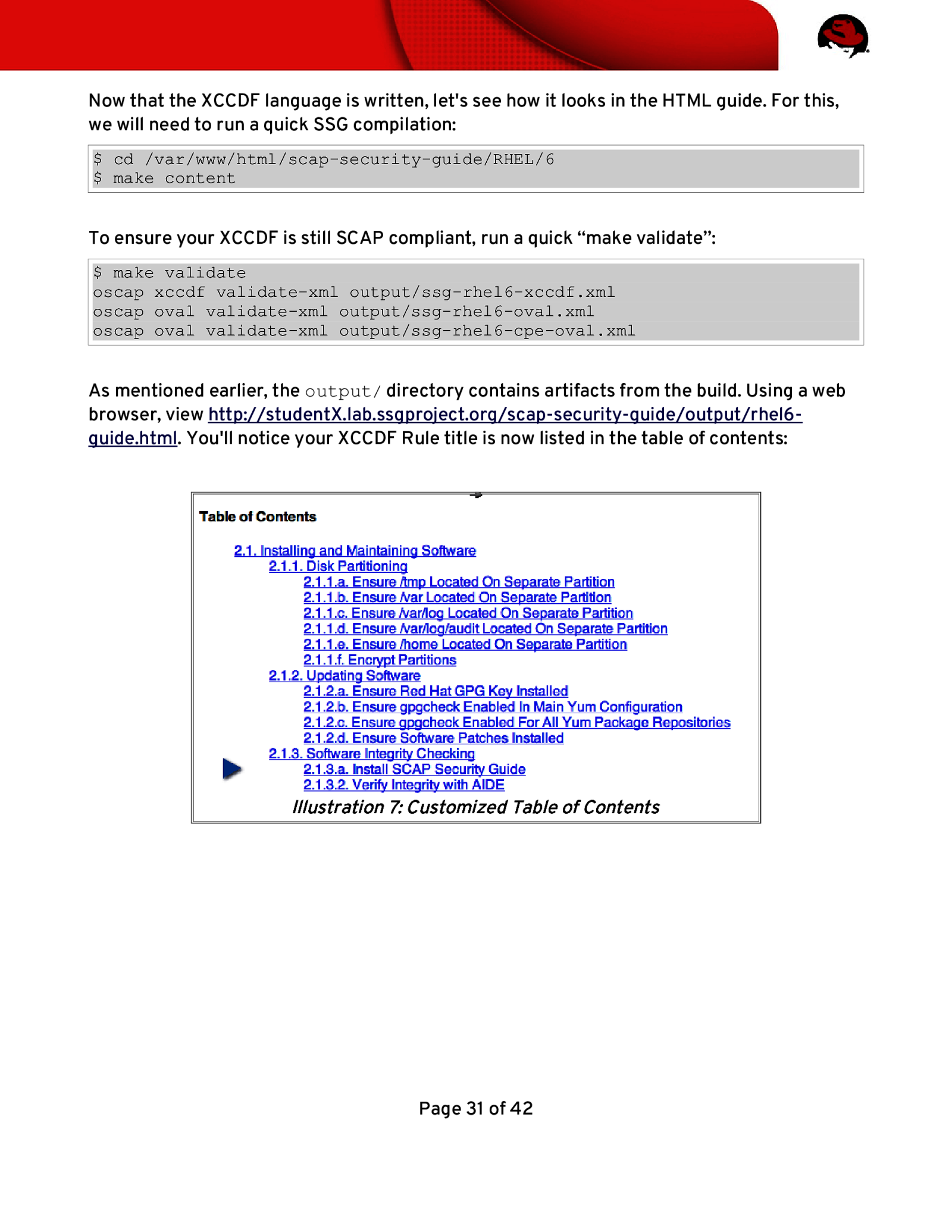
Now that the XCCDF language is written, let’s see how it looks in the HTML guide. For this, we will need to run a quick SSG compilation: $ cd /var/www/html/scap-security-guide/RHEL/6 $ make content To ensure your XCCDF is still SCAP compliant, run a quick “make validate”: $ make validate oscap xccdf validate-xml output/ssg-rhel6-xccdf.xml oscap oval validate-xml output/ssg-rhel6-oval.xml oscap oval validate-xml output/ssg-rhel6-cpe-oval.xml As mentioned earlier, the output/ directory contains artifacts from the build. Using a web browser, view http://studentX.lab.ssgproject.org/scap-security-guide/output/rhel6guide.html. You’ll notice your XCCDF Rule title is now listed in the table of contents: Illustration 7: Customized Table of Contents Page 31 of 42
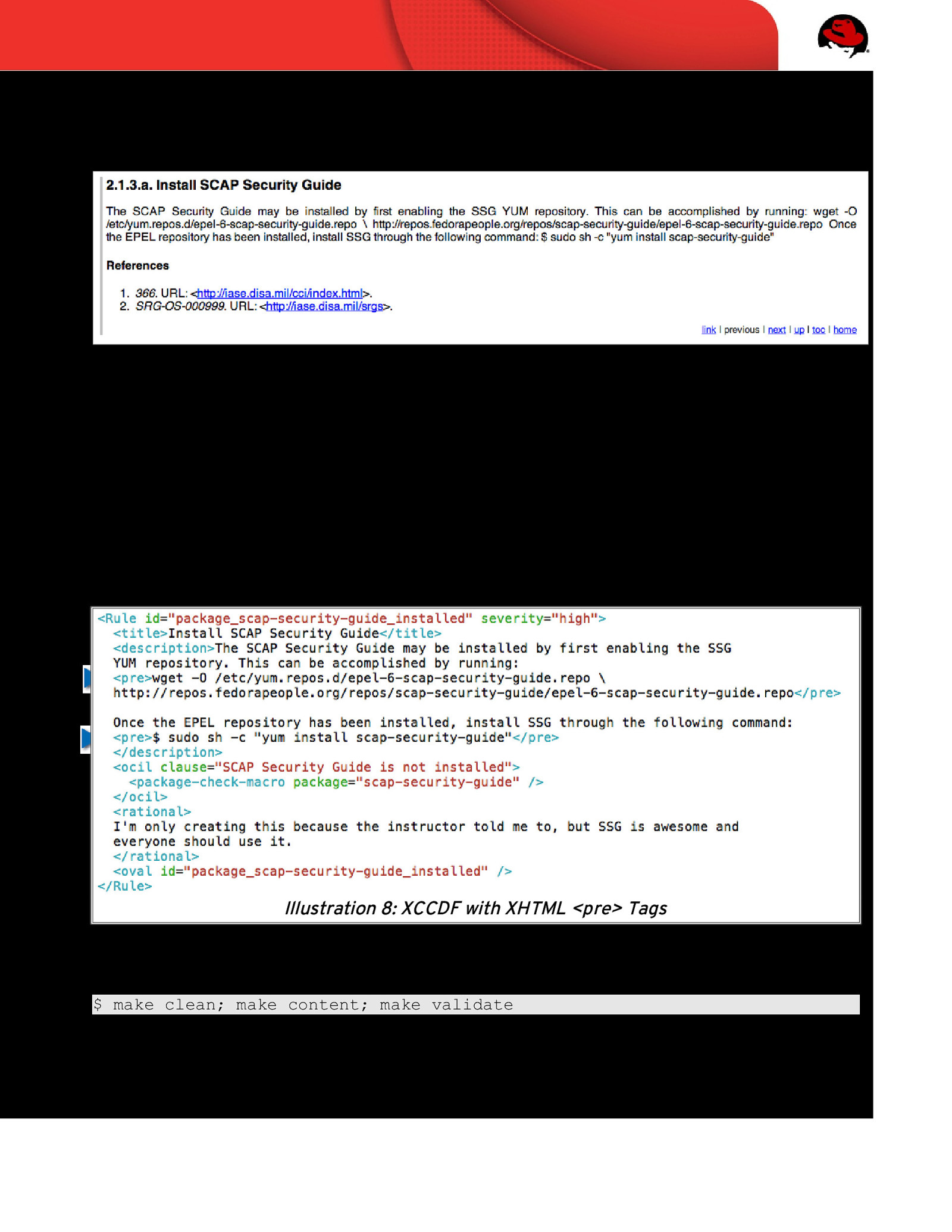
Click on the Install SCAP Security Guide link, and you’ll be brought to the newly created rule: You’ll notice a few things: 1. Rendering from your <description> tag isn’t pretty, and line returns didn’t keep. 2. References against DISA CCI and DISA’s OS SRG were automatically added. When rules are not specifcally mapped to a CCI or OS SRG, these “catch all” placeholders are inserted. The <description> tag has the ability to handle XHTML arguments. Let’s wrap our sample commands in <pre> tags, and re-run the build. Your XCCDF rule should now look like this: Illustration 8: XCCDF with XHTML <pre> Tags Once updated, re-run the build: $ make clean; make content; make validate Page 32 of 42
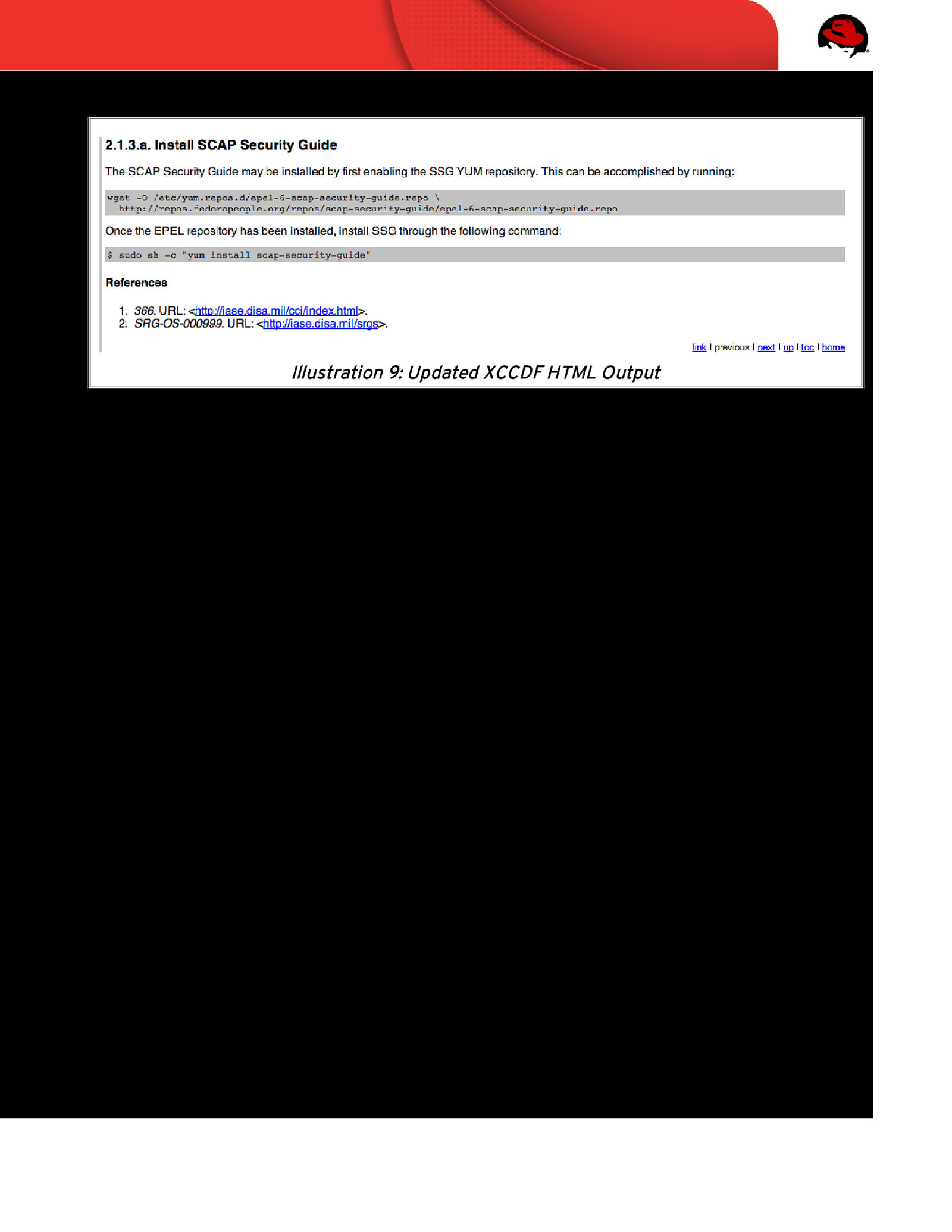
Upon completion, refresh your web browser to see the updated content: Illustration 9: Updated XCCDF HTML Output This looks much better. At this point we have a valid, functioning, XCCDF rule! Now, onto OVAL content creation… Page 33 of 42

5.5 OVAL Authoring OVAL standardizes the assessment and reporting of machine state. It’s very comprehensive, with capabilities to examine boot-time and run-time confguration. MITRE has documented OVAL’s built-in functions here: http://oval.mitre.org/language/version5.10.1/ovaldefnition/documentation/linuxdefnitions-schema.html The SSG project maintains all OVAL code under RHEL/6/input/checks/, and provides a template utilities in RHEL/6/input/checks/templates/. Change directories to templates/ and perform a directory listing: $ cd /var/www/html/scap-security-guide/RHEL/6/input/checks/templates/; ls create_kernel_modules_disabled.py packages_removed.csv create_package_installed.py README create_package_removed.py services_disabled.csv create_permission_checks.py services_enabled.csv create_services_disabled.py sysctl_values.csv create_services_enabled.py template_kernel_module_disabled create_sysctl_checks.py template_package_installed file_dir_permissions.csv template_package_removed find_untemplated.py template_permissions kernel_modules_disabled.csv template_service_disabled Makefile template_service_enabled output template_sysctl packages_installed.csv Before continuing to the next page, take a minute to review the README fle. What is the process to create a template for checking if scap-security-guide is installed? Page 34 of 42
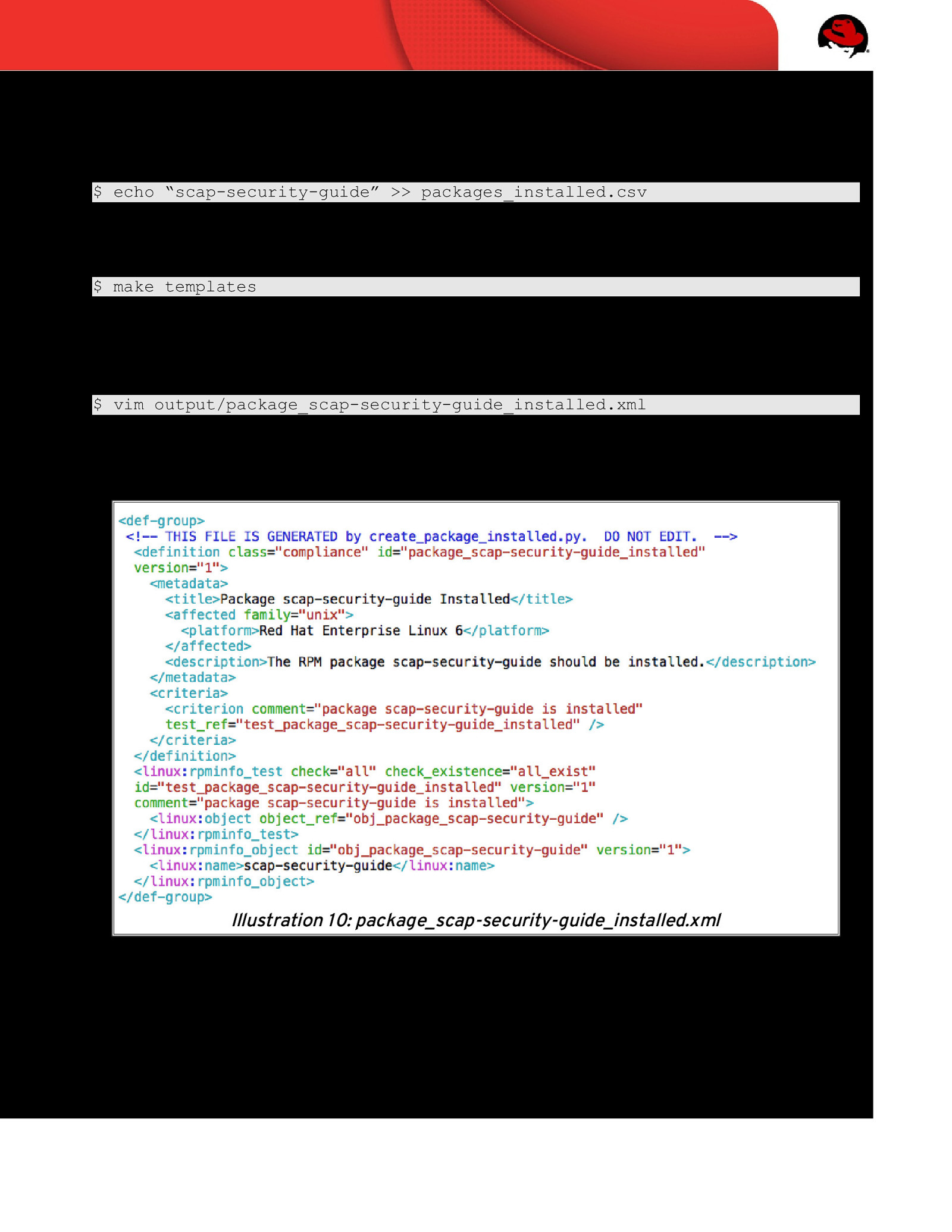
As noted in the README fle, several CSV fles are located within the templates/ directory. To automate the OVAL content: 1. Add scap-security-guide to the listing in packages_installed.csv: $ echo “scap-security-guide” >> packages_installed.csv 2. Run “make templates”: $ make templates 3. This process generated output/package_scap-securityguide_installed.xml. Load this fle in a text editor for human-review: $ vim output/package_scap-security-guide_installed.xml The newly created template: Illustration 10: package_scap-security-guide_installed.xml OVAL contains many pre-defned functions. In this case, we make use of linux:rpminfo_test to check for the installation of scap-security-guide. Page 35 of 42

- Run “make copy” to place package_scap-security-guide_installed.xml into the project: $ make copy
- Done! You’ve now added an OVAL rule to check for the existence of scapsecurity-guide! Page 36 of 42
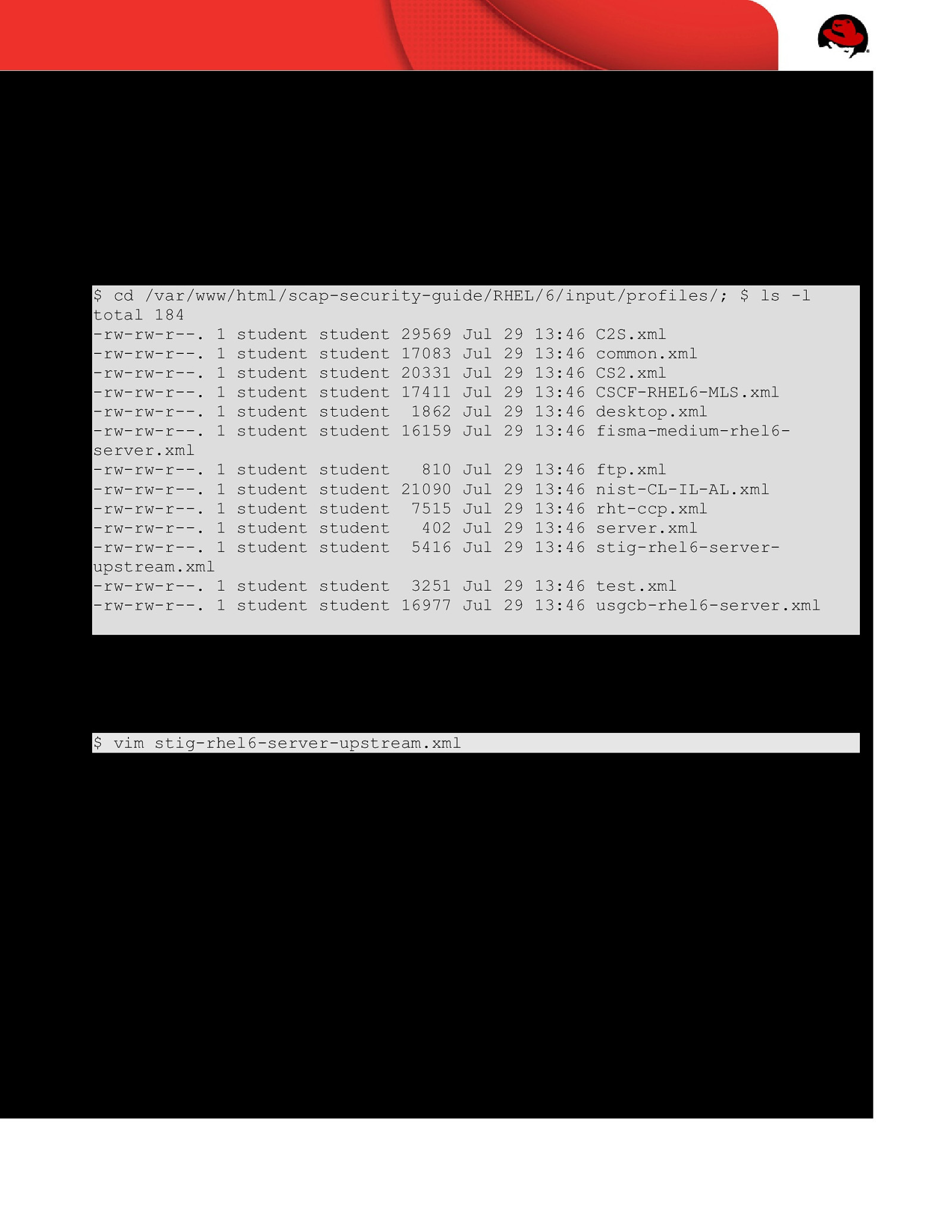
5.6 Profles With our XCCDF rule and OVAL content created, we must now add the rule to an XCCDF profle. Let’s add this as a STIG requirement, placing it into the stig-rhel6-server profle. XCCDF profles are retained within RHEL/6/input/profiles/. Change directory and perform a directory listing to see available profles: $ cd /var/www/html/scap-security-guide/RHEL/6/input/profiles/; $ ls -l total 184 -rw-rw-r—. 1 student student 29569 Jul 29 13:46 C2S.xml -rw-rw-r—. 1 student student 17083 Jul 29 13:46 common.xml -rw-rw-r—. 1 student student 20331 Jul 29 13:46 CS2.xml -rw-rw-r—. 1 student student 17411 Jul 29 13:46 CSCF-RHEL6-MLS.xml -rw-rw-r—. 1 student student 1862 Jul 29 13:46 desktop.xml -rw-rw-r—. 1 student student 16159 Jul 29 13:46 fisma-medium-rhel6server.xml -rw-rw-r—. 1 student student 810 Jul 29 13:46 ftp.xml -rw-rw-r—. 1 student student 21090 Jul 29 13:46 nist-CL-IL-AL.xml -rw-rw-r—. 1 student student 7515 Jul 29 13:46 rht-ccp.xml -rw-rw-r—. 1 student student 402 Jul 29 13:46 server.xml -rw-rw-r—. 1 student student 5416 Jul 29 13:46 stig-rhel6-serverupstream.xml -rw-rw-r—. 1 student student 3251 Jul 29 13:46 test.xml -rw-rw-r—. 1 student student 16977 Jul 29 13:46 usgcb-rhel6-server.xml Since we’re adding this rule to the STIG profle, load stig-rhel6-serverupstream.xml: $ vim stig-rhel6-server-upstream.xml Page 37 of 42
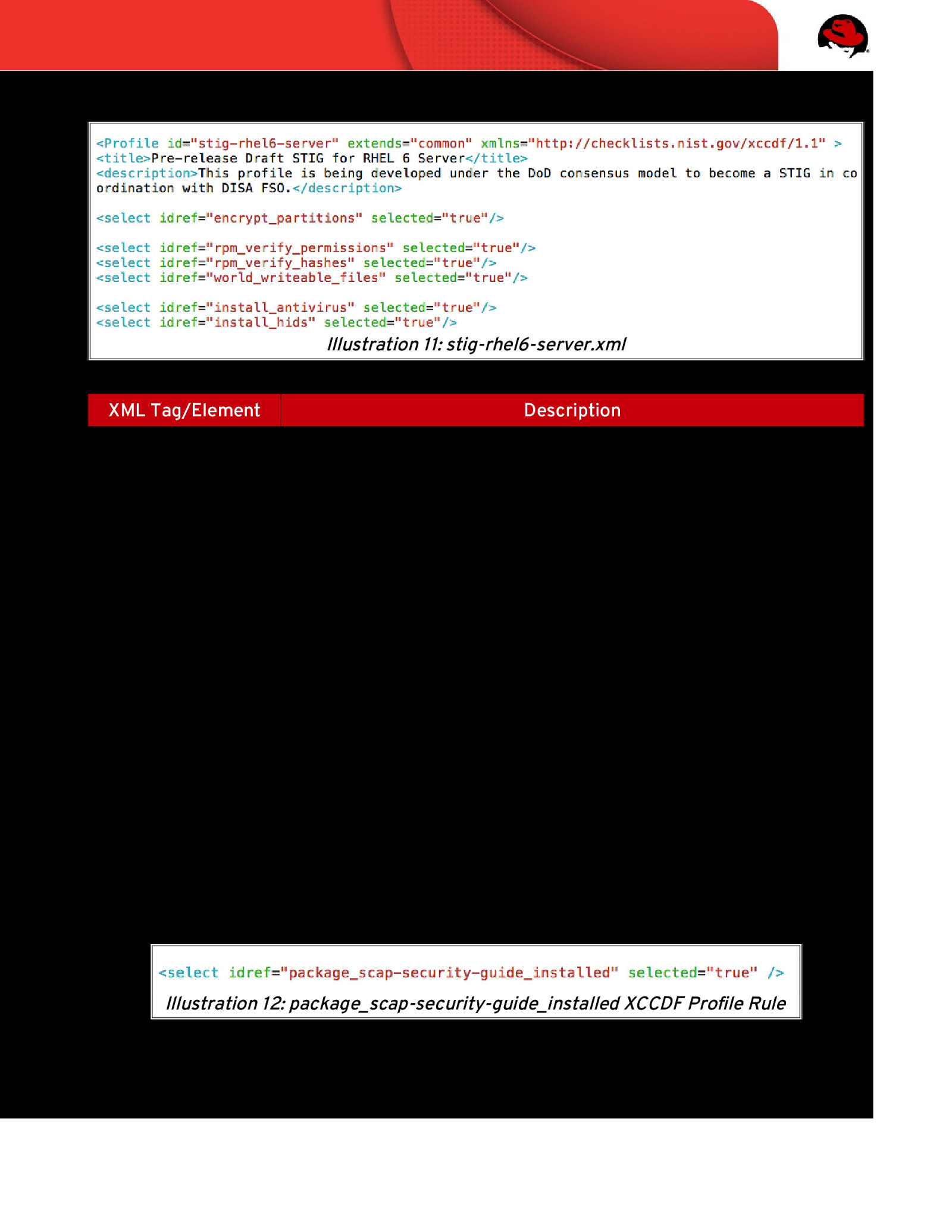
Upon loading the fle, you will be presented with the XCCDF code behind the STIG profle: Illustration 11: stig-rhel6-server.xml XML Tag/Element Description <Profile id=“…” XCCDF Profle Name
<title> XCCDF Rule Title <description> Brief description of the XCCDF profle <Profile… extends=“…” Name of XCCDF profle to inherit <select idref=“…” XCCDF rule to include or modify <select … selected=“…” Should this rule be enabled in the profle? True | False Particularly important when extending other XCCDF profles, allowing you to enable/disable rules from the parent source. Table 4: XCCDF Profle Tags Using the existing code as a reference: 1. Add the package_scap-security-guide_installed rule into the STIG profle 2. Ensure the rule is selected If added correctly, you will have inserted a line that matches the following: Illustration 12: package_scap-security-guide_installed XCCDF Profle Rule Page 38 of 42
5.7 Patch Creation & Submission Throughout this workshop, we’ve made several modifcations to the SSG source code. Specifcally: 1. Creation of a new XCCDF rule, package_scap-security-guide_installed, which was placed into RHEL6/input/system/software/integrity.xml. 2. Creation of a new OVAL rule, package_scap-security-guide_installed.xml, which also involved updating the OVAL template fle RHEL6/input/checks/templates/packages_installed.csv. 3. Modifcation of the STIG profle, located at RHEL6/input/profiles/stig-rhel6server-upstream.xml. We must now prepare our changes for submission back to the community, in the form of a patch. Change directories to /var/www/html/scap-security-guide/ and run “git commit”: $ cd /var/www/html/scap-security-guide/; git commit # On branch master # # Changed but not updated: # (use “git add <file>…” to update what will be committed) # (use “git checkout — <file>…” to discard changes in working directory) # # modified: RHEL6/input/checks/templates/packages_installed.csv # modified: RHEL6/input/profiles/stig-rhel6-server-upstream.xml # modified: RHEL6/input/system/software/integrity.xml # # Untracked files: # (use “git add <file>…” to include in what will be committed) # # RHEL6/input/checks/package_scap-security-guide_installed.xml no changes added to commit (use “git add” and/or “git commit -a”) From the output above, our patch must refect changes to the “modifed” fles and include the net-new “untracked” fle. To do so, run the following commands: $ git add RHEL6/input/checks/package_scap-security-guide_installed.xml $ git commit RHEL6/input/checks/templates/packages_installed.csv \ RHEL6/input/profiles/stig-rhel6-server.xml \ RHEL6/input/system/software/integrity.xml \ RHEL6/input/checks/package_scap-security-guide_installed.xml Page 39 of 42
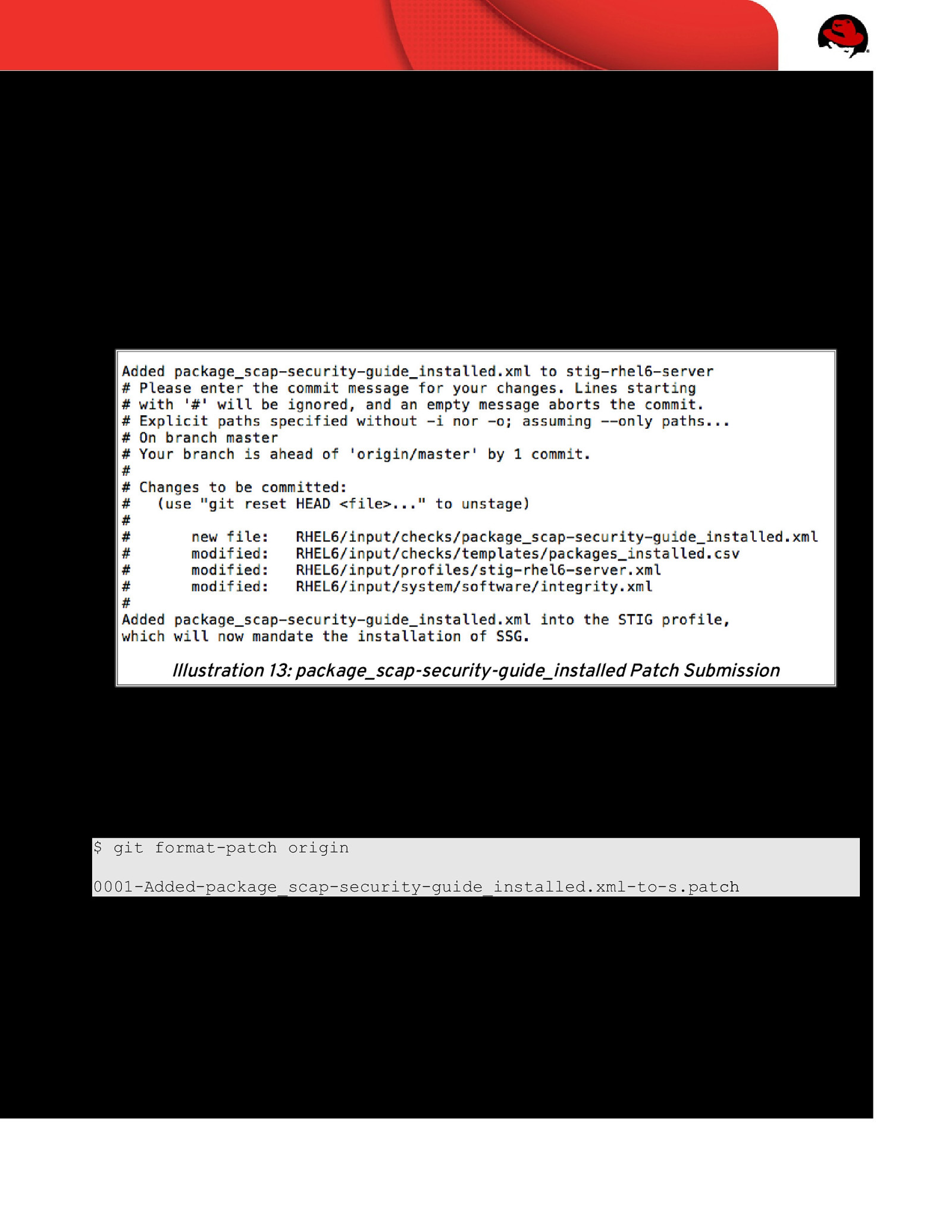
The “git commit” command will bring you into a vi editor, prompting you to enter details of your patch. The frst line, which is the default location of your cursor at this point, is where to create the patch title. At the EOF you place details of the patch. Edit your patch content to refect: • Patch title of “Added package_scap-security-guide_installed.xml to stig-rhel6-server profle” • Patch description of “Added package_scap-security-guide_installed.xml into STIG profle, which will now mandate the installation of the SSG” When done, your window will resemble the following: Illustration 13: package_scap-security-guide_installed Patch Submission Once complete, save and exit (:wq). Your local source tree has now identifed and grouped your changes into a consolidated patch. Using the git utility, we must “export” these changes in the format of a patch fle. To do so, run the following command: $ git format-patch origin 0001-Added-package_scap-security-guide_installed.xml-to-s.patch A newly created fle, 0001-Added-package_scap-security-guide_installed.xmlto-s.patch, will be placed into your working directory. The fnal step is to email this patch to the SSG project mailing list. Upon acknowledgement/signoff, you will be able to “git push” your changes into the project. Page 40 of 42
6 REFERENCES National Institute of Standards and Technology, Security Content Automation Protocol http://scap.nist.gov/ National Security Agency, Guide to the Secure Confguration of Red Hat Enterprise Linux 5 http://www.nsa.gov/ia/_fles/os/redhat/rhel5-guide-i731.pdf SCAP Security Guide Project https://fedorahosted.org/scap-security-guide/ Defense Information Systems Agency, Security Technical Implementation Guide for Red Hat Enterprise Linux 6 http://iase.disa.mil/stigs/os/unix/red_hat.html Page 41 of 42

Page 42 of 42
Student workbook as used in the SCAP & STIG Workshop at Defense in Depth 2014.
