Red Hat Security Seminar Shawn D. Wells (swells@redhat.com) Solutions Architect, Federal
Slide 1

Slide 2
Agenda Start: 10:30 am End: 1:00 pm, ish Red Hat Emerging Technologies Virtualization Security/MLS/Common Criteria High Availability Red Hat Security Future Direction (Emerging Technologies) Summary & Close 2
Slide 3
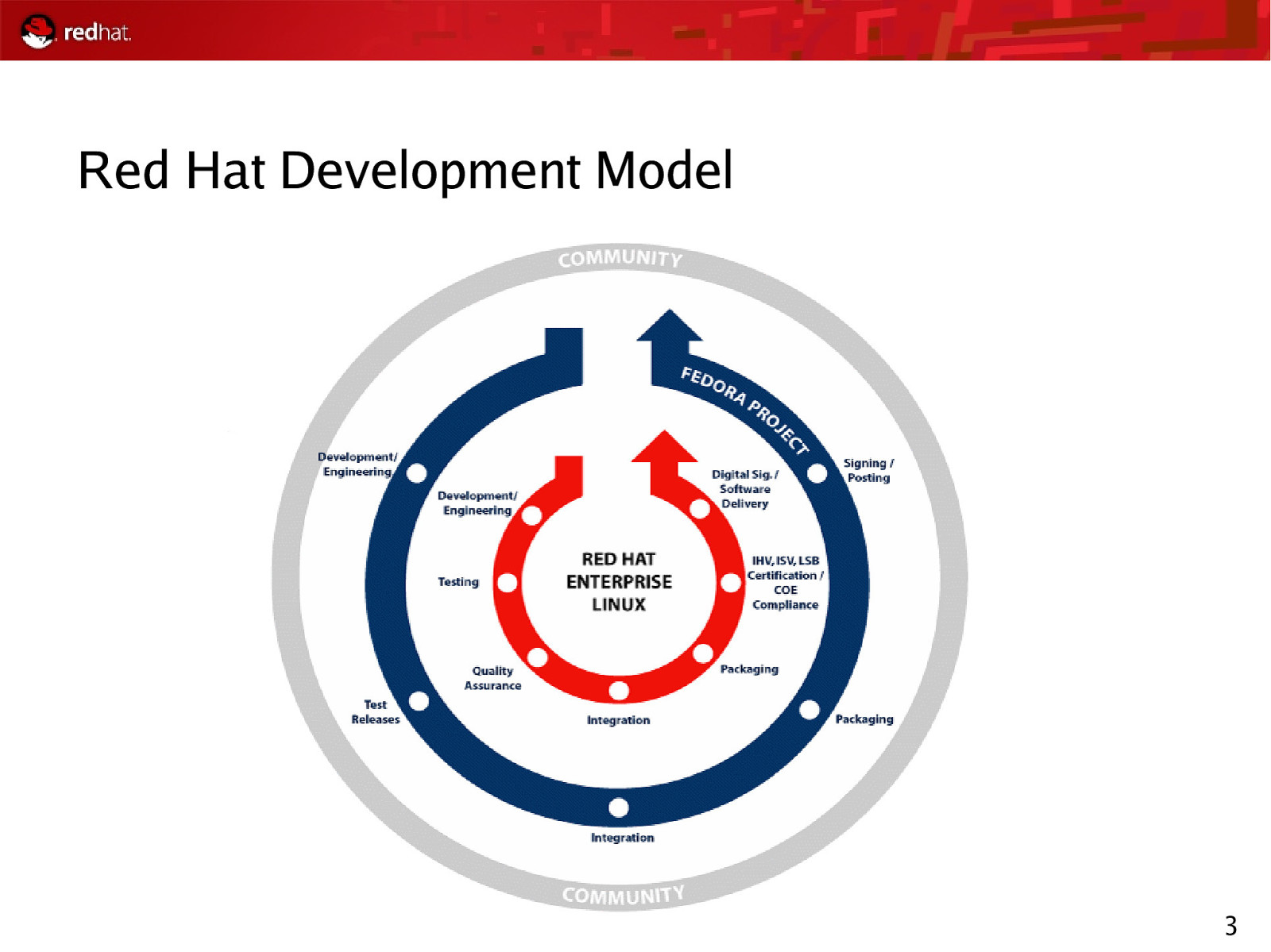
Red Hat Development Model 3
Slide 4

Red Hat Emerging Technologies
Slide 5
5
Slide 6
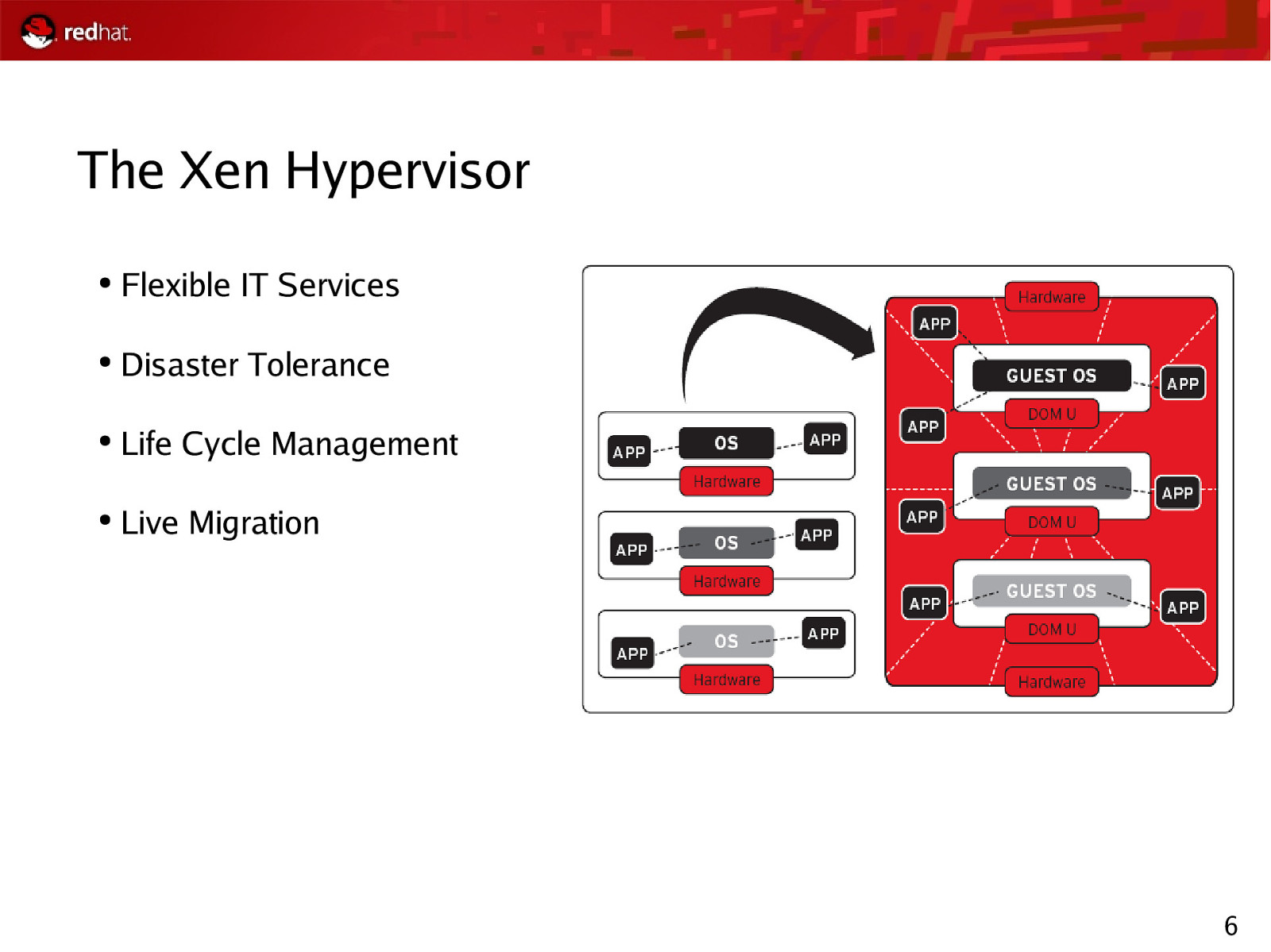
The Xen Hypervisor ● Flexible IT Services ● Disaster Tolerance ● Life Cycle Management ● Live Migration 6
Slide 7
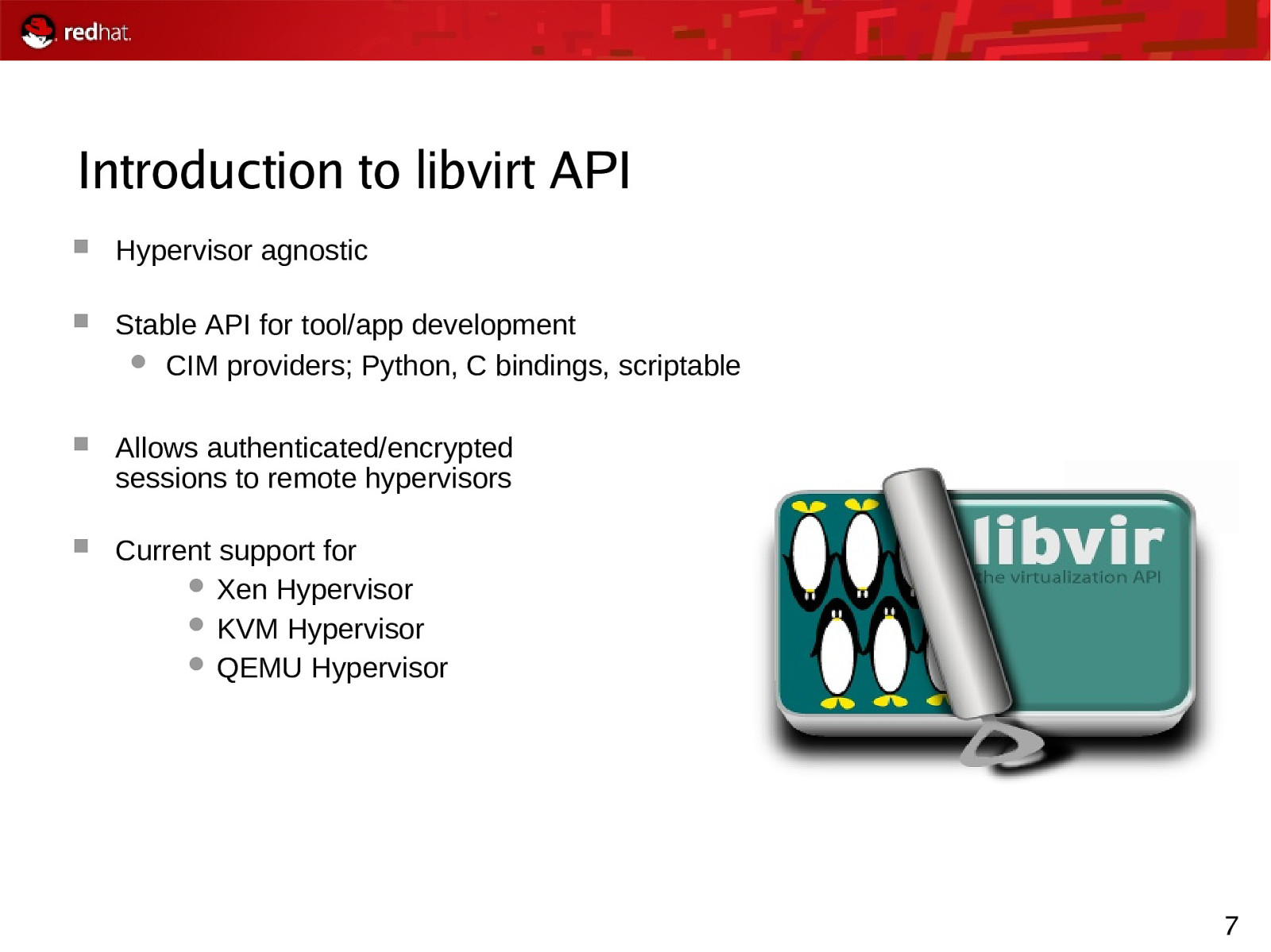
Introduction to libvirt API Hypervisor agnostic Stable API for tool/app development CIM providers; Python, C bindings, scriptable Allows authenticated/encrypted sessions to remote hypervisors Current support for Xen Hypervisor KVM Hypervisor QEMU Hypervisor 7
Slide 8
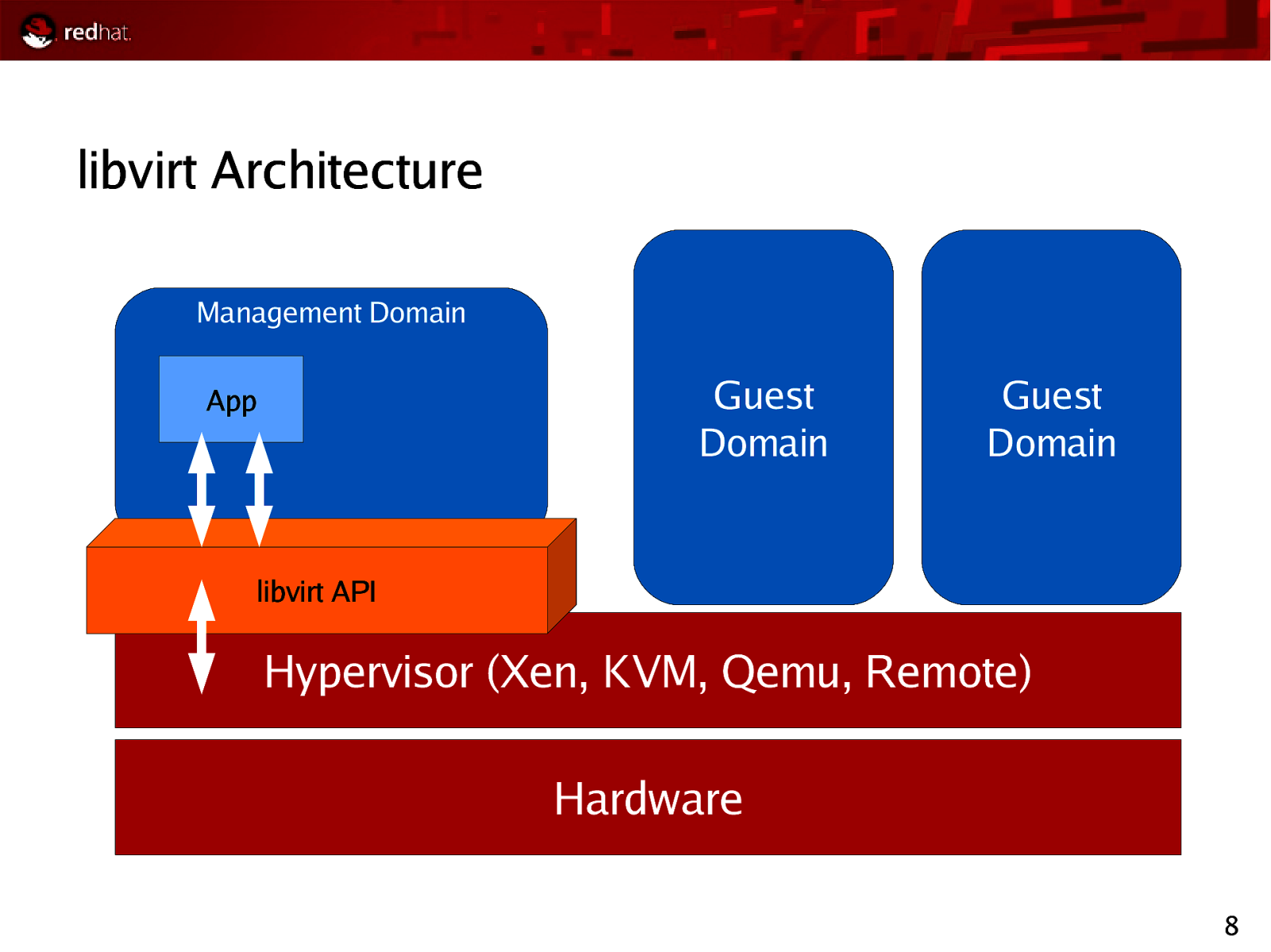
libvirt Architecture Management Domain Guest Domain App Guest Domain libvirt API Hypervisor (Xen, KVM, Qemu, Remote) Hardware 8
Slide 9
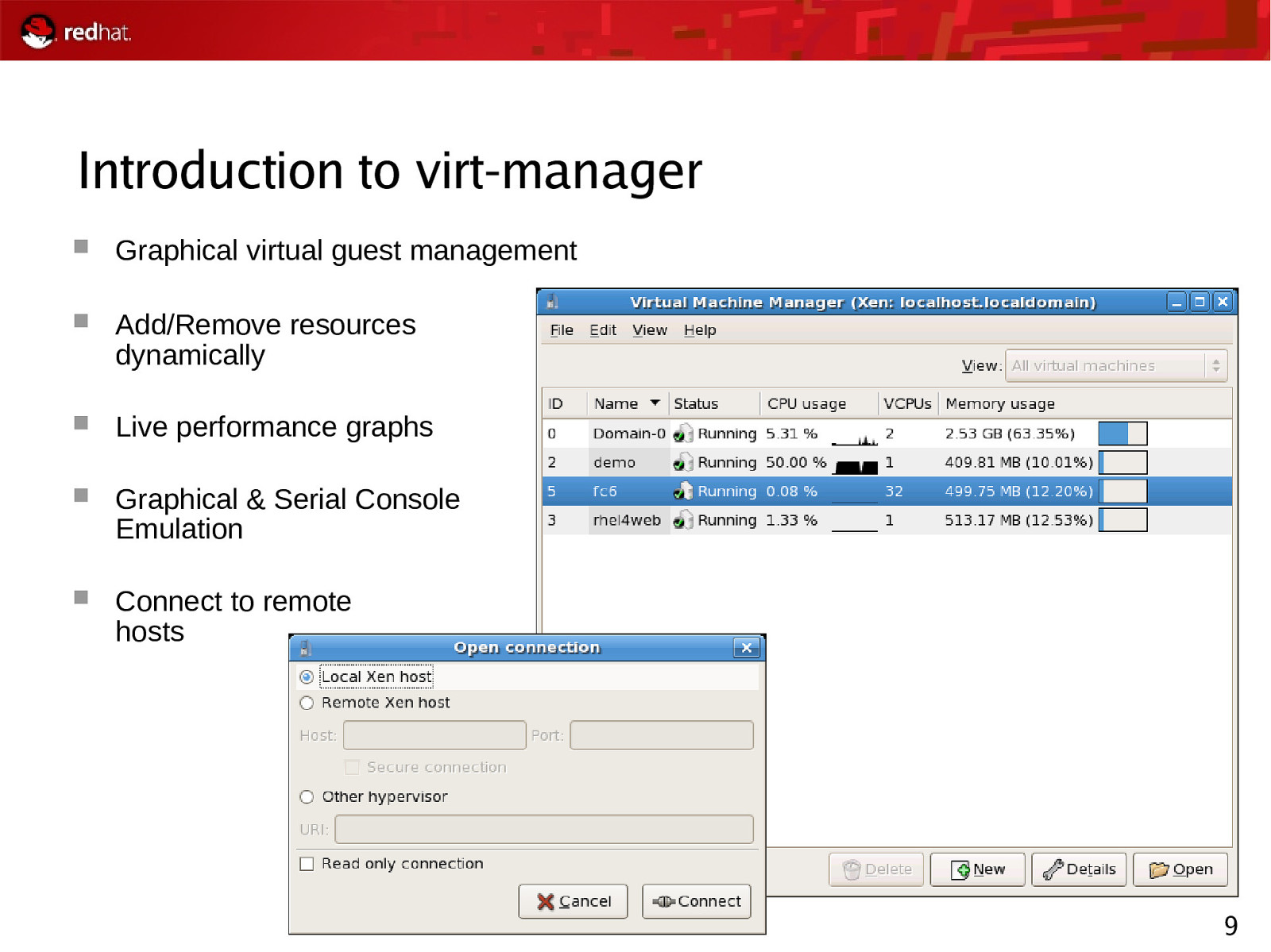
Introduction to virt-manager Graphical virtual guest management Add/Remove resources dynamically Live performance graphs Graphical & Serial Console Emulation Connect to remote hosts 9
Slide 10
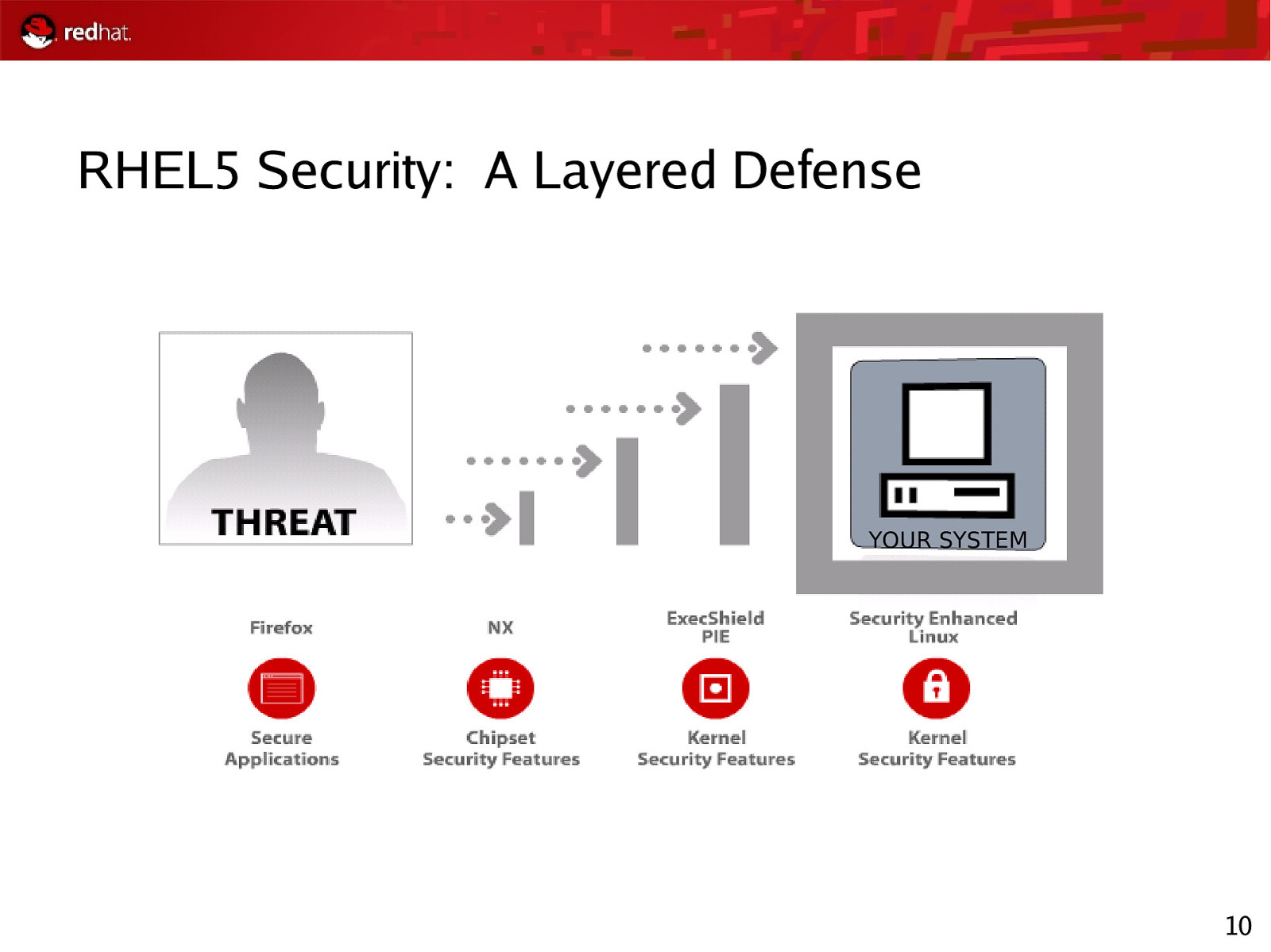
RHEL5 Security: A Layered Defense YOUR SYSTEM 10
Slide 11
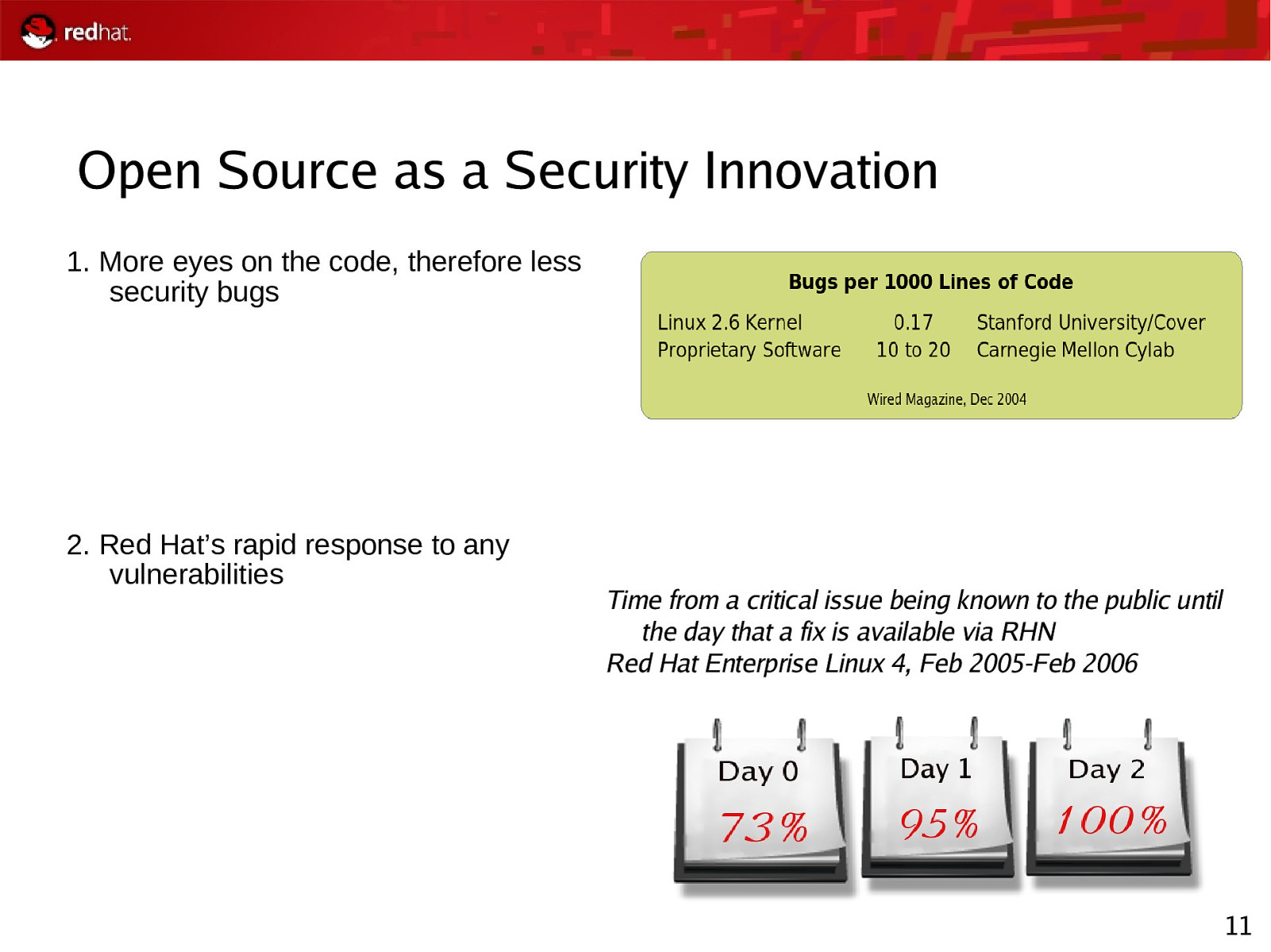
Open Source as a Security Innovation 1. More eyes on the code, therefore less security bugs 2. Red Hat’s rapid response to any vulnerabilities Time from a critical issue being known to the public until the day that a fix is available via RHN Red Hat Enterprise Linux 4, Feb 2005-Feb 2006 11
Slide 12
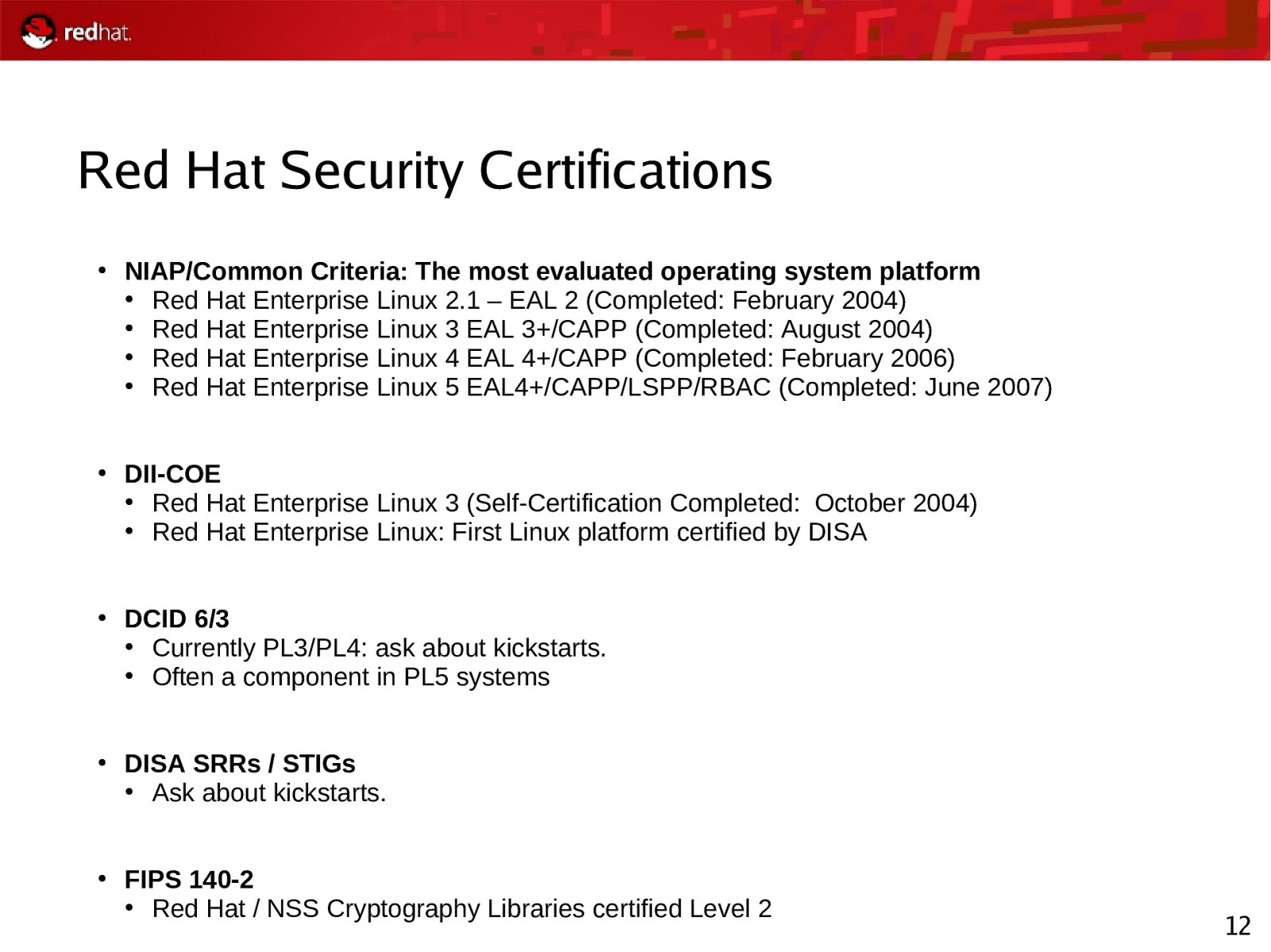
Red Hat Security Certifications ● ● ● ● ● NIAP/Common Criteria: The most evaluated operating system platform ● Red Hat Enterprise Linux 2.1 – EAL 2 (Completed: February 2004) ● Red Hat Enterprise Linux 3 EAL 3+/CAPP (Completed: August 2004) ● Red Hat Enterprise Linux 4 EAL 4+/CAPP (Completed: February 2006) ● Red Hat Enterprise Linux 5 EAL4+/CAPP/LSPP/RBAC (Completed: June 2007) DII-COE ● Red Hat Enterprise Linux 3 (Self-Certification Completed: October 2004) ● Red Hat Enterprise Linux: First Linux platform certified by DISA DCID 6/3 ● Currently PL3/PL4: ask about kickstarts. ● Often a component in PL5 systems DISA SRRs / STIGs ● Ask about kickstarts. FIPS 140-2 ● Red Hat / NSS Cryptography Libraries certified Level 2 12
Slide 13
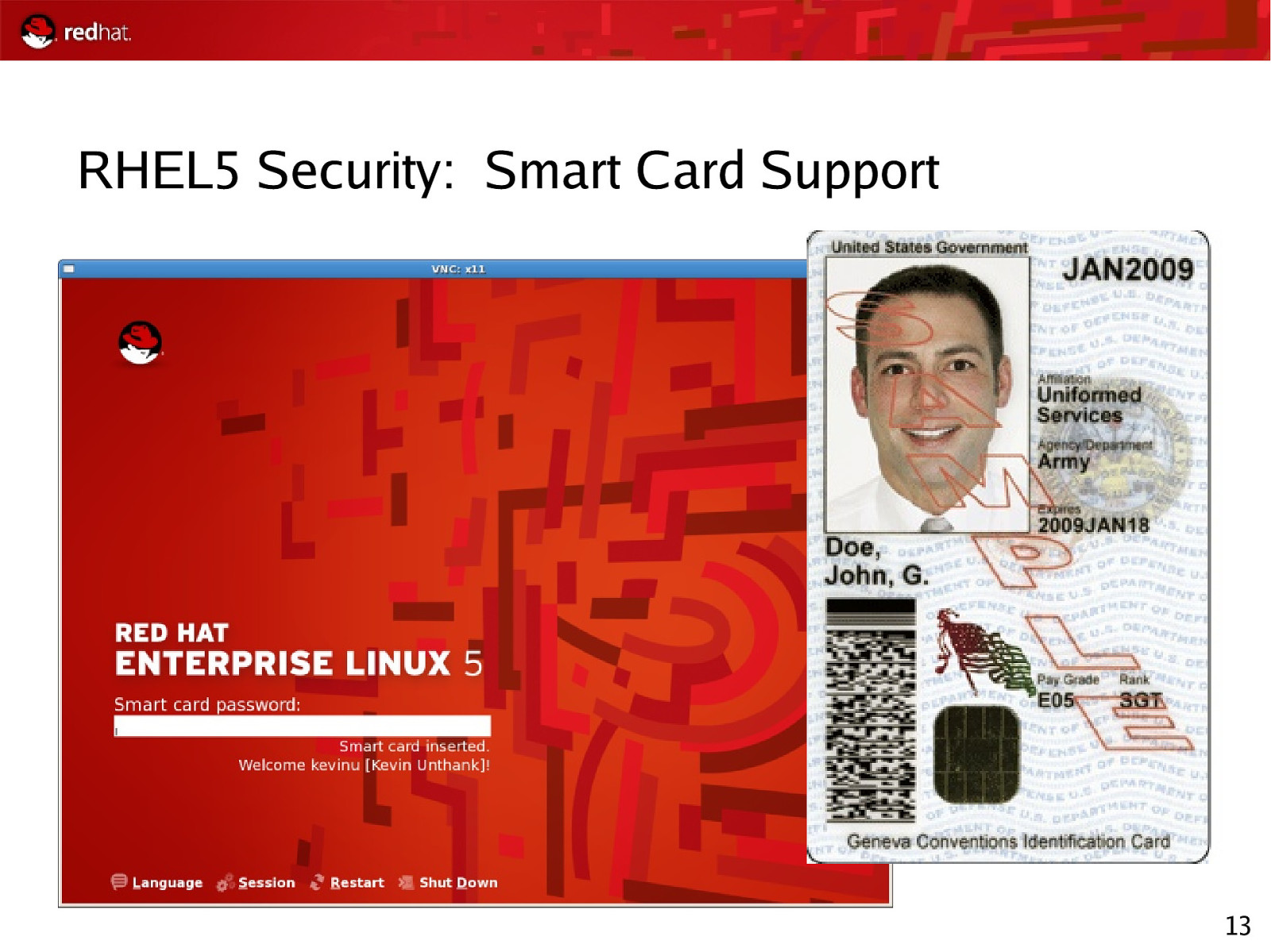
RHEL5 Security: Smart Card Support 13
Slide 14
RHEL5 Security: NIST Standards Work Extensible Configuration Checklist Description Format (XCCDF) Enumeration for configuration requirements DISA FSO committed to deploying STIG as XCCDF Others working with NIST Security policy becomes one file 14
Slide 15
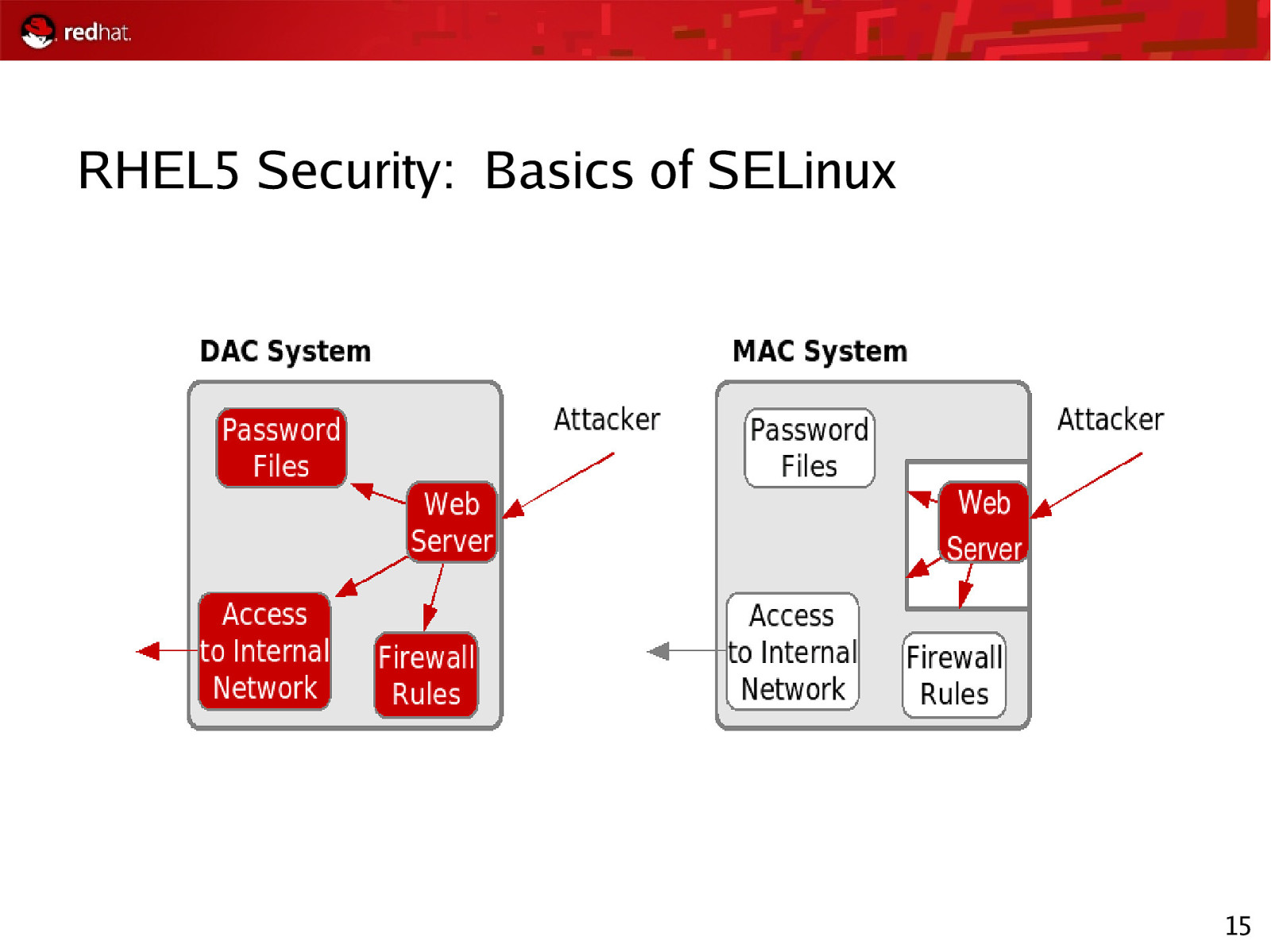
RHEL5 Security: Basics of SELinux 15
Slide 16
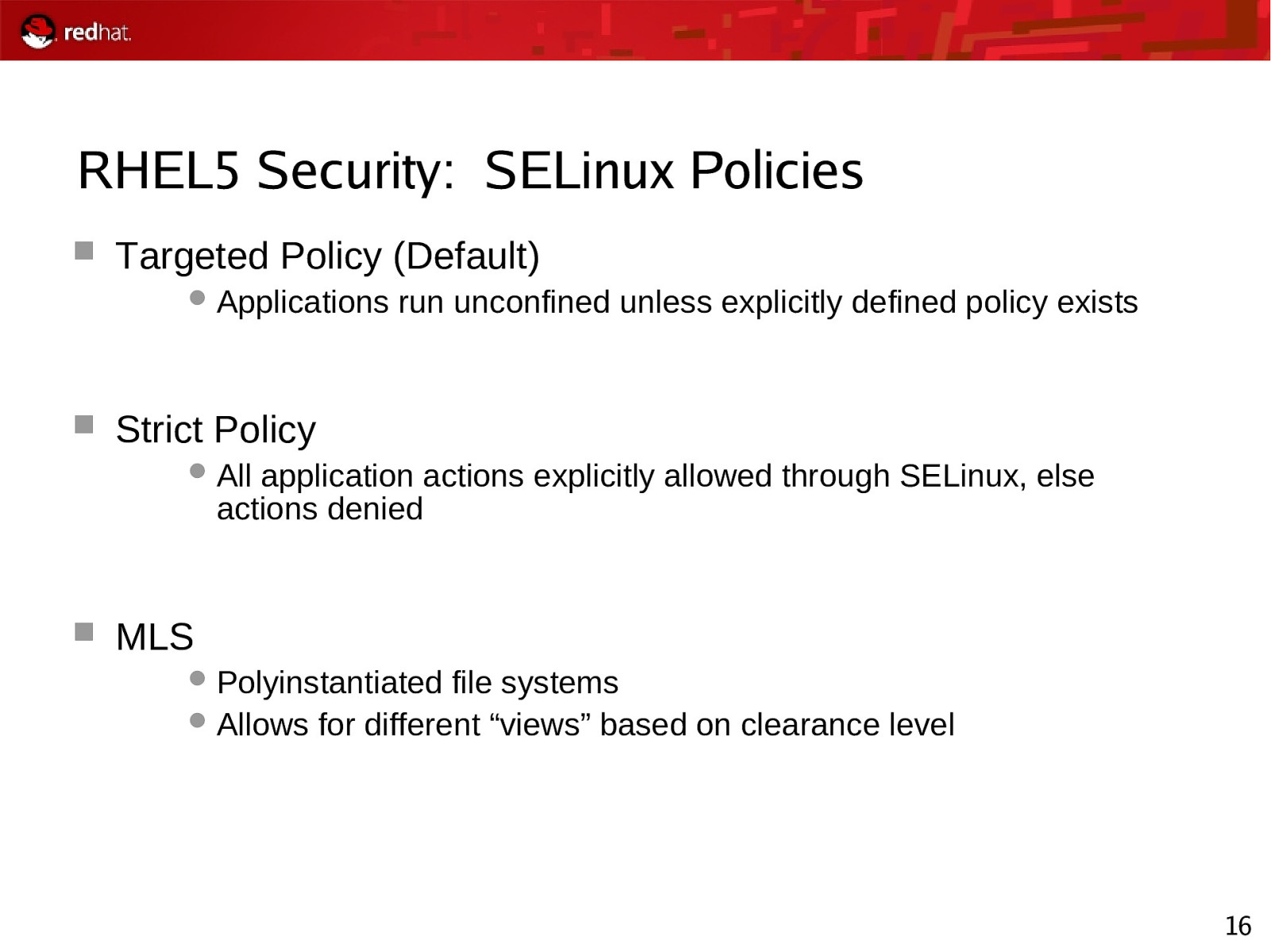
RHEL5 Security: SELinux Policies Targeted Policy (Default) Applications run unconfined unless explicitly defined policy exists Strict Policy All application actions explicitly allowed through SELinux, else actions denied MLS Polyinstantiated file systems Allows for different “views” based on clearance level 16
Slide 17
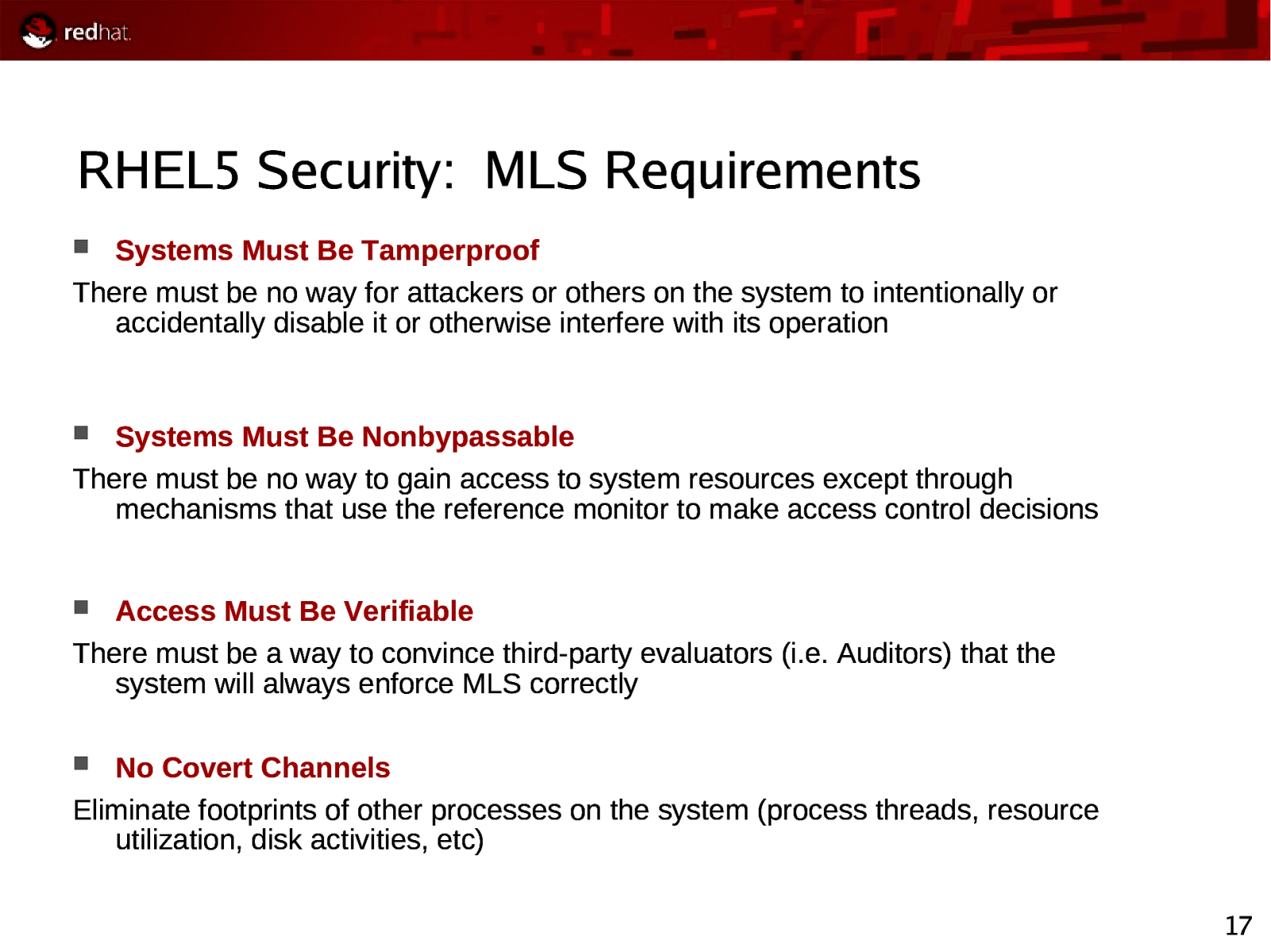
RHEL5 Security: MLS Requirements Systems Must Be Tamperproof There must be no way for attackers or others on the system to intentionally or accidentally disable it or otherwise interfere with its operation Systems Must Be Nonbypassable There must be no way to gain access to system resources except through mechanisms that use the reference monitor to make access control decisions Access Must Be Verifiable There must be a way to convince third-party evaluators (i.e. Auditors) that the system will always enforce MLS correctly No Covert Channels Eliminate footprints of other processes on the system (process threads, resource utilization, disk activities, etc) 17
Slide 18
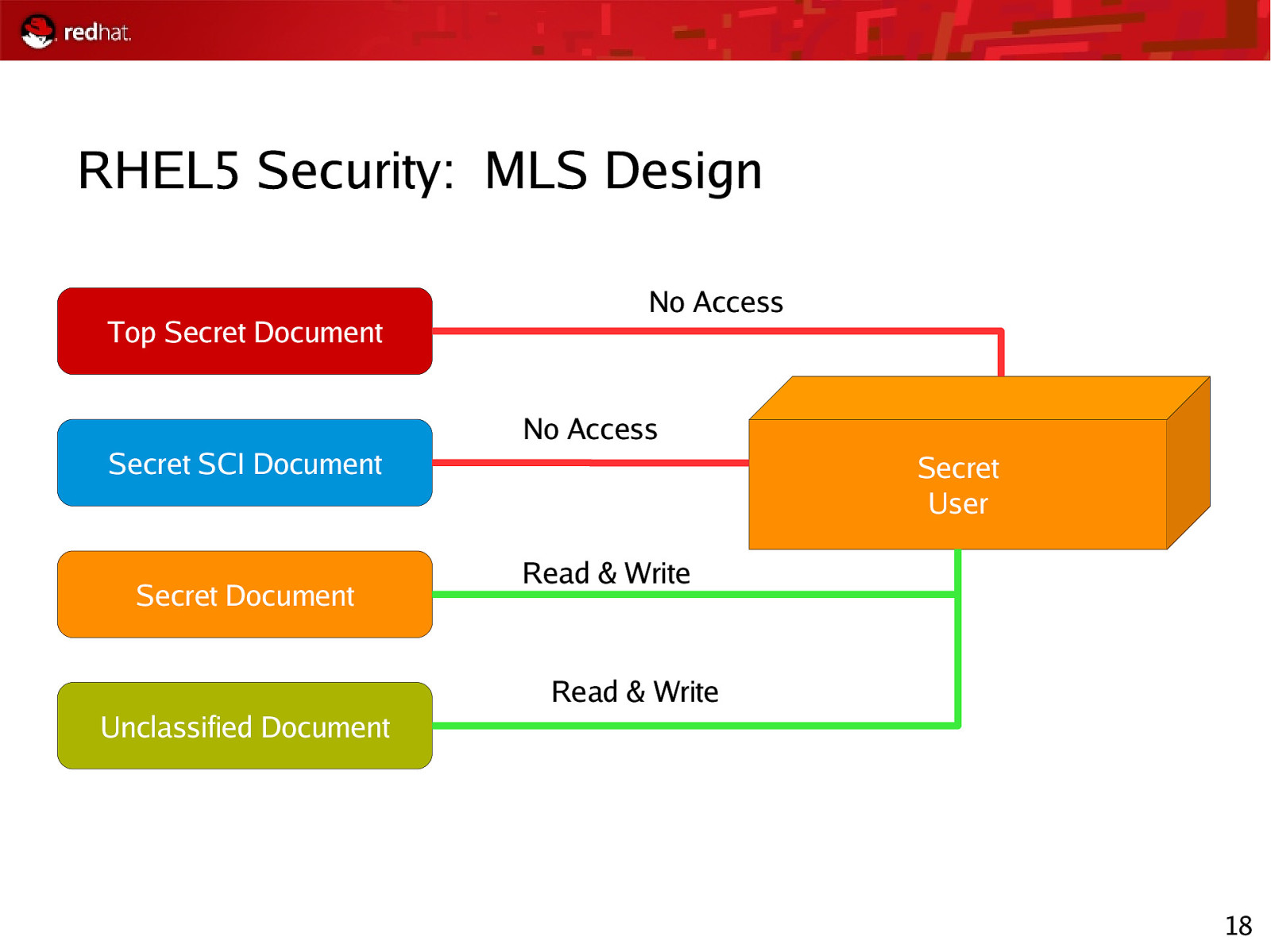
RHEL5 Security: MLS Design Top Secret Document No Access No Access Secret SCI Document Secret Document Secret User Read & Write Read & Write Unclassified Document 18
Slide 19
RHEL5 Security: Use of MLS Multi-Level Servers Servers implemented which connects to networks of differing classification, utilizing MLS for network traffic monitoring One-way Transfer (OWT) Devices with transfer from “low” to “high” Downgrading Guards Devices which transfer data in any direction between networks of differing classifications 19
Slide 20
RHEL5 SELinux Enhancements ● ● Expanded SELinux targeted policy coverage ● Provides coverage for all core system services, versus 11 in Red Hat Enterprise Linux 4 ● Includes support for Multi Level Security (MLS) enforcement model ● In addition to existing RBAC and TE models An additional level of protection against security exploits ● Fine-grained policies via kernel-enforced mandatory access controls ● Limits the scope of security vulnerabilities ● Beyond what any other general-purpose OS can deliver 20
Slide 21
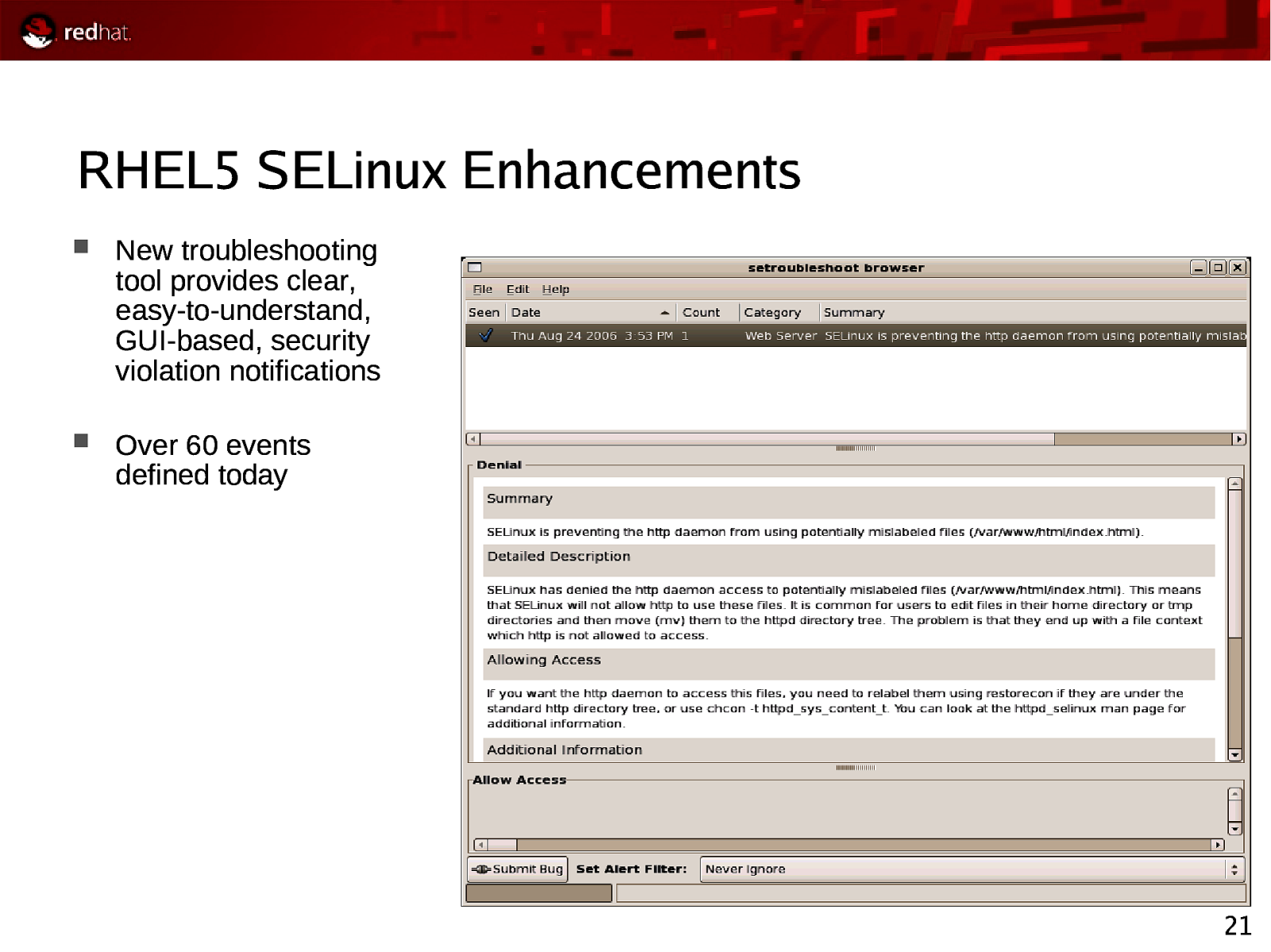
RHEL5 SELinux Enhancements New troubleshooting tool provides clear, easy-to-understand, GUI-based, security violation notifications Over 60 events defined today 21
Slide 22
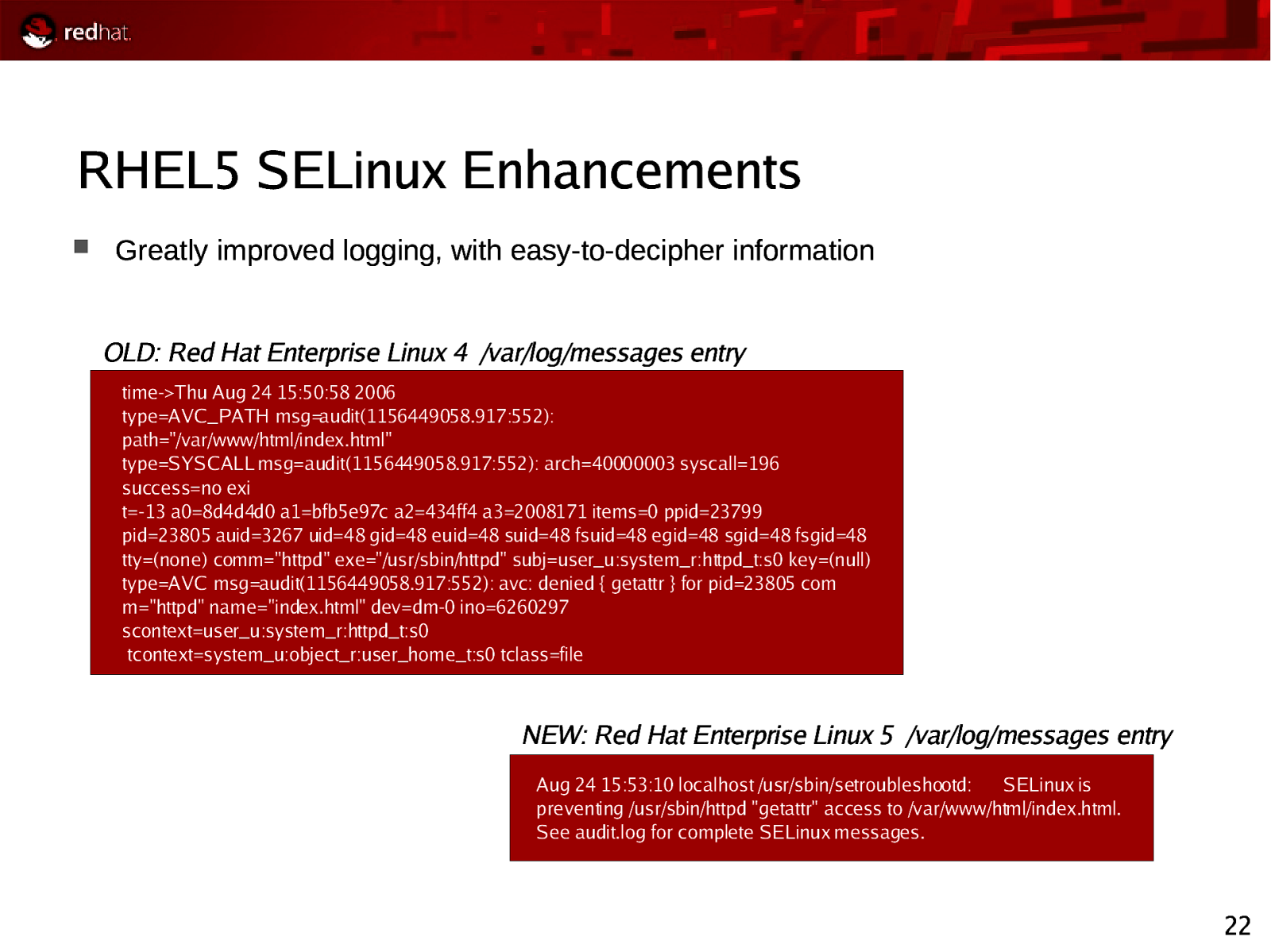
RHEL5 SELinux Enhancements Greatly improved logging, with easy-to-decipher information OLD: Red Hat Enterprise Linux 4 /var/log/messages entry time->Thu Aug 24 15:50:58 2006 type=AVC_PATH msg=audit(1156449058.917:552): path=”/var/www/html/index.html” type=SYSCALL msg=audit(1156449058.917:552): arch=40000003 syscall=196 success=no exi t=-13 a0=8d4d4d0 a1=bfb5e97c a2=434ff4 a3=2008171 items=0 ppid=23799 pid=23805 auid=3267 uid=48 gid=48 euid=48 suid=48 fsuid=48 egid=48 sgid=48 fsgid=48 tty=(none) comm=”httpd” exe=”/usr/sbin/httpd” subj=user_u:system_r:httpd_t:s0 key=(null) type=AVC msg=audit(1156449058.917:552): avc: denied { getattr } for pid=23805 com m=”httpd” name=”index.html” dev=dm-0 ino=6260297 scontext=user_u:system_r:httpd_t:s0 tcontext=system_u:object_r:user_home_t:s0 tclass=file NEW: Red Hat Enterprise Linux 5 /var/log/messages entry Aug 24 15:53:10 localhost /usr/sbin/setroubleshootd: SELinux is preventing /usr/sbin/httpd “getattr” access to /var/www/html/index.html. See audit.log for complete SELinux messages. 22
Slide 23
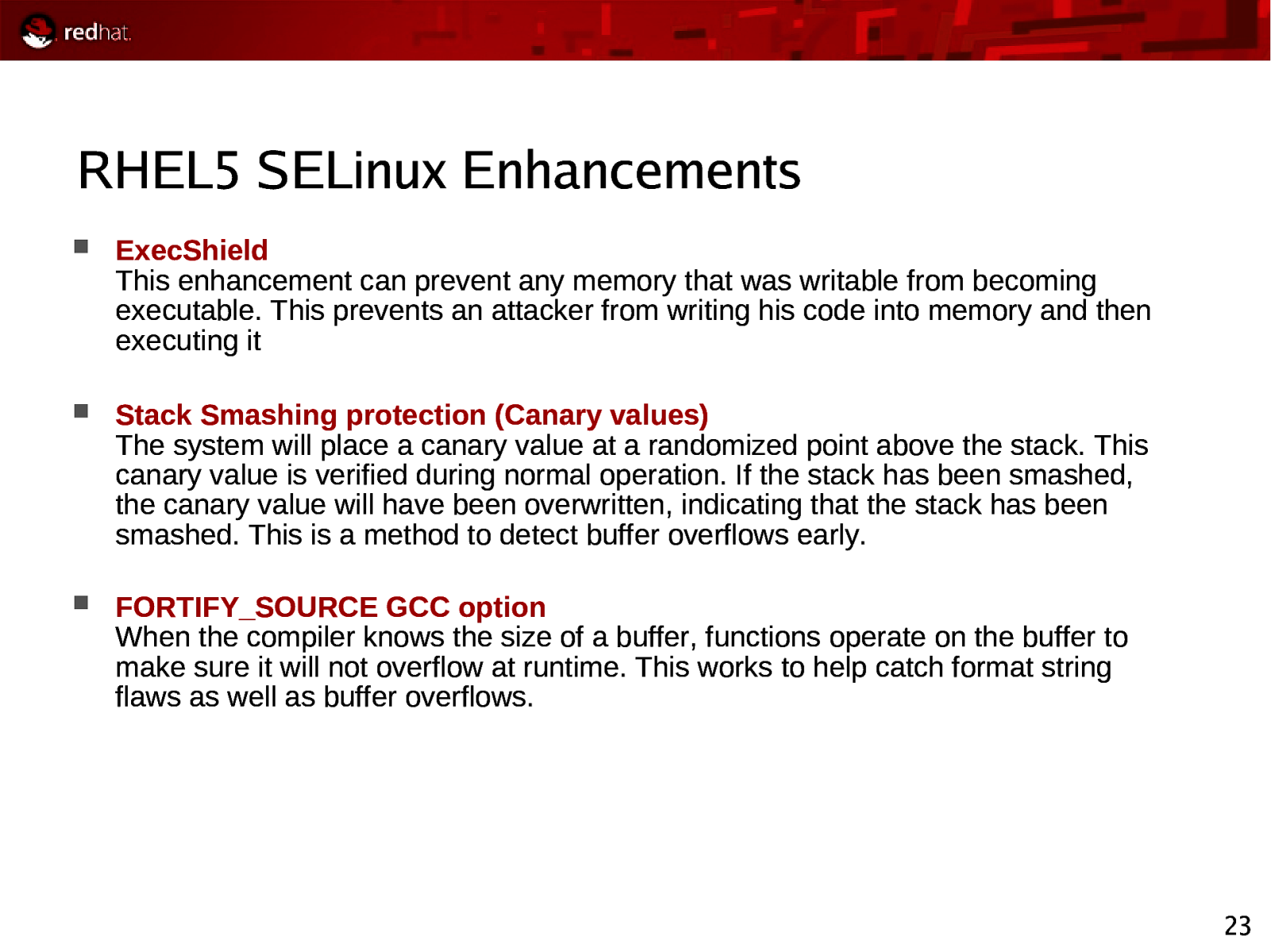
RHEL5 SELinux Enhancements ExecShield This enhancement can prevent any memory that was writable from becoming executable. This prevents an attacker from writing his code into memory and then executing it Stack Smashing protection (Canary values) The system will place a canary value at a randomized point above the stack. This canary value is verified during normal operation. If the stack has been smashed, the canary value will have been overwritten, indicating that the stack has been smashed. This is a method to detect buffer overflows early. FORTIFY_SOURCE GCC option When the compiler knows the size of a buffer, functions operate on the buffer to make sure it will not overflow at runtime. This works to help catch format string flaws as well as buffer overflows. 23
Slide 24
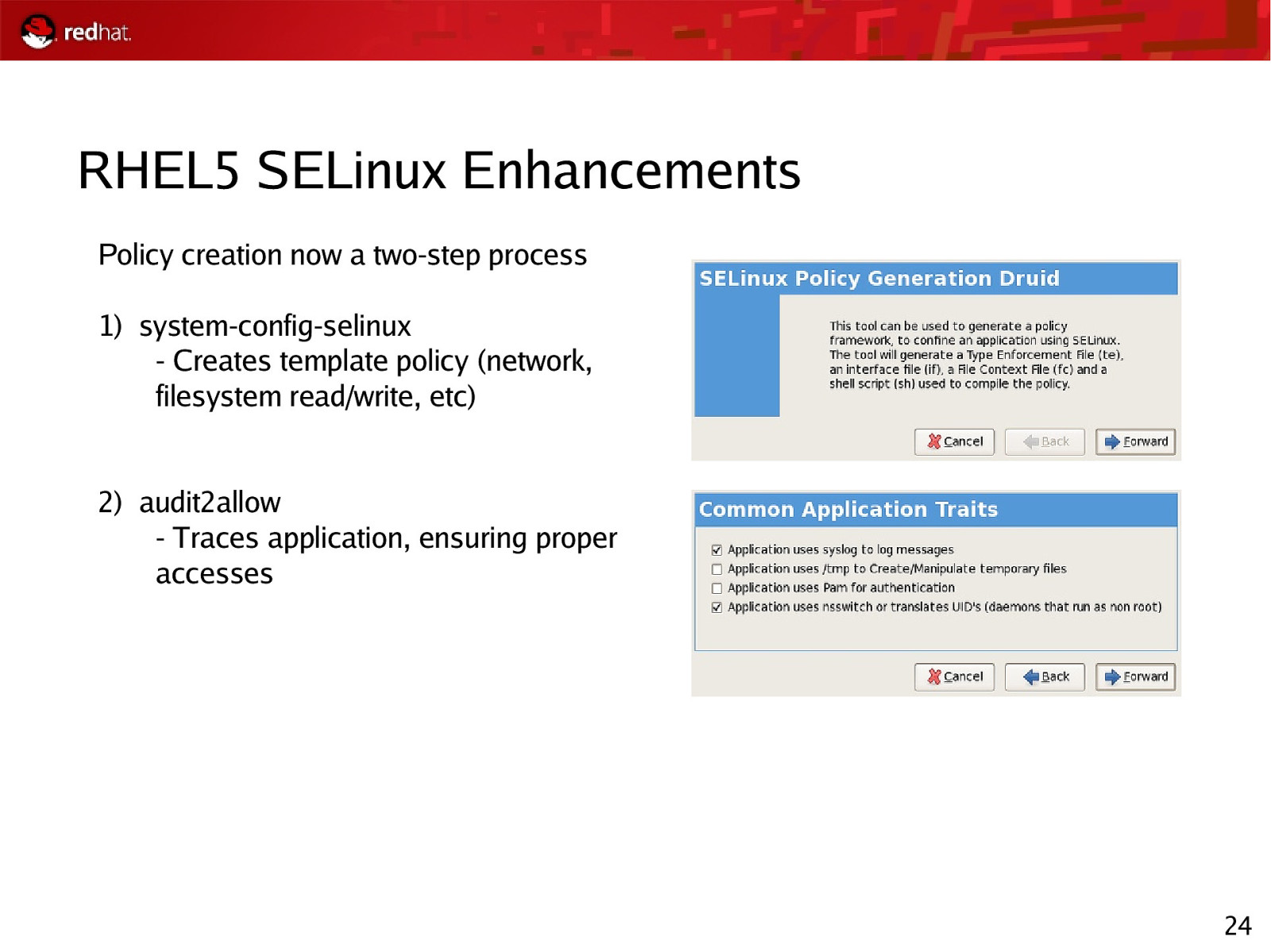
RHEL5 SELinux Enhancements Policy creation now a two-step process 1) system-config-selinux - Creates template policy (network, filesystem read/write, etc) 2) audit2allow - Traces application, ensuring proper accesses 24
Slide 25
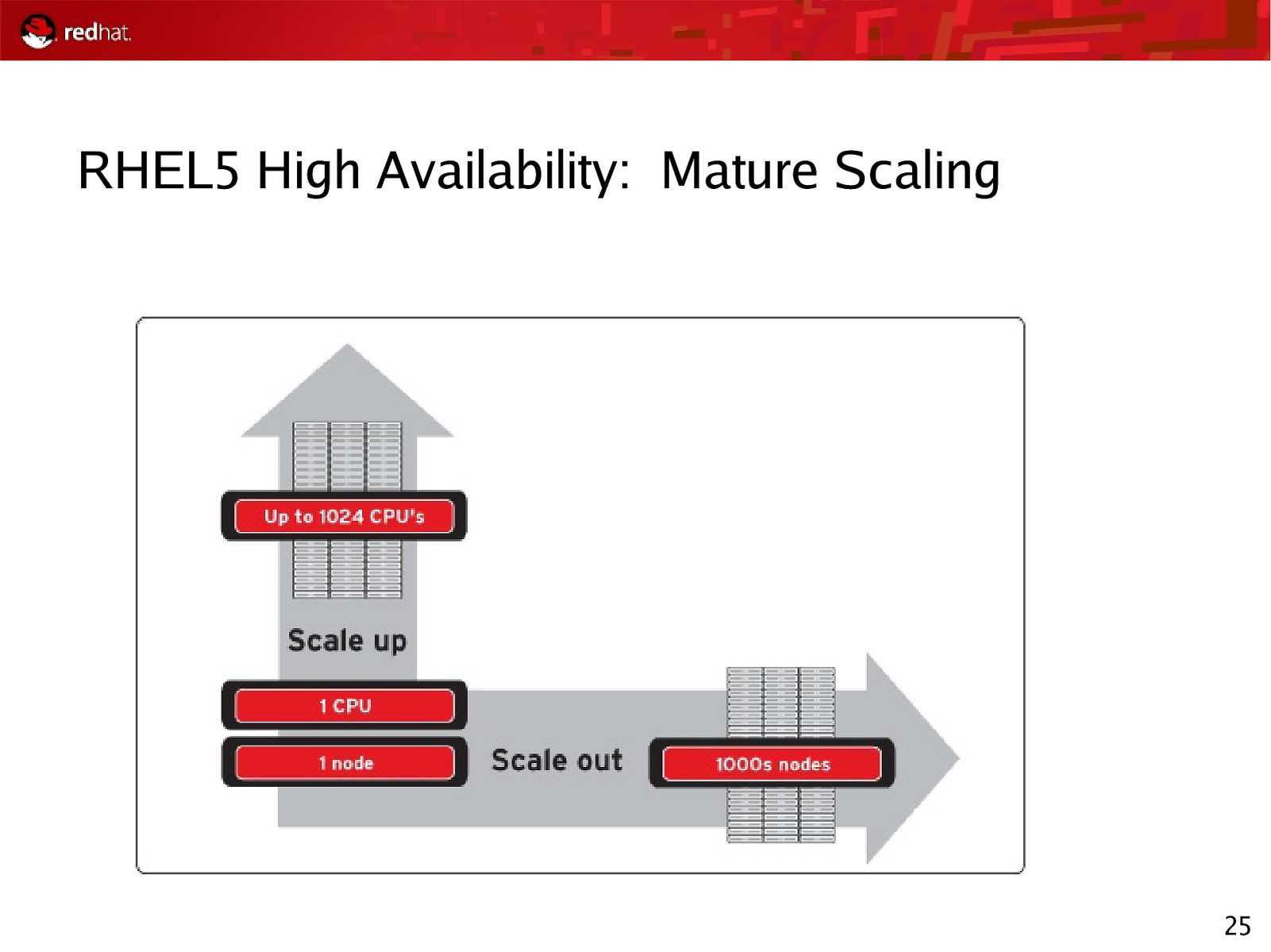
RHEL5 High Availability: Mature Scaling 25
Slide 26
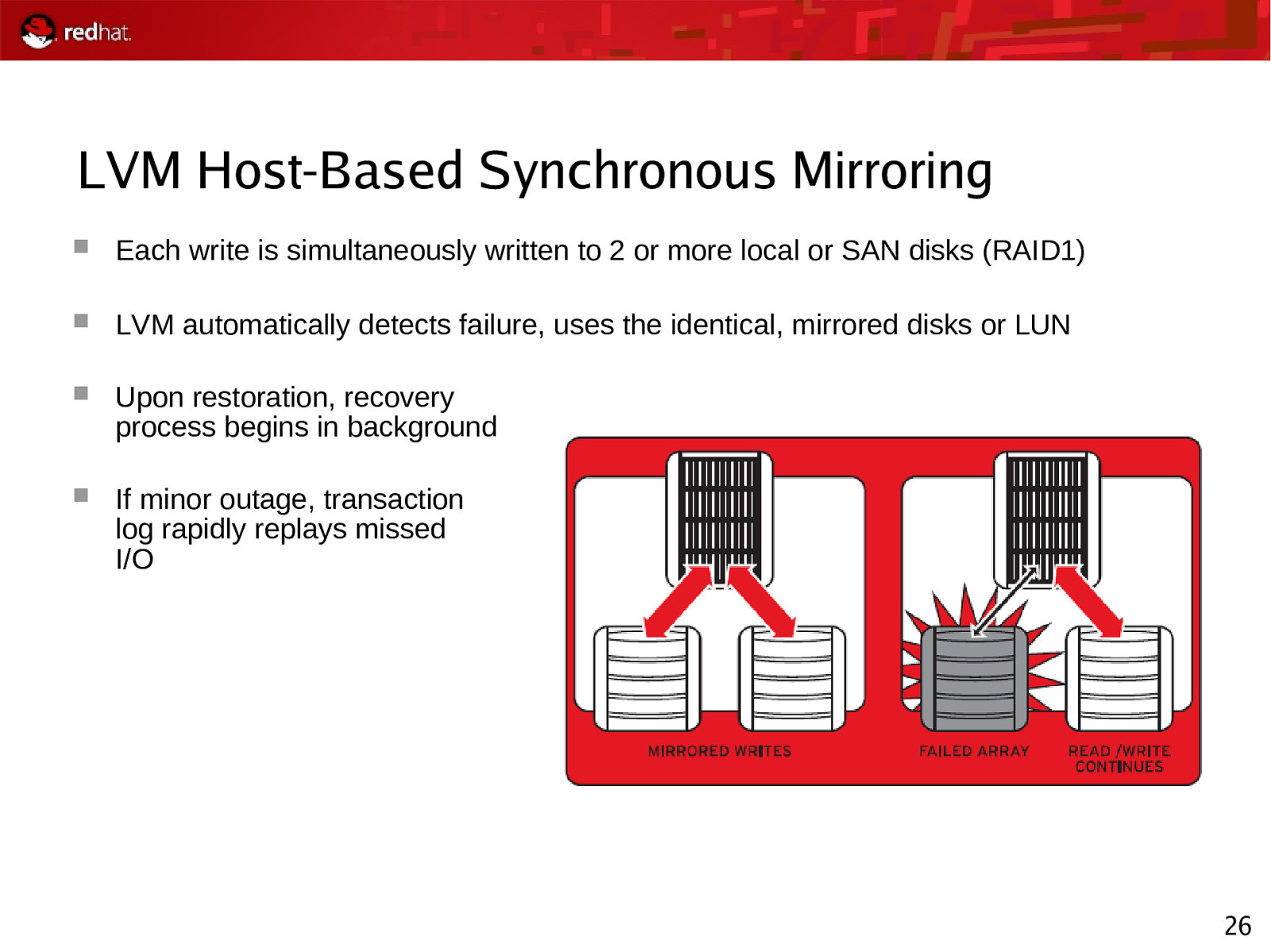
LVM Host-Based Synchronous Mirroring Each write is simultaneously written to 2 or more local or SAN disks (RAID1) LVM automatically detects failure, uses the identical, mirrored disks or LUN Upon restoration, recovery process begins in background If minor outage, transaction log rapidly replays missed I/O 26
Slide 27
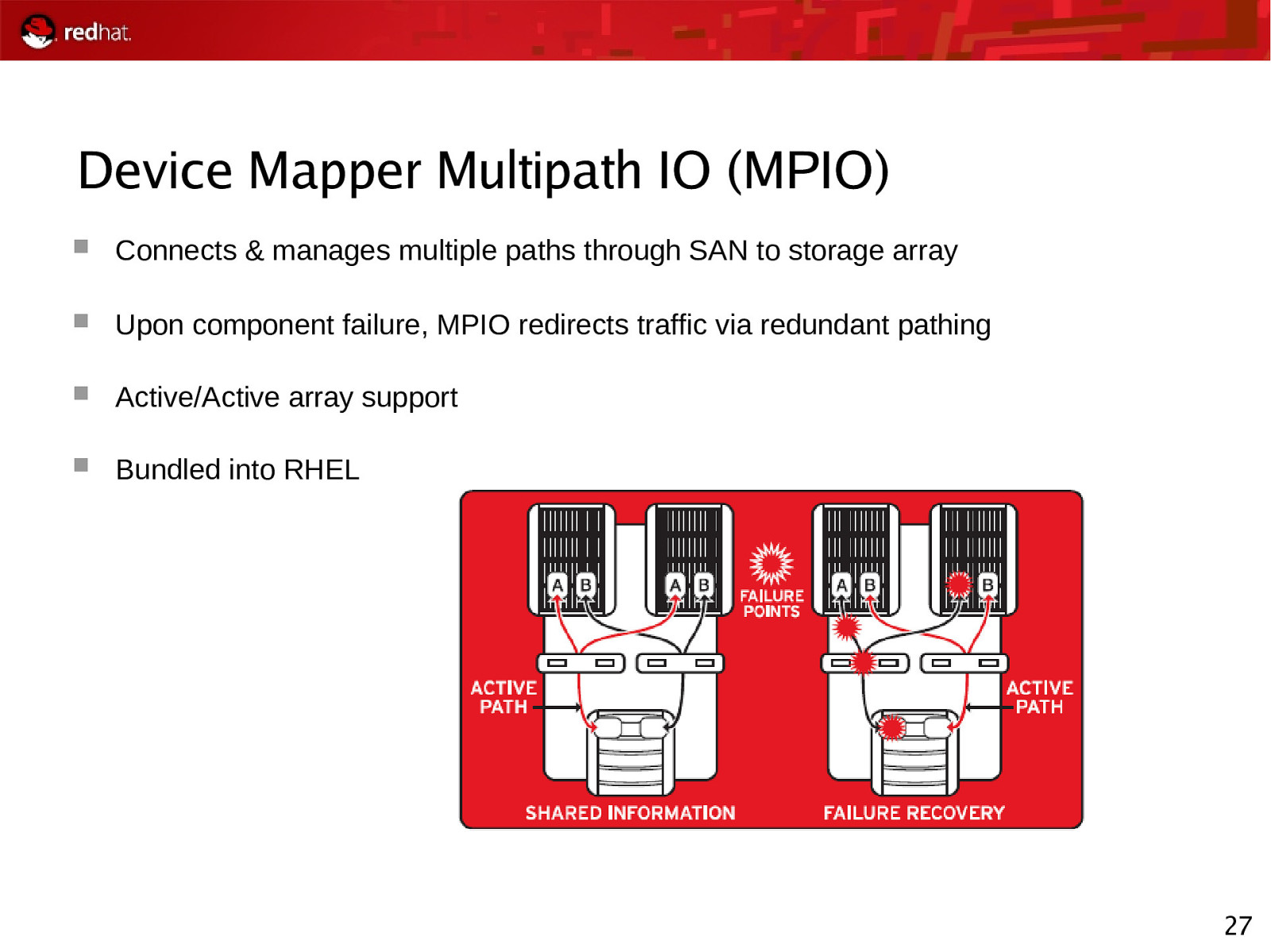
Device Mapper Multipath IO (MPIO) Connects & manages multiple paths through SAN to storage array Upon component failure, MPIO redirects traffic via redundant pathing Active/Active array support Bundled into RHEL 27
Slide 28
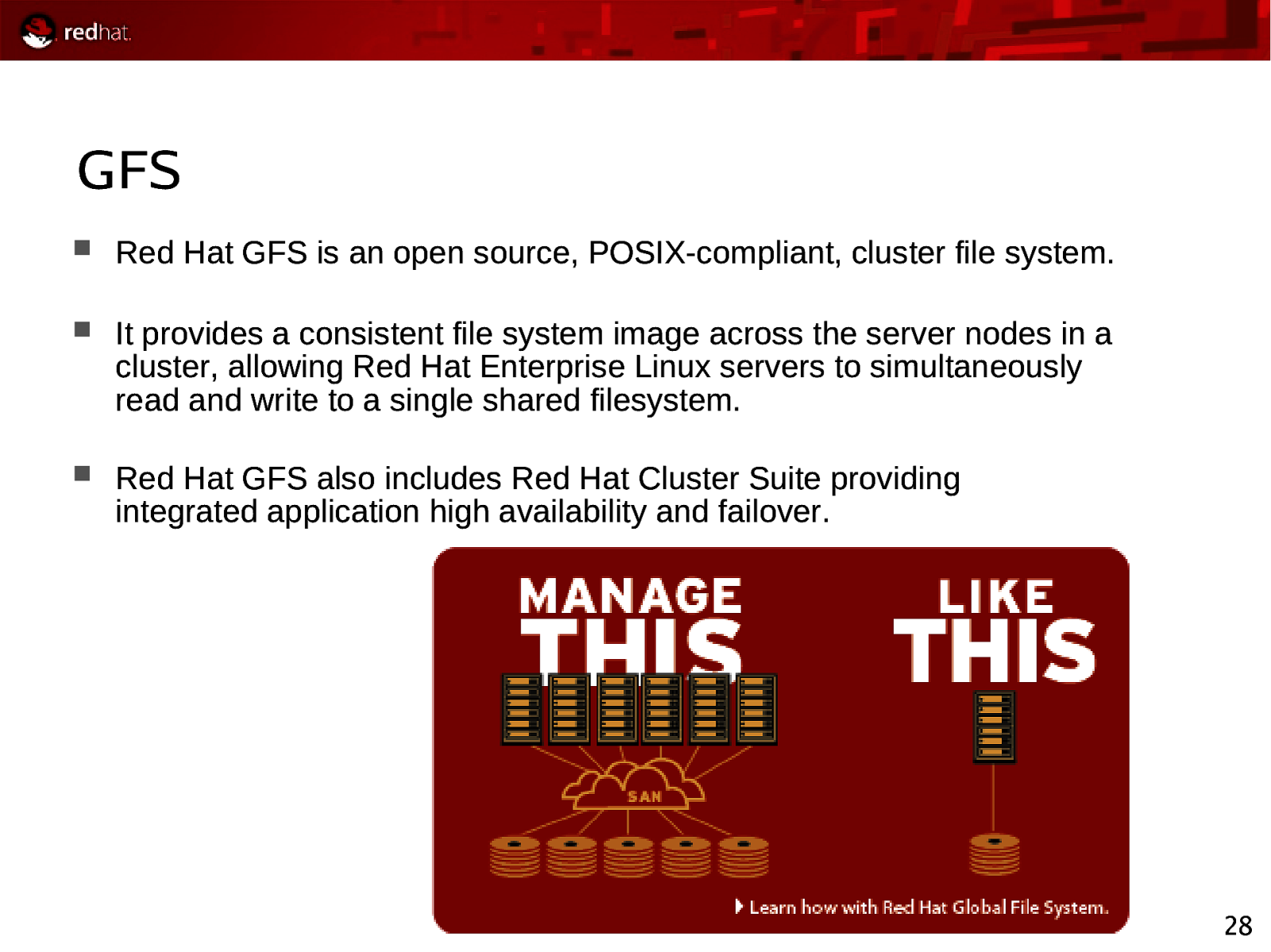
GFS Red Hat GFS is an open source, POSIX-compliant, cluster file system. It provides a consistent file system image across the server nodes in a cluster, allowing Red Hat Enterprise Linux servers to simultaneously read and write to a single shared filesystem. Red Hat GFS also includes Red Hat Cluster Suite providing integrated application high availability and failover. 28
Slide 29

Red Hat SOA Direction - JBoss - MetaMatrix
Slide 30
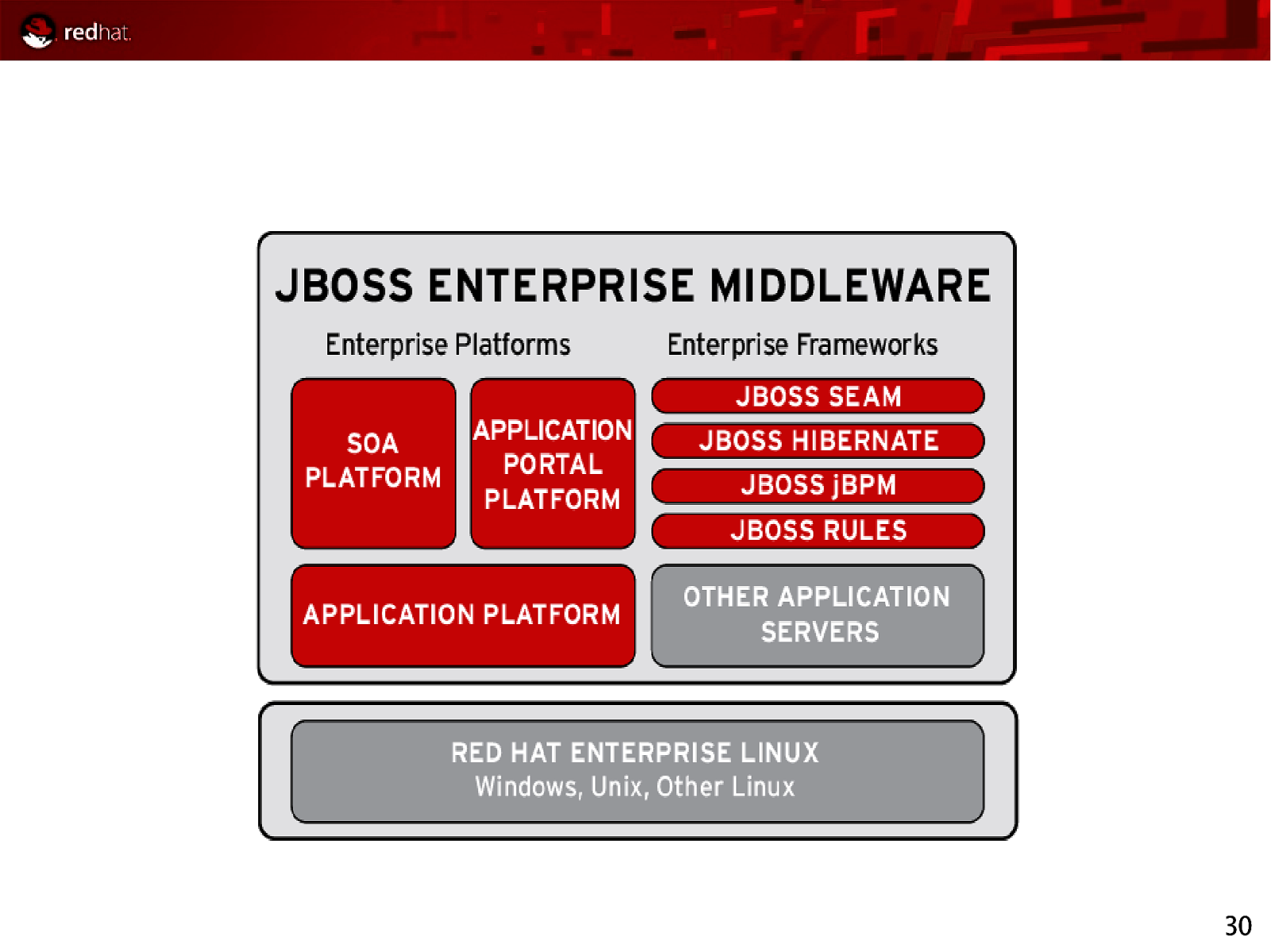
30
Slide 31
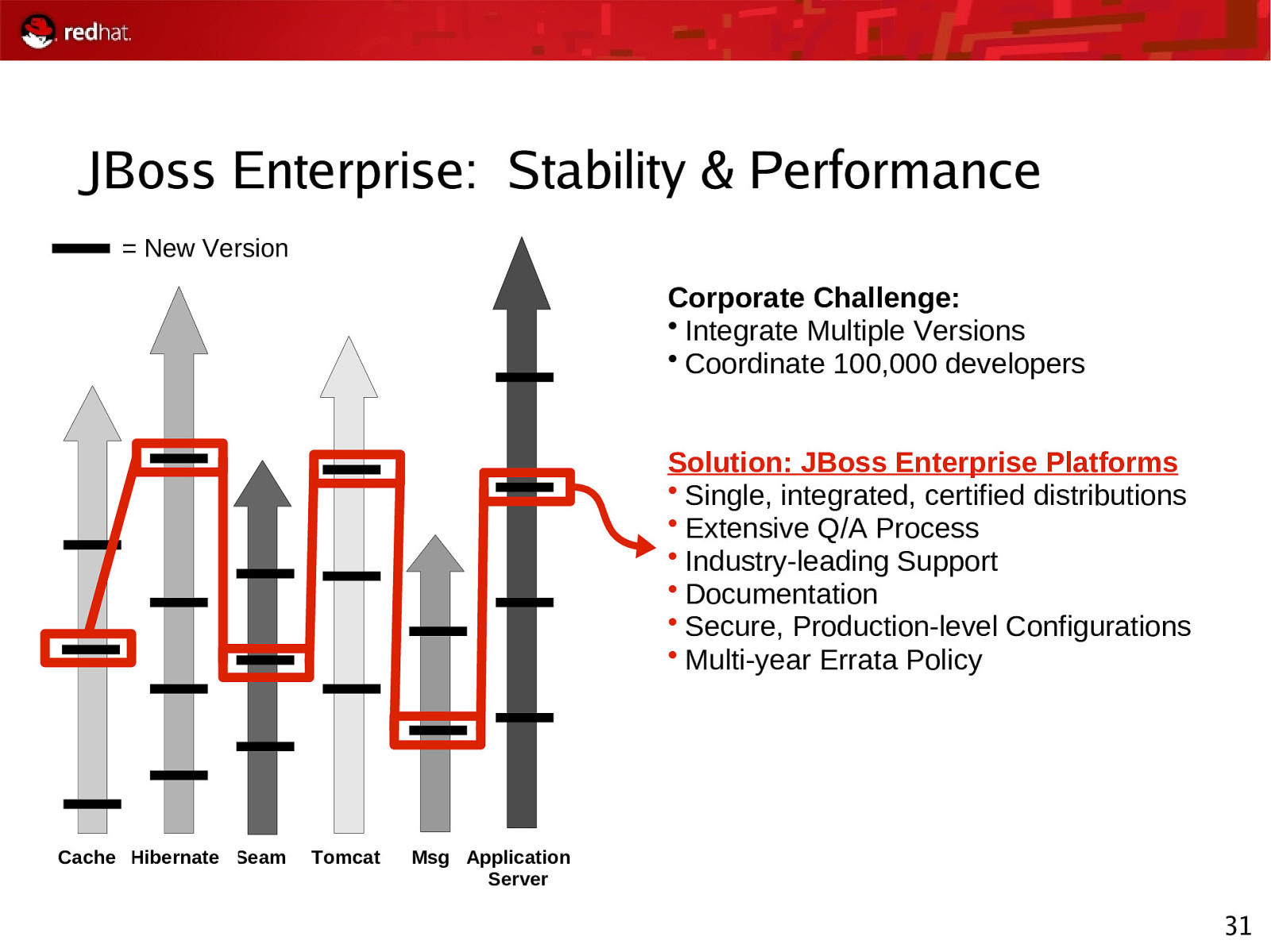
JBoss Enterprise: Stability & Performance = New Version Corporate Challenge: • Integrate Multiple Versions • Coordinate 100,000 developers Solution: JBoss Enterprise Platforms • Single, integrated, certified distributions • Extensive Q/A Process • Industry-leading Support • Documentation • Secure, Production-level Configurations • Multi-year Errata Policy Cache Hibernate Seam Tomcat Msg Application Server 31
Slide 32
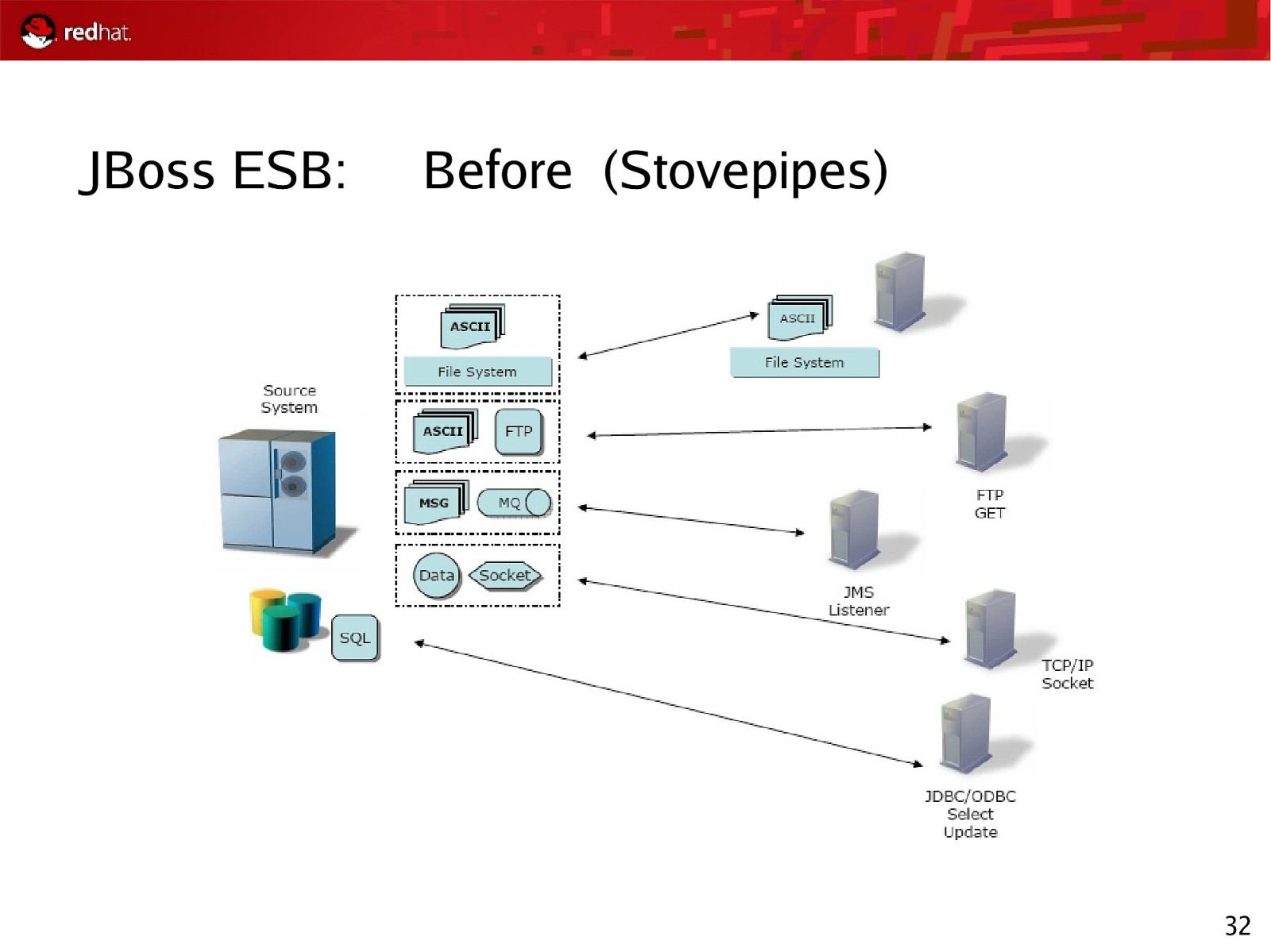
JBoss ESB: Before (Stovepipes) 32
Slide 33
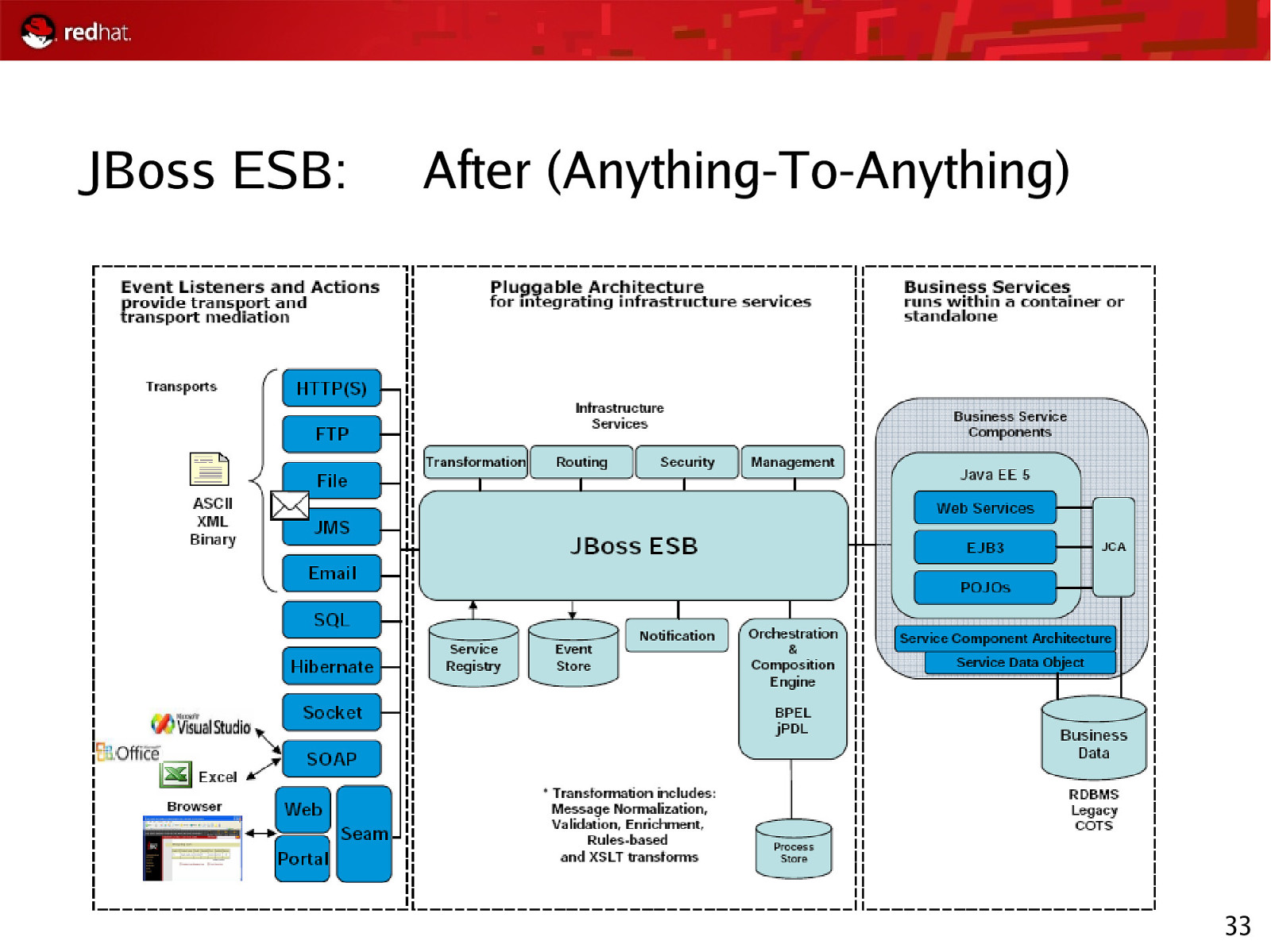
JBoss ESB: After (Anything-To-Anything) 33
Slide 34
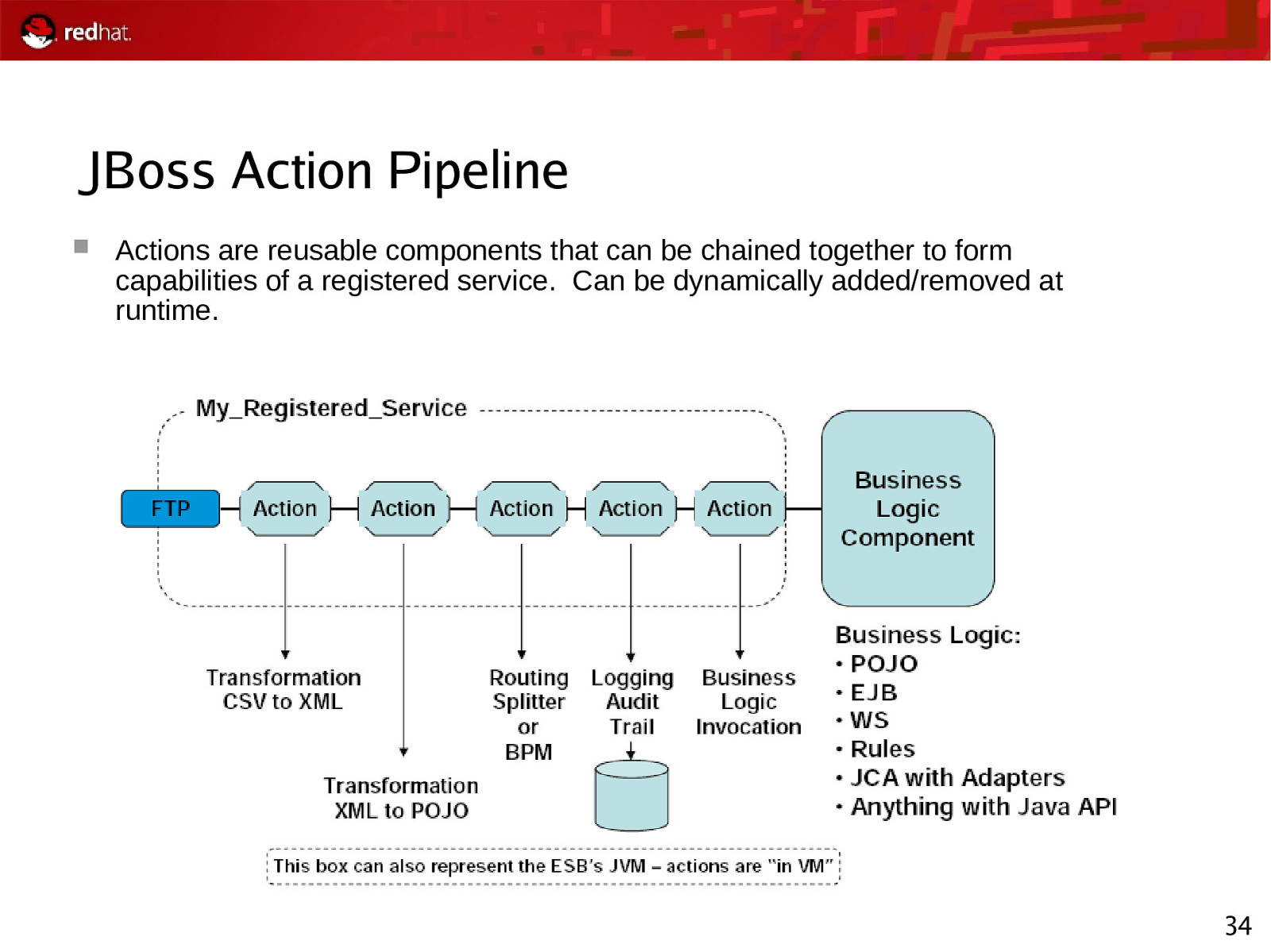
JBoss Action Pipeline Actions are reusable components that can be chained together to form capabilities of a registered service. Can be dynamically added/removed at runtime. 34
Slide 35
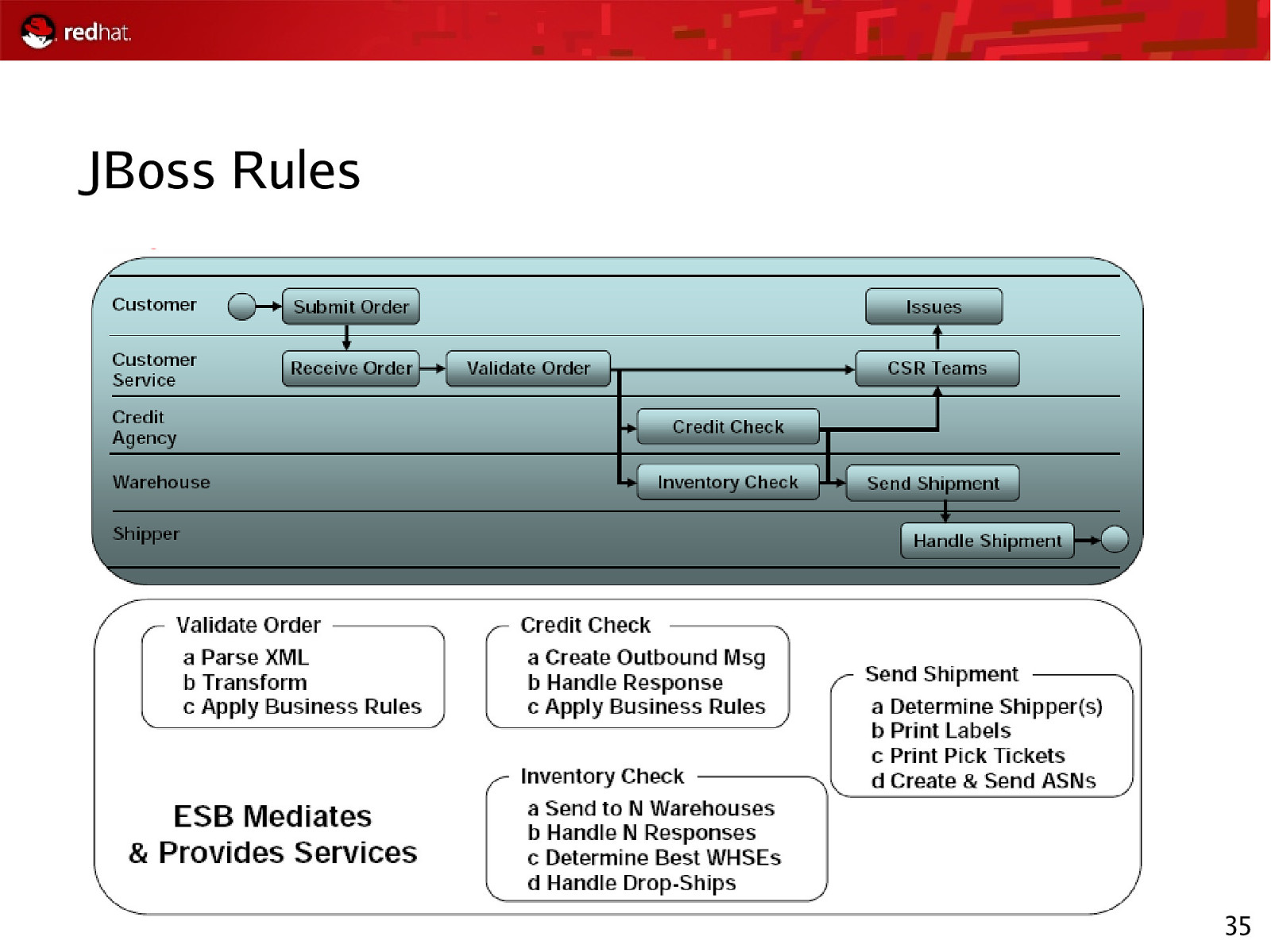
JBoss Rules 35
Slide 36
JBoss Conclusion Open Source makes JBoss SOA happen ESB Hibernate SEAM ESB is a solution for application/process integration ESB is about service intermediation Ask about getting evaluation copies! 36
Slide 37
MetaMatrix Background On-demand access to distributed information Real time integration of diverse data Avoid unnecessary data replication Metadata-Driven Integration in days, not weeks Reduce “long tail” of application maintenance Improved data agility Abstracts data into a “single view” without need to move data between databases Single view of Customer – CRM Single view of Supplier – Supply Chain Single view of Employee – HR Consolidation SOA Enabler Consume/Produce Web Services ……. and still provide support for ODBC, JDBC, and legacy! 37
Slide 38
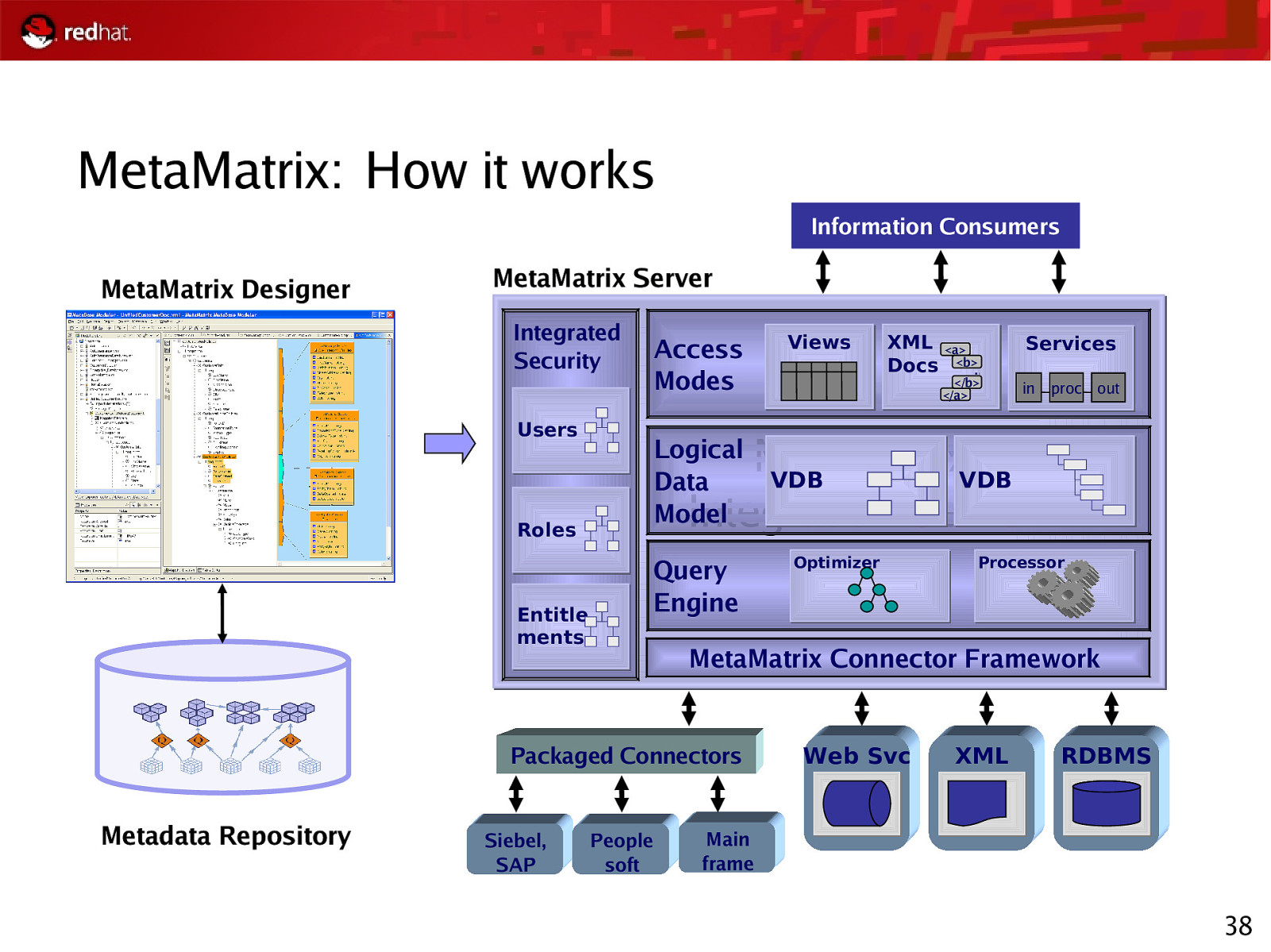
MetaMatrix: How it works Information Consumers MetaMatrix Designer MetaMatrix Server Integrated Security Users Access Modes </b> </a> Services in proc out Integration Server MetaMatrix VDB VDB Integration Server Query Engine Entitle ments Optimizer Processor MetaMatrix Connector Framework Packaged Connectors Siebel, SAP XML <a> Docs <b>… Logical Data Model Roles Metadata Repository Views People soft Web Svc XML RDBMS Main frame 38
Slide 39
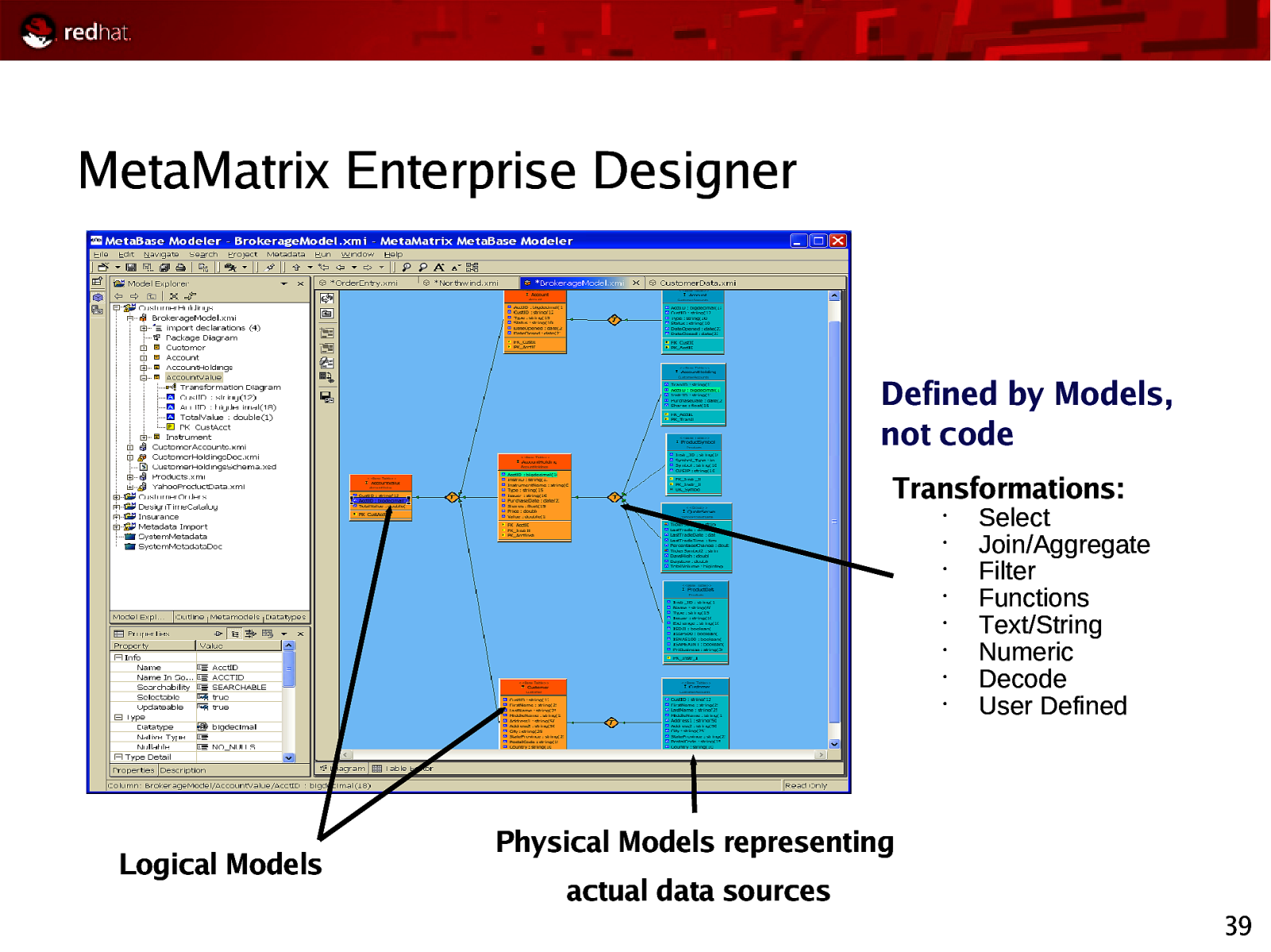
MetaMatrix Enterprise Designer Defined by Models, not code Transformations: • • • • • • • • Logical Models Select Join/Aggregate Filter Functions Text/String Numeric Decode User Defined Physical Models representing actual data sources 39
Slide 40

Red Hat Identity Management - Directory Server - Certificate Server
Slide 41
Red Hat Authentication History On December 8, 2004, Red Hat acquired assets from AOL’s Netscape Security Solutions business unit, including currently shipping products: Netscape Certificate Management System (Red Hat Certificate System) Netscape Directory Server (Red Hat Directory Server) Acquisition of JBoss in June 2006 now provides an extension for the identity management technologies into the Application and Web Services space. 41
Slide 42
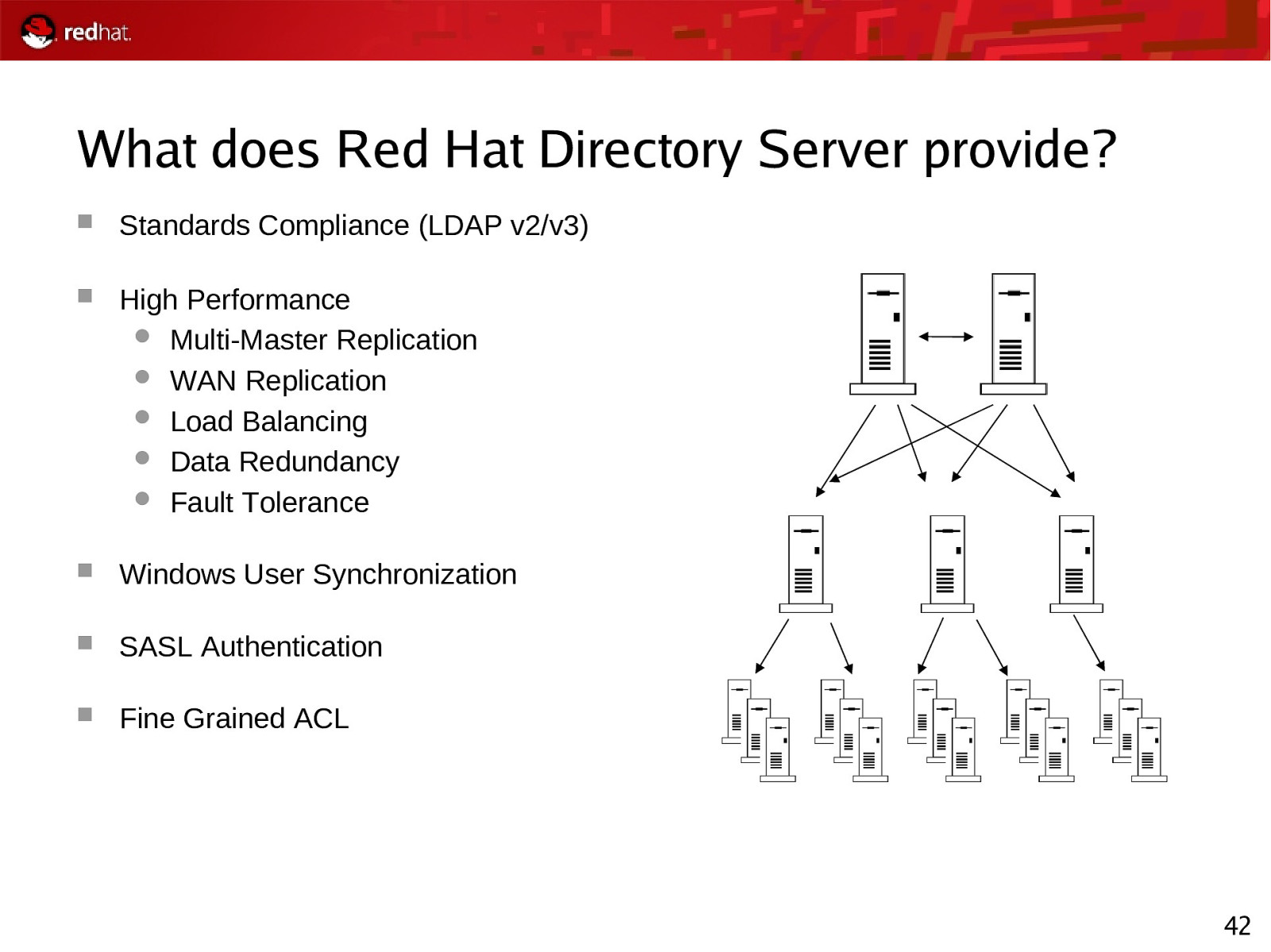
What does Red Hat Directory Server provide? Standards Compliance (LDAP v2/v3) High Performance Multi-Master Replication WAN Replication Load Balancing Data Redundancy Fault Tolerance Windows User Synchronization SASL Authentication Fine Grained ACL 42
Slide 43
What does Red Hat Certificate System provide? Standards Based PKI Unmatched Scalability 14,000 certificate issuances/hour 12M certificates issued < 35 days Largest public CRL: 1.2M Government Support FIPS-140 Certified EAL4/CIMC Protection Profile Replaces Passwords, Single Sign-On Smart Card Support Integrated with RHEL & Windows 43
Slide 44
Certificate Server Scalability 25M+ Certificates issued from the DoD PKI CAs, 1999-Present 3.5M – 4M “active” smart cards, most with 3 certificates Issuing lifetime of individual CAs governed by the size of the database managed by the CA As number of certificates issued increased, number of revocations increased, resulting in large CRLs CMS 4.2 and CMS 6.1 on Solaris – approximately 1.5M issued certificates per CA Red Hat CS 7.1 on Linux [deployed in 2006] – DT&E Testing prior to fielding demonstrated 3M issued certificates per CA with large CRL 44
Slide 45
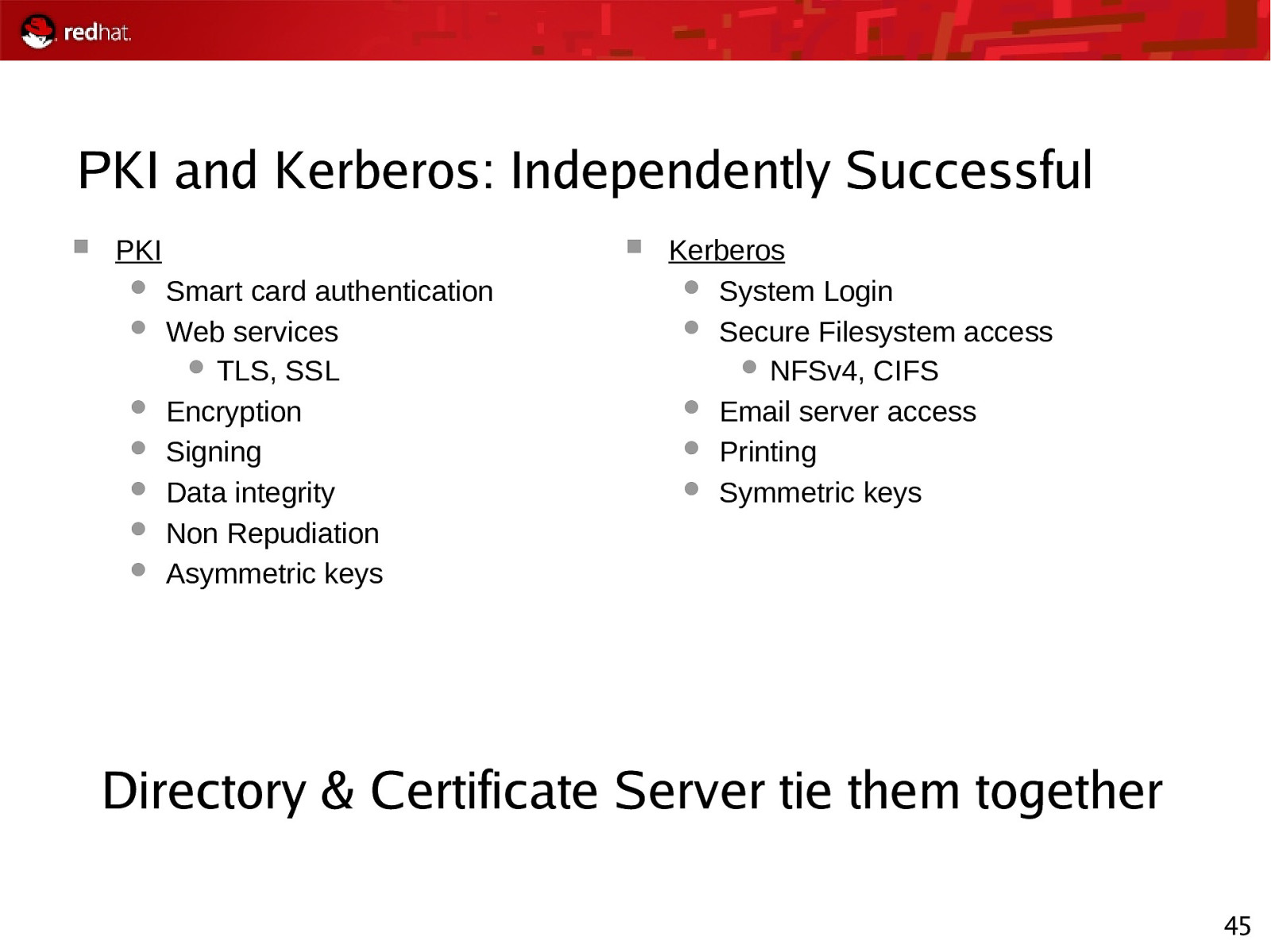
PKI and Kerberos: Independently Successful PKI Smart card authentication Web services TLS, SSL Encryption Signing Data integrity Non Repudiation Asymmetric keys Kerberos System Login Secure Filesystem access NFSv4, CIFS Email server access Printing Symmetric keys Directory & Certificate Server tie them together 45
Slide 46

Red Hat Emerging Technologies - Virtualization Updates - MRG/Realtime - freeIPA
Slide 47
Trusted Platform Module Planned for inclusion in next minor release of RHEL (5.2) What functionality would you like to see? What functionality would you use? 47
Slide 48
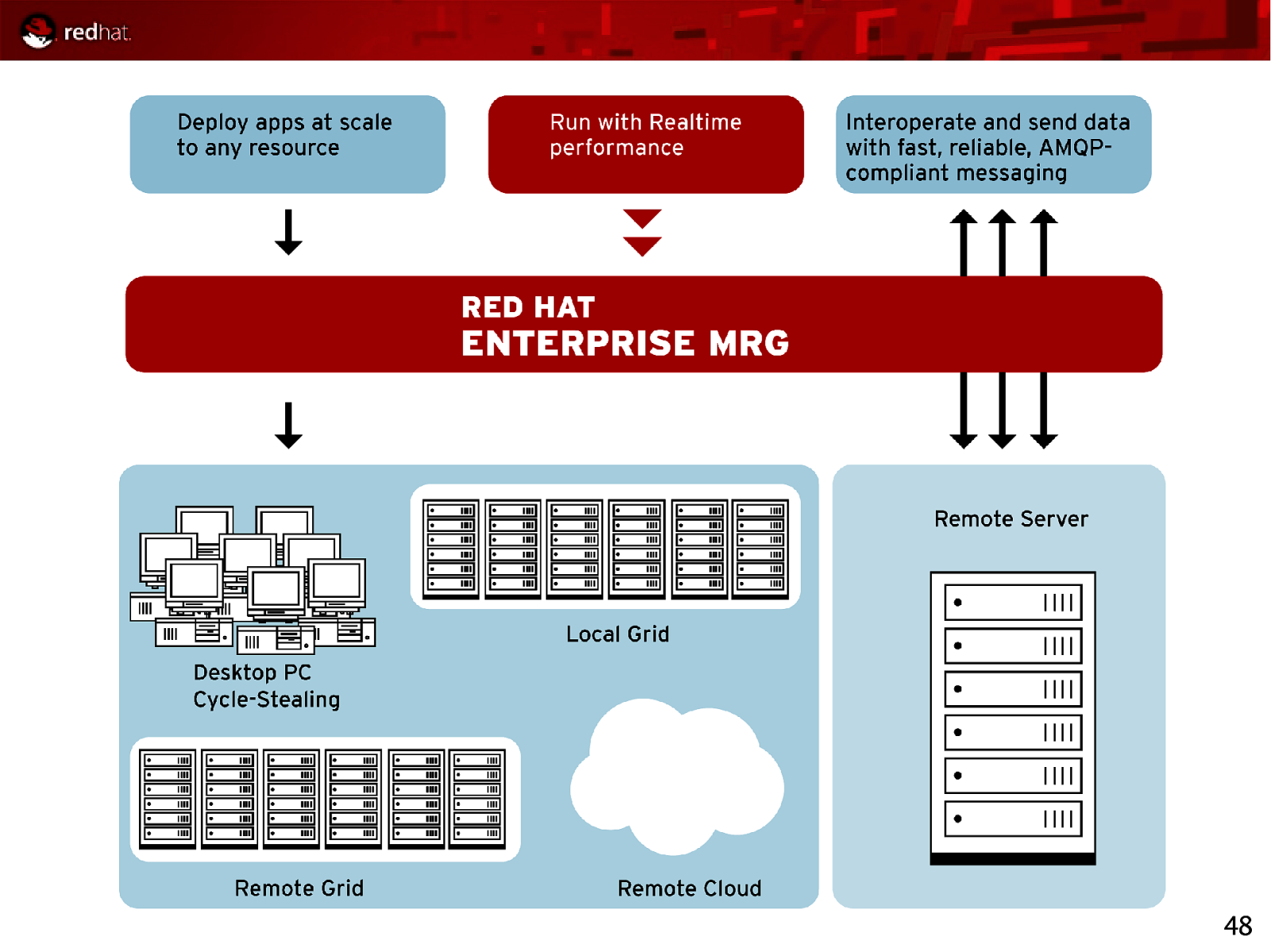
48
Slide 49
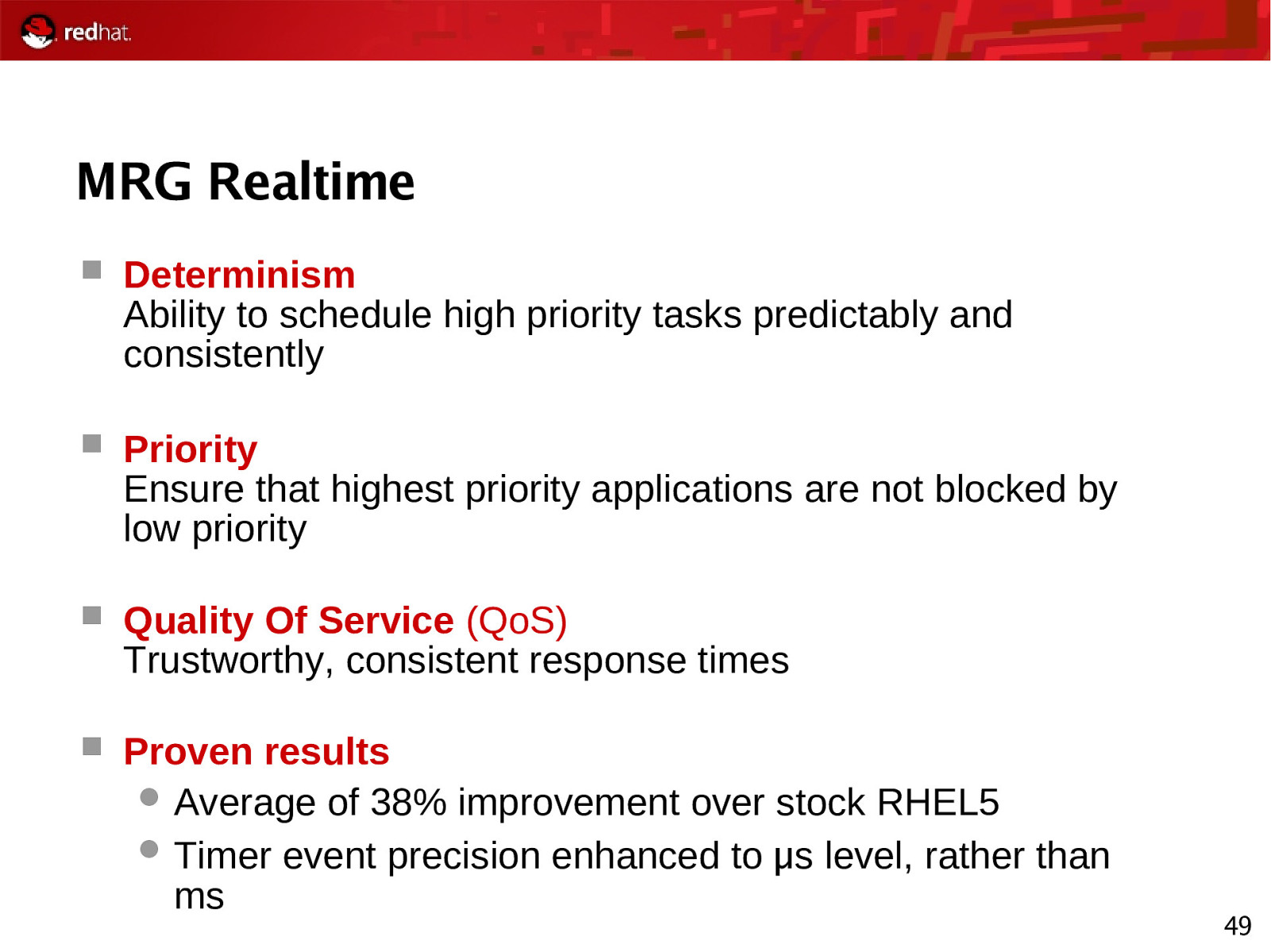
MRG Realtime Determinism Ability to schedule high priority tasks predictably and consistently Priority Ensure that highest priority applications are not blocked by low priority Quality Of Service (QoS) Trustworthy, consistent response times Proven results Average of 38% improvement over stock RHEL5 Timer event precision enhanced to μ s level, rather than ms 49
Slide 50
MRG: Messaging Provides messaging that is up to 100-fold faster than before Spans fast messaging, reliable messaging, large-file messaging Implements AMQP, the industry’s first open messaging standard, for unprecedented interoperability that is cross-language, cross-platform, multivendor, spans hardware and software, and extends down to the wire level Uses Linux-specific optimizations to achieve optimal performance on Red Hat Enterprise Linux and MRG Realtime ● Takes advantage of RHEL clustering, IO, kernel, and more ● Includes new high-performance AIO Journal for durable messaging ● Provides native infiniband support for transient messaging 50
Slide 51

About AMQP AMQP is an open specification for messaging ● It is a complete specification ● Anyone may use the AMQP specification to create useful implementations without being charged for the IP rights to do so AMQP aims to be technology and language-neutral ● Available in C, C++, Java, JMS, .NET, C#, Ruby, Python, etc. ● Requires IP, and can be used with TCP, UDP, SCTP, Infiniband, etc. Products complying with AMQP are inter-operable ● AMQP is a Wire-Level protocol based on the ubiquitous IP ● Wire-level compatibility means it can be embedded in the network ● Applications written to Product X will plug into servers running Product Y Red Hat is a founding member of the AMQP Working Group 51
Slide 52
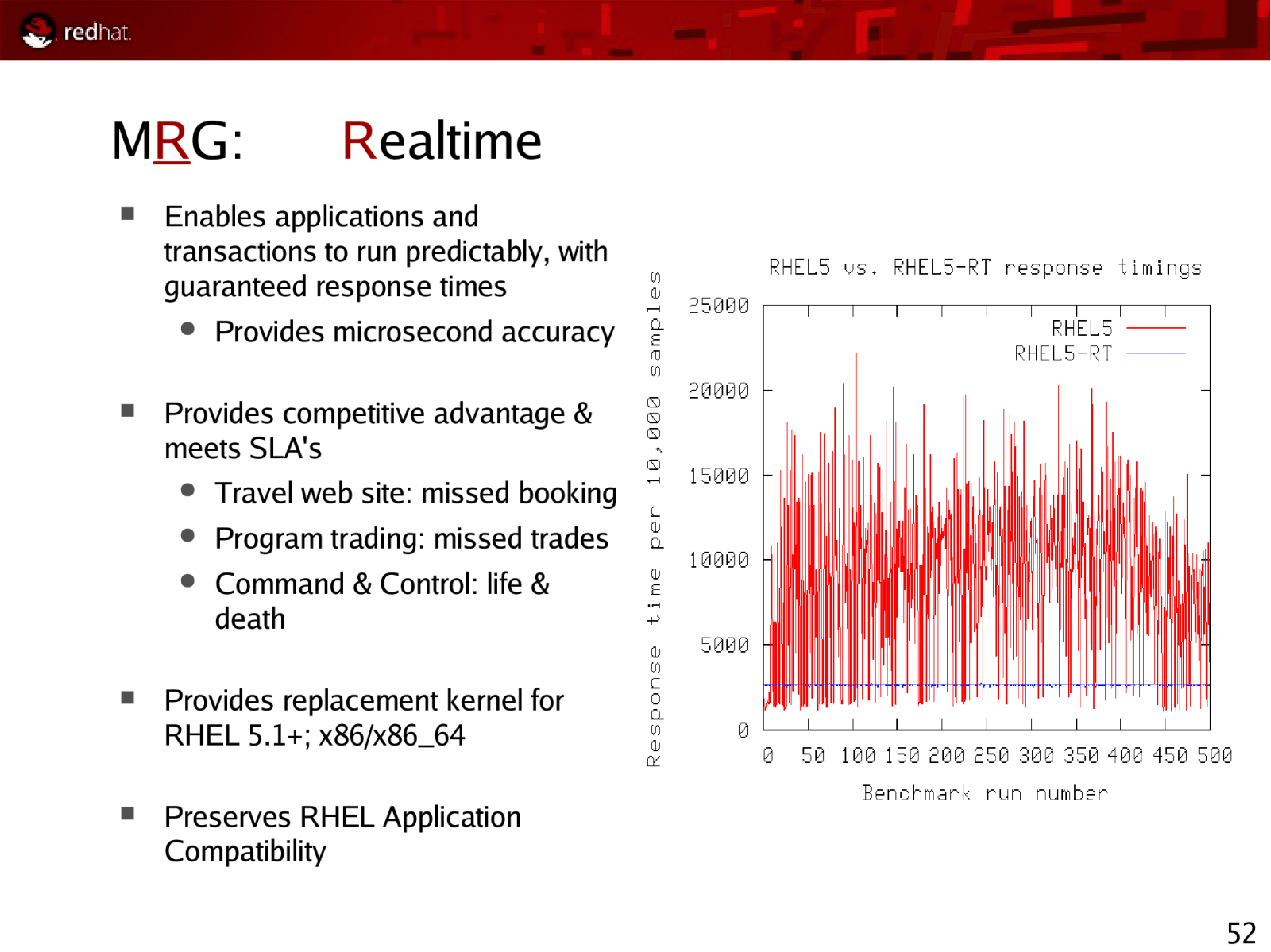
MRG: Enables applications and transactions to run predictably, with guaranteed response times ● Realtime Provides microsecond accuracy Provides competitive advantage & meets SLA’s ● Travel web site: missed booking ● Program trading: missed trades ● Command & Control: life & death Provides replacement kernel for RHEL 5.1+; x86/x86_64 Preserves RHEL Application Compatibility 52
Slide 53
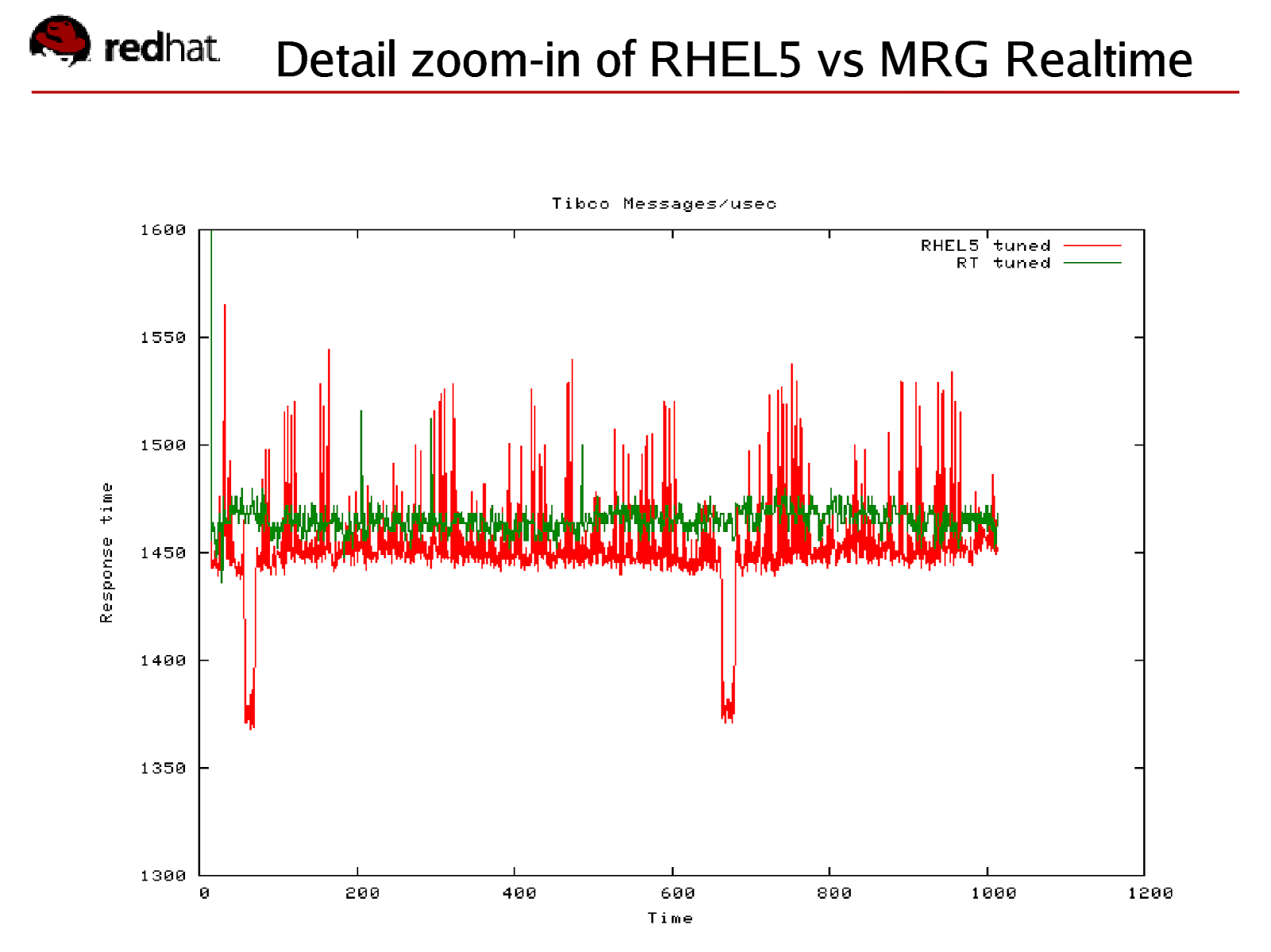
Detail zoom-in of RHEL5 vs MRG Realtime Red Hat Confidential
Slide 54
MRG: Realtime Tools MRG includes a new MRG Realtime Latency Tracer ● Runtime trace capture of longest latency codepaths – both kernel and application. Peak detector ● Selectable triggers for threshold tracing ● Detailed kernel profiles based on latency triggers Existing standard RHEL5 based performance monitoring tools remain relevant ● Gdb, OProfile Frysk – source level debuggers & profiler ● SystemTap, kprobe – kernel event tracing and dynamic data collection ● kexec/kdump standard kernel dump/save core capabilities 54
Slide 55
MRG: Realtime Breakthroughs Red Hat engineers succeed at mainstream acceptance ● Methodical multi-year implementation ● Incrementally added features beneficial to all use cases ● Iteratively worked to cooperatively build an inclusive realtime community MRG Realtime is COTS (Commercial Off The Shelf) operating system ● Standard RHEL5.1 OS ● Replacement kernel Integrated with distributed high speed messaging & grid scheduler ● MRG Messaging, MRG Grid 55
Slide 56
MRG: Grid Brings advantages of scale-out and flexible deployment to any application Delivers better asset utilization, allowing applications to to take advantage of all available computing resources Dynamically provisions additional peak capacity for “Christmas Rush”-like situations Executes across multiple platforms and in virtual machines Provides seamless and flexible High Throughput Computing (HTC) and High Performance Computing (HPC) across Local grids Remote grids Remote clouds (Amazon EC2) Cycle-stealing from desktop PCs 56
Slide 57
MRG: Grid based off Condor MRG Grid is based on the Condor Project created and hosted by the University of Wisconsin, Madison Red Hat and the University of Wisconsin have signed a strategic partnership around Condor: University of Wisconsin makes Condor source code available under OSIapproved open source license Red Hat & University of Wisconsin jointly fund and staff Condor development on-campus at the University of Wisconsin Red Hat and the University of Wisconsin’s partnership will: Add enhanced enterprise features, management, and supportability to Condor and MRG Grid Add High Throughput Computing capabilities to Linux 57
Slide 58
Red Hat Enterprise MRG Availability MRG Announcement & Beta Launch: December 2007 Public beta MRG v1.0: Early 2008 RHEL-only support for MRG Messaging broker MRG Grid Technology Preview MRG v1.1: Late 2008 Multi-platform support for MRG Messaging Java-based broker AMQP support updated to newly available AMQP version (1.0) MRG Grid support available 58
Slide 59
Additional Information: http://www.redhat.com/mrg/ 59
Slide 60
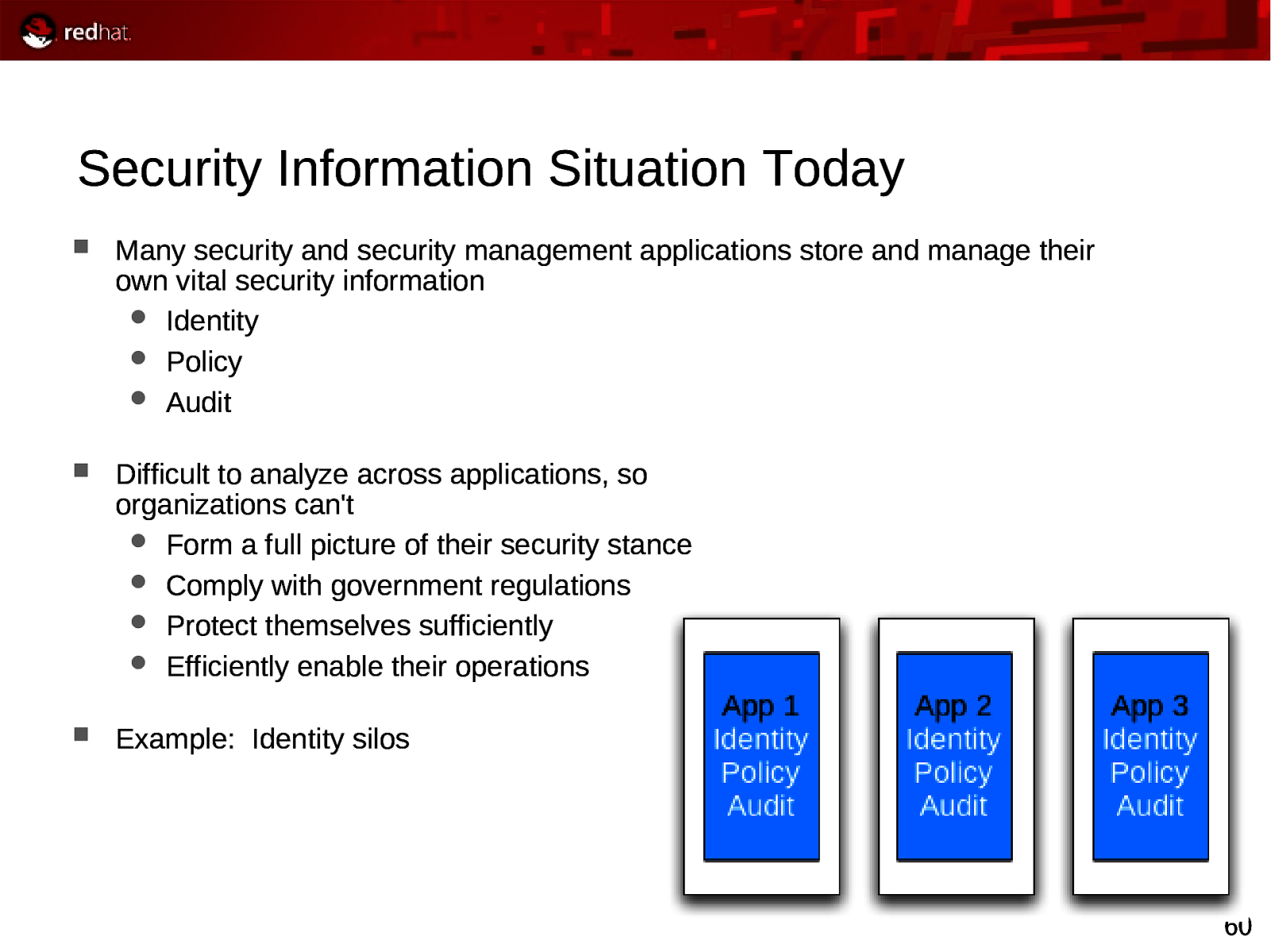
Security Information Situation Today Many security and security management applications store and manage their own vital security information Identity Policy Audit Difficult to analyze across applications, so organizations can’t Form a full picture of their security stance Comply with government regulations Protect themselves sufficiently Efficiently enable their operations Example: Identity silos 60
Slide 61
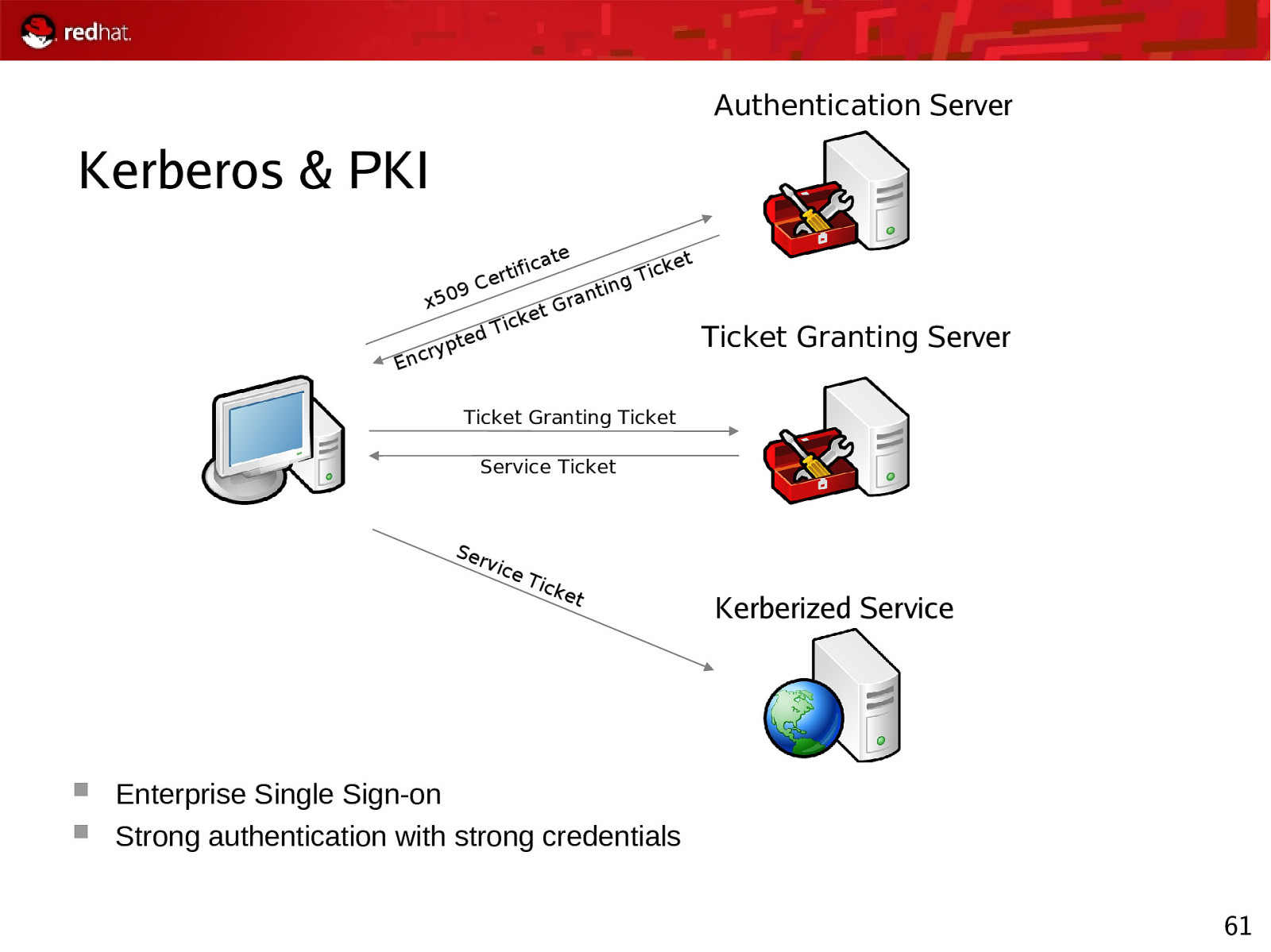
Authentication Server Kerberos & PKI ate x50 9C d pte ry Enc fic erti t icke T g tin ran G et Tick Ticket Granting Server Ticket Granting Ticket Service Ticket Ser v ice Tic ket Kerberized Service Enterprise Single Sign-on Strong authentication with strong credentials 61
Slide 62
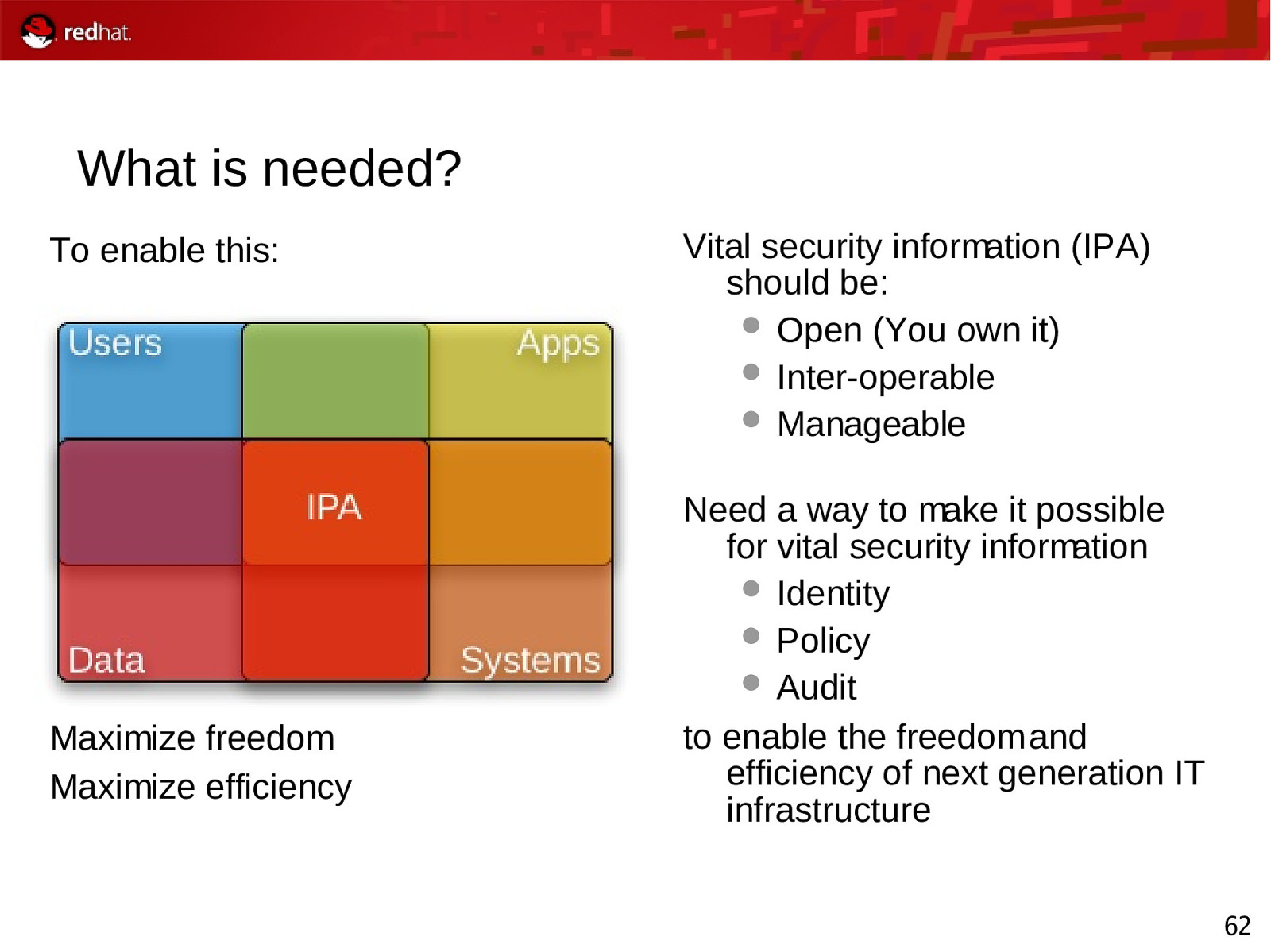
What is needed? To enable this: Maximize freedom Maximize efficiency Vital security information (IPA) should be: Open (You own it) Inter-operable Manageable Need a way to make it possible for vital security information Identity Policy Audit to enable the freedom and efficiency of next generation IT infrastructure 62
Slide 63
Project Open Source www.freeipa.org Started and contributed to by Red Hat Open to all IPA = Identity, Policy, Audit Big vision Start with centralized user identity management for UNIX/Linux Add robust, shared sense of machine, service and data identity Provide centrally managed admin access control for UNIX/Linux Give ability to externalize policy and add to it easily Add centralized audit With this you can enable flexible cross-enterprise policy and rational audit 63
Slide 64
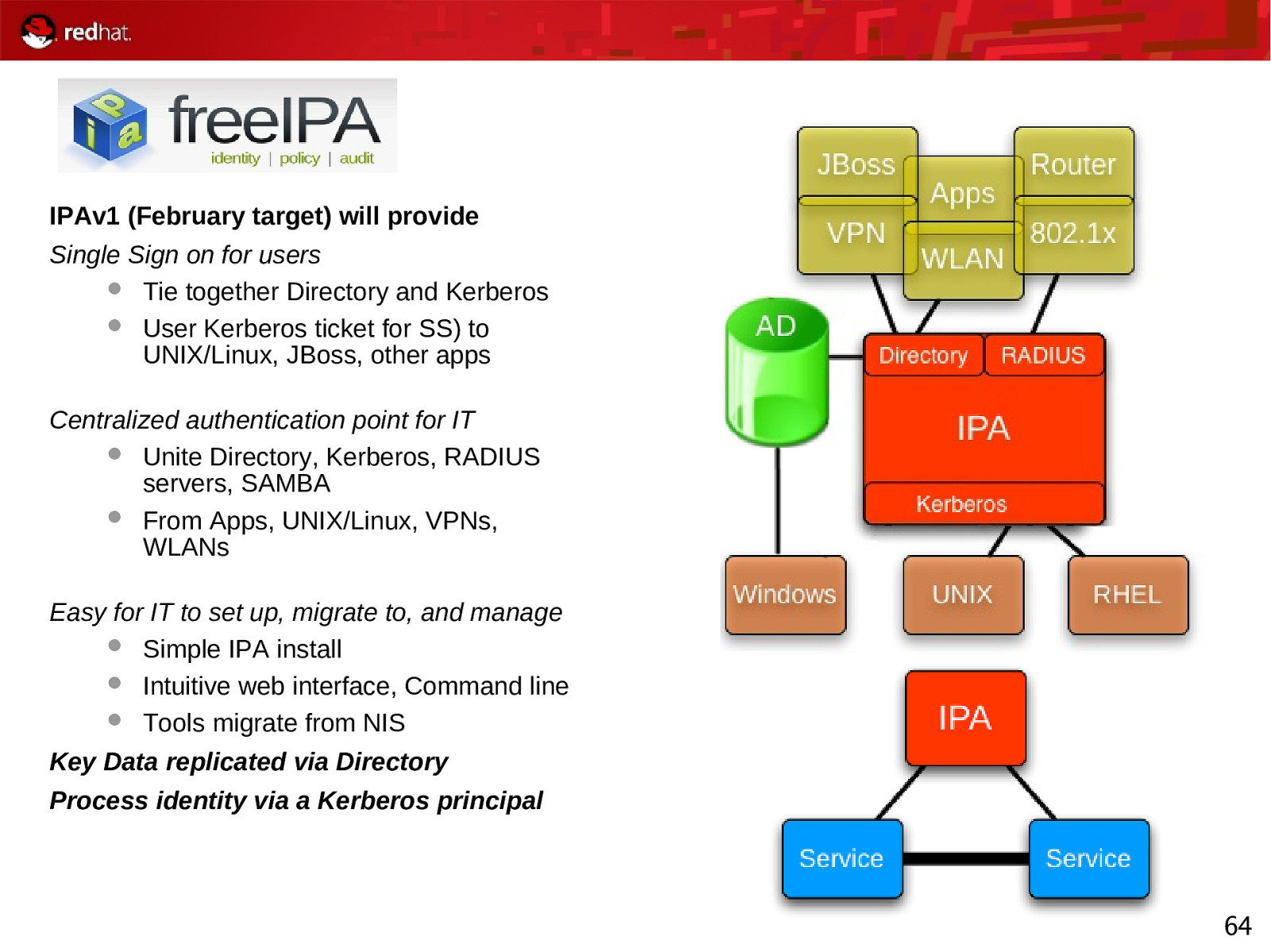
IPAv1 (February target) will provide Single Sign on for users Tie together Directory and Kerberos User Kerberos ticket for SS) to UNIX/Linux, JBoss, other apps Centralized authentication point for IT Unite Directory, Kerberos, RADIUS servers, SAMBA From Apps, UNIX/Linux, VPNs, WLANs Easy for IT to set up, migrate to, and manage Simple IPA install Intuitive web interface, Command line Tools migrate from NIS Key Data replicated via Directory Process identity via a Kerberos principal 64
Slide 65
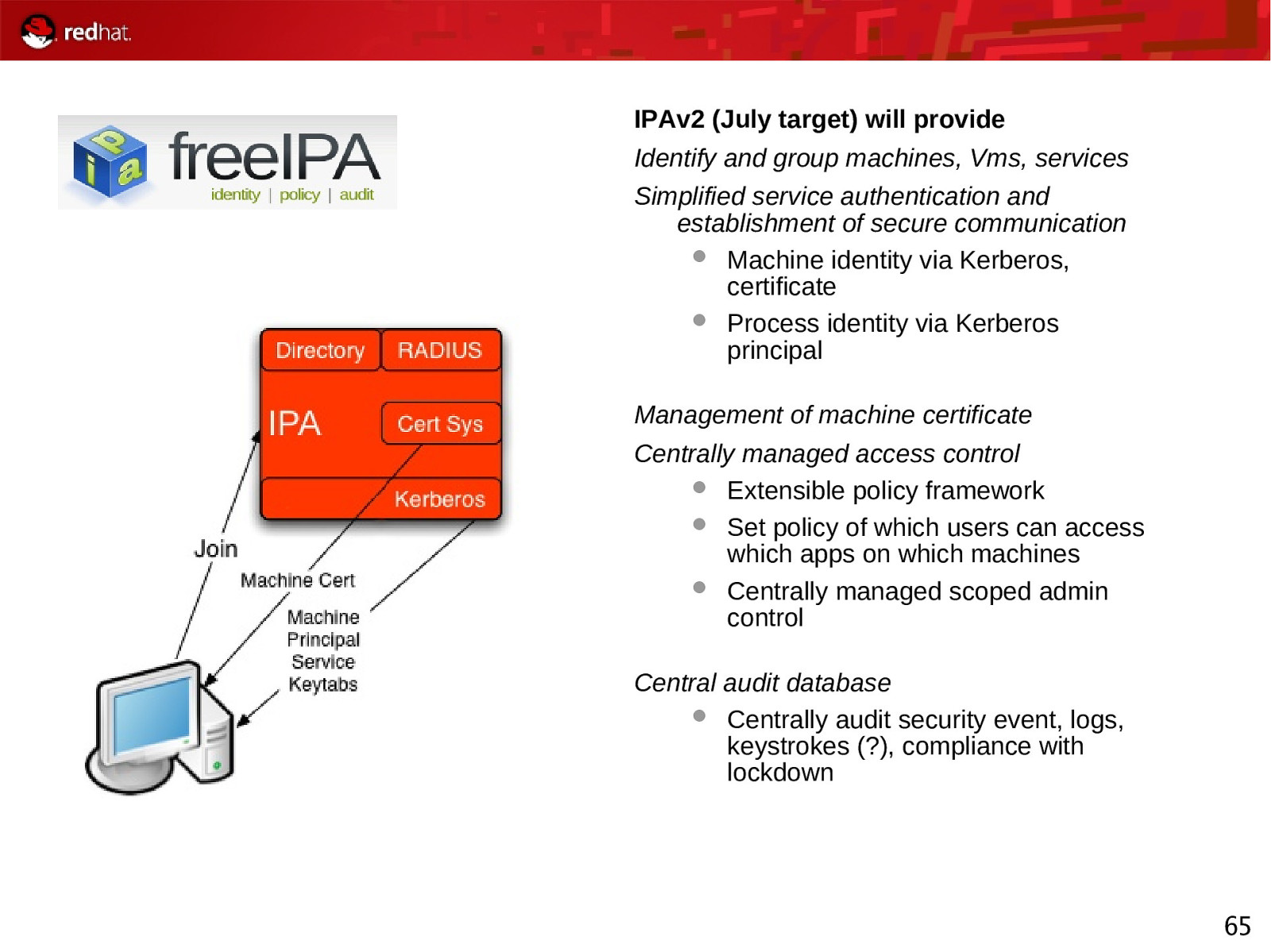
IPAv2 (July target) will provide Identify and group machines, Vms, services Simplified service authentication and establishment of secure communication Machine identity via Kerberos, certificate Process identity via Kerberos principal Management of machine certificate Centrally managed access control Extensible policy framework Set policy of which users can access which apps on which machines Centrally managed scoped admin control Central audit database Centrally audit security event, logs, keystrokes (?), compliance with lockdown 65
Slide 66

Open Discussion